In today’s interconnected world, data security is critical. With the rise of cyberattacks, businesses are increasingly vulnerable to SQL injection (SQLi) attacks and data breaches.
These incidents can result in significant financial losses, reputational damage, and legal consequences. However, with the right measures in place, businesses can prevent such attacks and protect sensitive information from malicious actors.
SQL injection is a type of cyberattack that targets the database layer of an application. It exploits flaws in SQL queries, enabling attackers to manipulate a database and access, alter, or delete sensitive data. Data breaches, on the other hand, often occur due to weak security protocols or unauthorized access to private information.
The good news is that by implementing a few best practices, businesses can significantly reduce the risk of SQL injection and data breaches.
In this article, we’ll explore 10 tips to prevent SQL injection and data breaches, which will help safeguard your business from these pervasive threats.
Introduction to SQL Injection and Data Breaches
SQL injection (SQLi) is one of the most common and dangerous forms of attack. It occurs when an attacker inserts or manipulates malicious SQL code into a query, often through an input field (e.g., a login form, search box, or feedback form). If the application does not properly validate and sanitize user inputs, the malicious code gets executed, allowing attackers to manipulate the database.
SQL injection can result in:
- Data theft: Attackers can access confidential information such as customer details, passwords, or financial data.
- Data destruction: Attackers can delete or corrupt data, rendering a database unusable.
- Privilege escalation: Attackers can gain administrative rights and perform unauthorized actions.
- Website defacement or denial of service (DoS): An attacker may take down a site, preventing legitimate users from accessing it.
Real-life example: In 2009, the well-known social networking site Twitter was compromised via a SQL injection attack, which allowed hackers to steal login credentials of millions of accounts, exposing the vulnerability in their web application.
Understanding Data Breaches
A data breach occurs when unauthorized access is gained to sensitive or protected data. This could happen due to hacking, accidental exposure, weak password management, or even physical theft of devices containing critical information.
Data breaches can have a far-reaching impact, including:
- Legal consequences: Many countries have stringent data protection regulations, and failing to secure data could result in hefty fines (e.g., GDPR, CCPA).
- Financial losses: Businesses may face lawsuits, penalties, and revenue loss due to diminished customer trust.
- Brand damage: A breach can tarnish a company’s reputation, leading to loss of customers and market position.
Case Study: In 2017, Equifax, a credit reporting agency, suffered a massive data breach, affecting approximately 147 million individuals. Attackers exploited a vulnerability in a web application framework (Apache Struts) to access sensitive financial data, resulting in a public outcry and legal settlements exceeding $700 million.
Why Preventing SQL Injection and Data Breaches is Crucial?
When sensitive data such as personal information, payment details, or intellectual property is compromised, the impact on a business can be devastating. Beyond immediate financial losses, breaches and SQL injections can cause irreparable reputational damage. Trust, once lost, is hard to regain, especially in today’s competitive market where customers prioritize security.
The following table illustrates the potential consequences of a data breach:
| Consequence | Impact | Example |
| Financial Loss | Penalties, lawsuit settlements, and lost revenue | Equifax breach: $700M+ in settlements |
| Reputation Damage | Loss of customer trust and market position | Target breach: customer churn |
| Legal Penalties | Fines and legal action due to non-compliance | GDPR: €20M fine for data violations |
Protecting User Privacy and Trust
User privacy is a cornerstone of maintaining a strong relationship with customers. Businesses that fail to safeguard sensitive data are at risk of losing customer loyalty. Customer trust is invaluable, and any breach of this trust can lead to customers abandoning your service in favor of a competitor with better security measures in place.
Trends to Watch:
- 80% of consumers say that they would stop doing business with a company if it experienced a breach that compromised their personal information (source: IBM).
- 67% of data breaches in 2022 involved compromised passwords and credentials (source: Verizon).
10 Essential Tips to Prevent SQL Injection and Data Breaches
Let’s take a look.
Tip #1: Use Parameterized Queries
Parameterized queries are one of the most effective ways to prevent SQL injection. Instead of inserting raw user input directly into a query string, parameterized queries treat the user input as a value rather than executable code. This significantly reduces the risk of SQL injection.
By using parameterized queries, you ensure that inputs are safely handled, as the database will never confuse user input with part of the SQL code.
Example: In Python using MySQLdb
python
Copy code
cursor.execute(“SELECT * FROM users WHERE email = %s”, (email,))
The %s placeholder ensures the email input is treated as a parameter, not executable SQL code.
| Method | Benefit | Example |
| Parameterized Queries | Protects against SQL injection by treating user inputs as data | SELECT * FROM users WHERE email = %s |
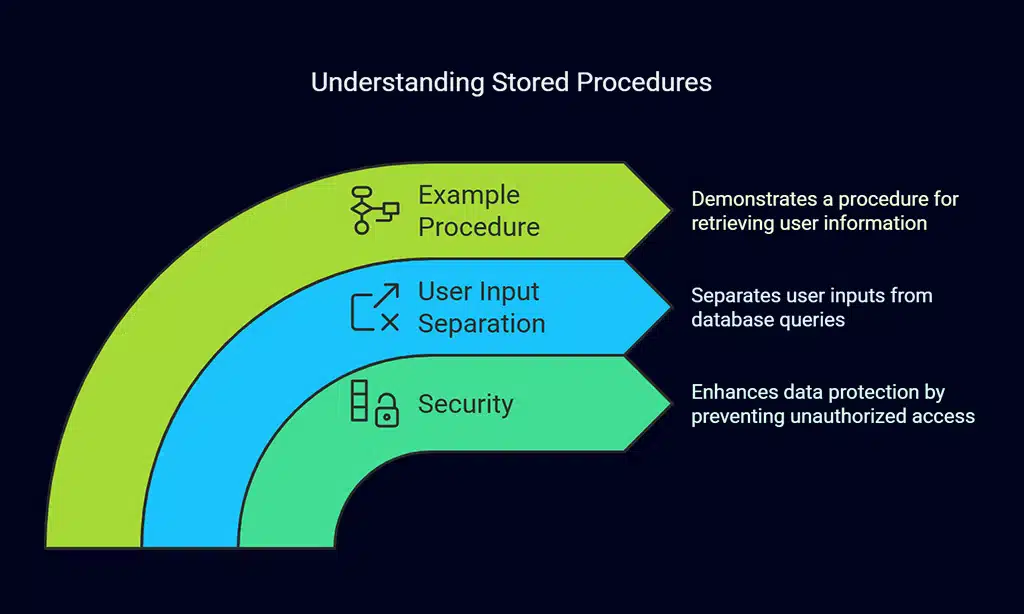
Tip #2: Employ Stored Procedures
Stored procedures are precompiled SQL statements that are stored and executed within the database. They allow businesses to control how data is queried, reducing the possibility of unauthorized SQL code execution. By using stored procedures, you separate user inputs from database queries, enhancing security.
Example: A stored procedure that retrieves a user’s information:
sql
Copy code
CREATE PROCEDURE GetUserInfo(IN user_email VARCHAR(255))
BEGIN
SELECT * FROM users WHERE email = user_email;
END;
Stored procedures also improve performance by reducing the need to recompile SQL queries.
Tip #3: Validate and Sanitize User Inputs
Input validation and sanitization should be a fundamental part of your security strategy. Always assume that user input could be malicious. By validating input types (e.g., expecting a number or email) and sanitizing inputs (e.g., removing special characters), you can significantly reduce the risk of SQL injection attacks.
Best Practices:
- Use whitelisting (accept only known safe inputs) rather than blacklisting (blocking known harmful inputs).
- For example, an email address field should only accept email formats, not HTML or JavaScript.
Example Validation:
python
Copy code
import re
email = input(“Enter your email: “)
if re.match(r”[^@]+@[^@]+\.[^@]+”, email):
print(“Valid email!”)
else:
print(“Invalid email!”)
| Technique | Benefit | Example |
| Input Validation | Ensures only valid, safe data is accepted | Whitelist format: Only alphanumeric characters |
| Input Sanitization | Removes or escapes harmful characters | Remove dangerous characters like quotes or semicolons |
Tip #4: Implement the Least Privilege Principle
The least privilege principle dictates that users, applications, and processes should have only the minimum access required to perform their tasks. Restricting permissions helps reduce the damage that an attacker can do if they manage to gain access to your system.
For instance, an employee who only needs read access to certain data should not have write or administrative access. Similarly, web applications should only be granted database access necessary for their functionality.
Tip #5: Regularly Update and Patch Software
One of the easiest ways attackers gain access to your systems is by exploiting known vulnerabilities in outdated software. Regularly applying software updates and patches helps close these security gaps and ensures your system is protected against new threats.
| Software | Recommended Action | Frequency |
| Operating System | Apply security patches and updates | Monthly or as released |
| Web Server | Update to the latest version | Quarterly |
| Database | Apply database security patches | As patches become available |
Tip #6: Use Web Application Firewalls (WAFs)
A Web Application Firewall (WAF) acts as a barrier between your application and the internet. WAFs can detect and block suspicious traffic, including SQL injection attempts and other attacks, before they reach your database.
Benefits:
- Automatically blocks known attack vectors.
- Offers real-time monitoring of incoming traffic.
- Protects against cross-site scripting (XSS), SQL injection, and other OWASP top 10 threats.
Tip #7: Encrypt Sensitive Data
Encrypting sensitive data both at rest and in transit helps protect it even if attackers gain access to your database or communications. For example, encryption ensures that stolen payment card information or customer data cannot be read without the decryption key.
Encryption Best Practices:
- Use SSL/TLS to encrypt data transmitted over the internet.
- Store passwords using secure hashing algorithms like bcrypt.
| Method | Benefit | Example |
| SSL/TLS | Secures data in transit | HTTPS encryption for all data transfers |
| Data Encryption | Secures data at rest | AES encryption for stored user data |
Tip #8: Monitor Database Activity
Database activity monitoring (DAM) tools track and record database access patterns, allowing you to detect suspicious behavior early. This proactive monitoring helps you identify potential SQL injection attacks or unauthorized access attempts before they cause significant harm.
Tip #9: Regularly Perform Security Audits
Conducting regular security audits ensures that vulnerabilities are identified and addressed before they are exploited. Audits involve reviewing system configurations, network traffic, user activity, and code vulnerabilities to identify potential risks.
Tools for Security Audits:
- OWASP ZAP for web application vulnerability scanning.
- Burp Suite for penetration testing.
Tip #10: Educate Developers and Employees
Regular security training ensures that developers and employees understand how to handle sensitive information securely and recognize potential threats. By raising awareness of phishing scams, strong password practices, and secure coding principles, you can reduce human error and vulnerabilities.
Wrap Up
In conclusion, the importance of safeguarding your systems from SQL injection and data breaches cannot be overstated. By following these 10 tips—including using parameterized queries, regularly updating software, and employing strong encryption—you can significantly reduce the risk of data loss and enhance your system’s security.
Cybersecurity threats are constantly evolving, and businesses must remain vigilant in order to protect themselves. Stay proactive, educate your teams, and implement these best practices today to ensure a secure future for your organization and its data.