Listen to Podcast:
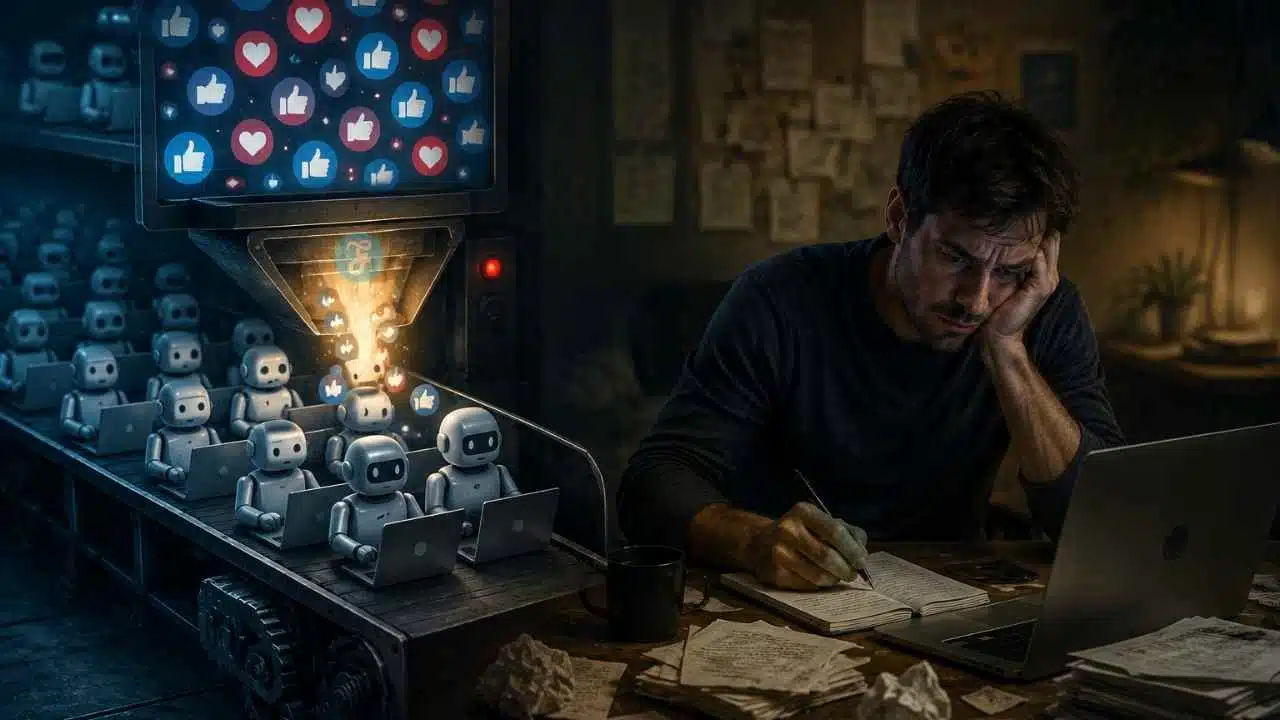
What sort of emotions would you have if someone kept staring at the screen of your iPhone all the time? Checking your emails, playing about with your camera roll, reading all of your messages, and looking through the history of your internet browser seems like a living hell, doesn’t it?
However, there are dozens of dubious businesses that do it behind your back without you even realizing it.
Read More: Apple Watch Series 9
For instance, certain businesses are committed to crossing data about your actual location, the amount of time you have spent at a particular location, and whether or not you have made a purchase at that location. All of this information is bundled together and then offered for sale to other businesses.
Some of them, particularly the more well-known ones, even have a profile on your preferences, your Internet activities, and your most recent purchases made online. How are they able to tell what you have purchased? It is very simple: all they need to do is check their email inbox and locate the receipts there. Indeed, they do this again and over again.
There are several reasons why maintaining one’s privacy is essential. Some of the repercussions stemming from the loss of one’s ability to maintain privacy. If the general public is allowed unrestricted access to and use personal information, then individuals run the risk of being hurt or weakened.
Other factors are more fundamental, and their effects extend to the core of what it means to be a human being. It is necessary to preserve personal privacy in order to appreciate the human individual as an end in himself and as an independent creature. When an individual gives up control of their personal information, they risk losing some measure of control over their lives as well as their dignity.
Read Also: Apple iPhone 15 will come with Wi-Fi 6E
Apple is the only brand of technology that makes it simple for its customers to exercise control over any and all elements that are connected to their privacy, despite the fact that European regulations are among the world’s most stringent in this regard. The privacy of customers’ information has been prioritized as a core principle by the corporation that Steve Jobs initially established.
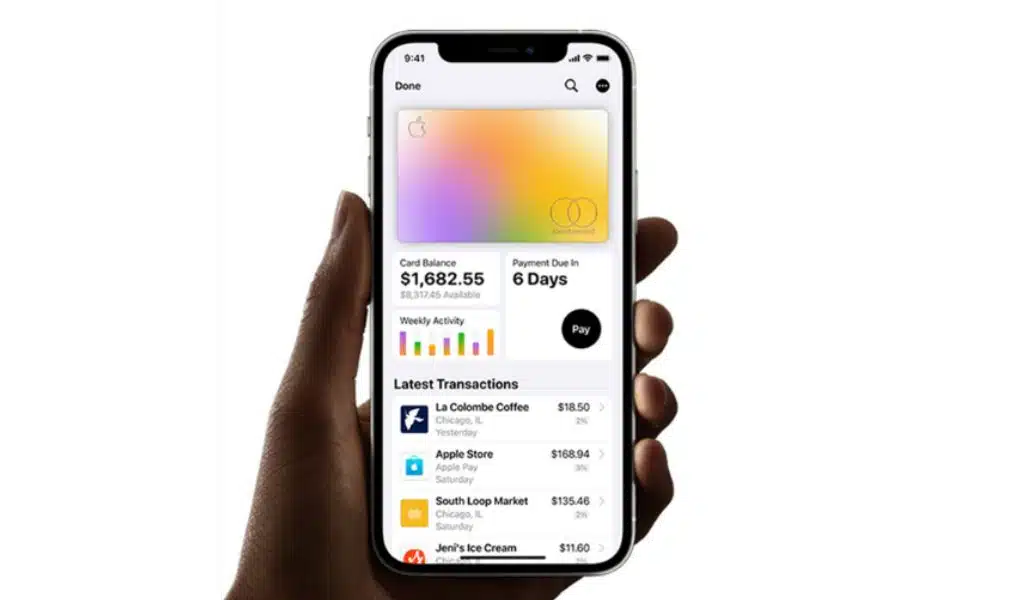
“Apple makes money with the products and services, not with the data of its consumers,” is how Tim Cook, the current CEO of the company, summarizes the brand’s strategy in this regard. Because of this, Bitten Apple is the only company that has been able to develop a set of tools that provide its customers with complete authority over the data and information associated with their goods and the information they store.
Some of these features are equally as critical as the one that prevents tracking and data gathering from any organization, regardless of whether they are located within or outside of your app. An alert screen appears on the iPhone whenever we install an application on it that attempts to spy on us. From this page, you have the option of asking the third-party company to refrain from engaging in any form of monitoring.
Privacy ‘nutrition’ labels are another useful tool. These labels, which can be viewed on the Program Store, educate consumers about what information a particular app intends to collect from them and can be interpreted as warning labels.
Also Read: Fix Your iPhone Stuck on Apple Logo
However, these are not the only methods available to regulate privacy. On the occasion of Privacy Day, which will be observed the following Saturday, January 28, the business has compiled a list of several tips and tactics that can be used to control this characteristic of the iPhone. Do any of these:
1. Location
You have control over when apps can access your location and how they do so. Check your iPhone to ensure that it is not sending your location data to anyone with whom you do not wish to share it.
Navigate to the Settings menu, then select Privacy and Security, and then select Location Services.
You have the ability to limit access by selecting Never, Ask Next Time, or On Use from the available options.
2. Protect the Mail on your iPhone
When you use Mail, third parties may be able to learn about your behavior and use this information to infer data about you and track you for advertising purposes using the emails that you receive from them. Your Internet activity will remain hidden from the sender because mail protection conceals your IP address. Additionally, it conceals the precise area you are in and prevents senders from determining whether or not an email has been opened by the recipient.
Navigate to the Settings menu, select Mail, and then select Privacy Protection.
3. Avoid Tracking Apps
Some apps will monitor what you do on the websites and other apps created by other companies. Now it is up to you to decide whether you will permit it or not, or whether you will insist that they get your permission beforehand.
To Know More: Apple’s Next MacBook Pro with Touch Screen
Navigate to Settings > Privacy and Security > Location Services. Tracking: Depending on the app, you can choose to enable or disable tracking, and you also have the option to disable tracking entirely.
4. Check your Security
Apple’s new Safety Checkup feature can assist you in the event that you ever need to rapidly stop sharing your information, as well as review and change the information that you share with specific persons and apps. The adjustments are made in a covert manner. When you discontinue sharing with a person or app, that person or app is not notified.
To do a security check, navigate to Settings > Privacy and Security > Security check.
5. Use the Access Keys
You can now sign in to a website or service using something called “Access Keys,” which is a new feature that eliminates the need for you to fill in your username and password in order to verify your identity. A one-of-a-kind digital key is generated for each user, and that key can only be used to log in to the specific website or mobile application that it was designed for. This makes the login process much simpler and more secure. Access Keys can be used to authenticate your login in conjunction with Touch ID or Face ID.
One of the following must be done in order to save an access key to your iPhone and iCloud Keychain:
On the screen that asks you to register for an account, you will need to give your new account a name.
— If you already have an account, you will need to sign in using your password and navigate to the screen where you may manage your account.
Tap the Continue button when you are presented with the opportunity to save a passcode for the account.
The password will be stored for future use.
6. Check your Privacy Settings
There is a dedicated section under Settings that allows you to view the information and permissions that you have granted to the applications that are installed on your mobile device. On the list are items such as your contacts and calendar, as well as your location, camera, and microphone. It’s a quick and easy task that can help protect the privacy of your personal information.
Navigate to Settings, then click Privacy.
After that, you should be presented with a list of the capabilities and data stored on your phone to which applications should inquire about gaining permission to access.
7. Use Private web Browsing in Safari
While you browse the web, certain websites give permission to hundreds of data-gathering companies to track your activity, create a profile of you, and send you advertisements. The Smart Tracking Prevention feature found in Safari makes advantage of the machine learning capabilities of the device itself to assist stop these trackers. In addition, by going to your Privacy Report in the toolbar of Safari, you will be able to view an overview of all of the cross-site trackers that Safari is blocking.
Navigate to Settings, then select Safari, and turn “No cross-site tracking” on.