In today’s fast-paced digital world where security is quite essential, biometric authentication has emerged as a powerful security system to safeguard online users’ data and sensitive info.
Unlike the regular traditional authentication system that involves passwords, tokens, and 2-factor authentications, the biometric security system uses biological and behavioral features to identify users. One of the most common biometric systems is fingerprint recognition and face ID.
Biometric authentication is a step in the appropriate direction as far as digital security is concerned. And this is because it’s heavily dependent on distinctive biological traits that can’t be replicated or transferred.
In this piece, you’ll discover the advantages and disadvantages of the two common biometric authentication: The fingerprint and the face ID security system.
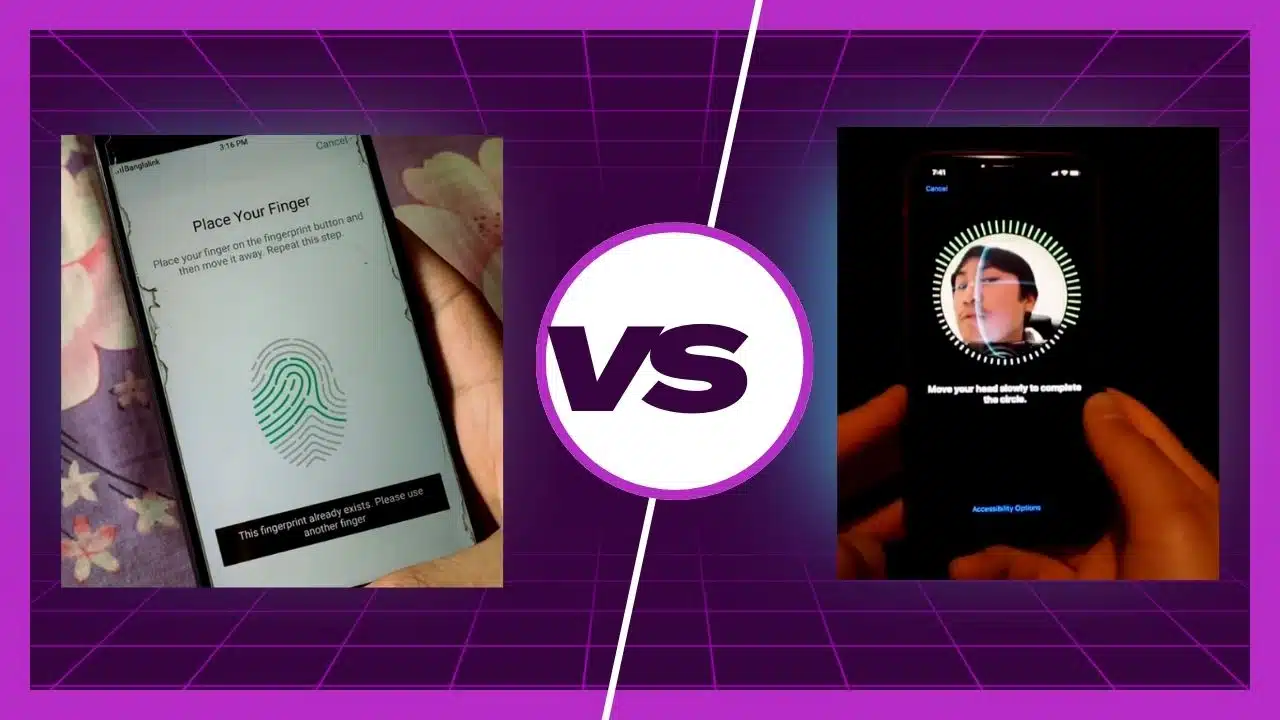
Fingerprint Versus Face ID
The fingerprint and face ID security systems are the 2 most common security systems in the world of biometric authentication. As much as they both have their merits and demerits it’s ideal you understand their comparative strengths and weaknesses.
This will help you know which is more suitable for specific applications.
Fingerprint Authentication
Fingerprint authentication is a type of biometric security system that is dependent on the unique patterns in each person’s fingerprint. Such patterns help fingerprint sensors identify the prints of users and grant access only if it’s the same as what was registered.
Advantages
User Convenience
The fingerprint authentication system ensures user convenience. You don’t have to memorize passwords or even type them. All you need to do is touch the fingerprint sensor. This eliminates problems that come with traditional authentication.
Affordability
Fingerprint sensors are quite inexpensive and it’s a cost-effective way for organizations and companies to enhance their security systems.
Wide User Acceptance
The fingerprint security system is widely accepted by the general public. Right now, most smartphones, tablets, and laptops now have a fingerprint sensor. This is due to its ease of use.
Disadvantages
Damaged Fingerprint
Cuts and scars can affect fingerprint-sensor readings and this could lead to failure of the authentication process.
Prone Spoofing
Artificial fingerprints can also be used to circumvent fingerprint sensors.
Face ID Authentication
Face ID authentication is more recent than fingerprint and it uses facial recognition to identify users based on their unique facial features. The algorithm captures and analyzes facial features such as the distance between the eyes, the nose’s shape, wrinkle patterns, and the like.
This biometric security system generates a facial signature it stores and uses during the authentication process before allowing users access.
Advantages
User Convenience
Given the contactless and hands-free authentication experience, users find face ID quite convenient. It’s not as demanding as the traditional authentication system.
Identification in Motion
Even when users are moving, face ID identifies them. This makes it quite suitable for changing environments. The face ID security system is quite convenient even in such situations.
Multi-person Authentication Potential
Facial recognition has the potential of virtually recognizing many individuals at the same time, expanding its applicability.
Disadvantages
Light Sensitivity & Facial Expressions
Some lighting conditions, extreme facial expressions, and poses can affect the accuracy of results. Thus, some places aren’t suitable to use this security system.
Privacy Concerns
Facial data collection and storage raises privacy concerns. Thus, it requires careful handling of user data.
Misuse Potential
Face ID data has the potential to be misused. It could be misused for surveillance, and unauthorized data collection, and this could lead to theft, murder, and many other types of crime.
Which Security Authentication Is More Appropriate To Use?
Choosing between fingerprint and face ID authentication heavily depends on your specific application requirements. Fingerprint is quite reliable and it’s also an inexpensive security measure. Thus, it guarantees accuracy and affordability.
However, Face ID is contactless, able to identify users in motion, and is quite convenient. With the continuous evolution of biometric technology, combining these 2 security authentication systems is better as it strengthens security.
In addition, the advancement of AI and machine learning are expected to improve the functionality of both Face ID and fingerprint authentication. Thus, using one and ignoring the other won’t do users any good.
As much as they have their weaknesses, they complement each other. Facial recognition can be affected by poor lighting conditions but fingerprint authentication can help remedy this situation.
On the other hand, if there are no fingerprint sensors, facial recognition can come through in the authentication process. Right now, phones, laptops, and many other devices are now including both fingerprint and facial recognition features.
This ensures users have various ways to gain access to their devices. And it also ensures all-round ease and convenience. Combining the two authentication methods is the ideal solution.
Conclusion
Fingerprint and face recognition authentication are independently ideal security solutions. But together, they enhance security for individuals, companies, and organizations. Quite frankly, you don’t have to have a preference.
Both of them are now even combined in a single device.