Any message sent by your organization either builds or weakens customer confidence. This is why email authentication and implementation of Verified Mark Certificates (VMC) are essential. When customers get emails from your domain, trust decisions are made in a split second. Such decisions impact the development of long-term business relationships and revenue generation.
Verizon declares a 34% increase in attackers exploiting vulnerabilities to get initial access and cause security issues. Such a threat poses a significant challenge to the business’s reputation. It is questioned when customers fall victim to fraudulent emails.
The deeper-than-ordinary connection between email trust and brand perception. One email could erode customer confidence, which spills across the entire communication spectrum. It not only affects email marketing performance but also wider market positioning.
This is why it’s paramount to understand this link between email trust and brand reputation. Plus, brands need to know the risks and the business impact of phishing-like emails. This article focuses precisely on that, offering a complete picture of how email trust is crucial. Its importance, technical signals, and solution.
What is the Connection Between Email Trust and Brand Reputation?
What makes customers trust a brand? Is it the content? No, it’s the subtle cues of trust that make them want to open your email. Name of the email sender, the subject line, and what the email conveys in the message can be the cue that the user trusts.
Especially with your content, if it appears suspicious or resembles phishing scams, or is filtered into the spam section, it can lead to skepticism among customers. Such a lack of trust can lead to,
- Hesitation among customers to open future emails from your brand.
- Higher unsubscribe rates as recipients lose confidence in your communications
- Poor sender reputation that affects email deliverability across all campaigns
- Lost revenue opportunities from customers who ignore your promotional messages
- Damage to long-term customer relationships and brand loyalty
- Negative word-of-mouth that spreads beyond your email subscribers
Risks of Untrusted or Spoofed Emails
Phishing attacks, spoofing warnings, and lookalike domains will erode that credibility faster than any marketing campaign can restore it. When cybercriminals masquerade as your company to send emails, they have not only targeted your customers but have also begun the systematic destruction of the trust you have built over many years.
What is a Real-World Scenario?
Clients associate the negative experience of a financial fraud directly with your brand, causing bad press and regulatory scrutiny by authorities. Complaints by customers are spread on social media, which magnifies the damage across digital channels where your reputation counts the most.
Just imagine how one spoofed email can undo years of reputation-building when clients begin to lose trust in everything that bears your brand name: they begin to question every legitimate communication, hesitate before clicking on every link, and basically stop engaging in your email marketing altogether.
The harm compounds quickly, nonetheless. Less engagement from recipients signals a bad sender reputation to email providers, who then start pushing all legitimate emails to spam. The customer acquisition costs ramp up as prospects shy away from brands they consider a security risk.
What’s the Solution?
This is where advanced email authentication becomes critical. Solutions like mark certificates provide visible trust indicators that help customers distinguish authentic communications from fraudulent attempts, protecting both your brand reputation and customer relationships from irreversible damage.
Elements That Make Emails Trusted
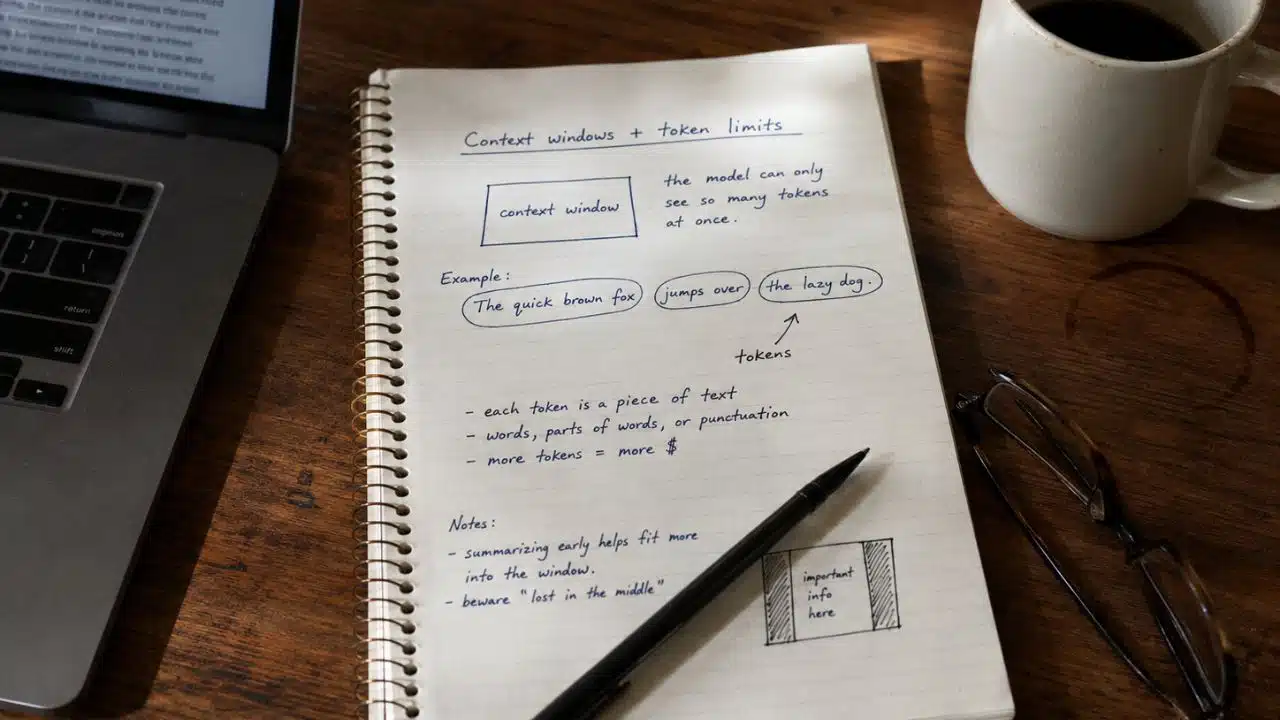
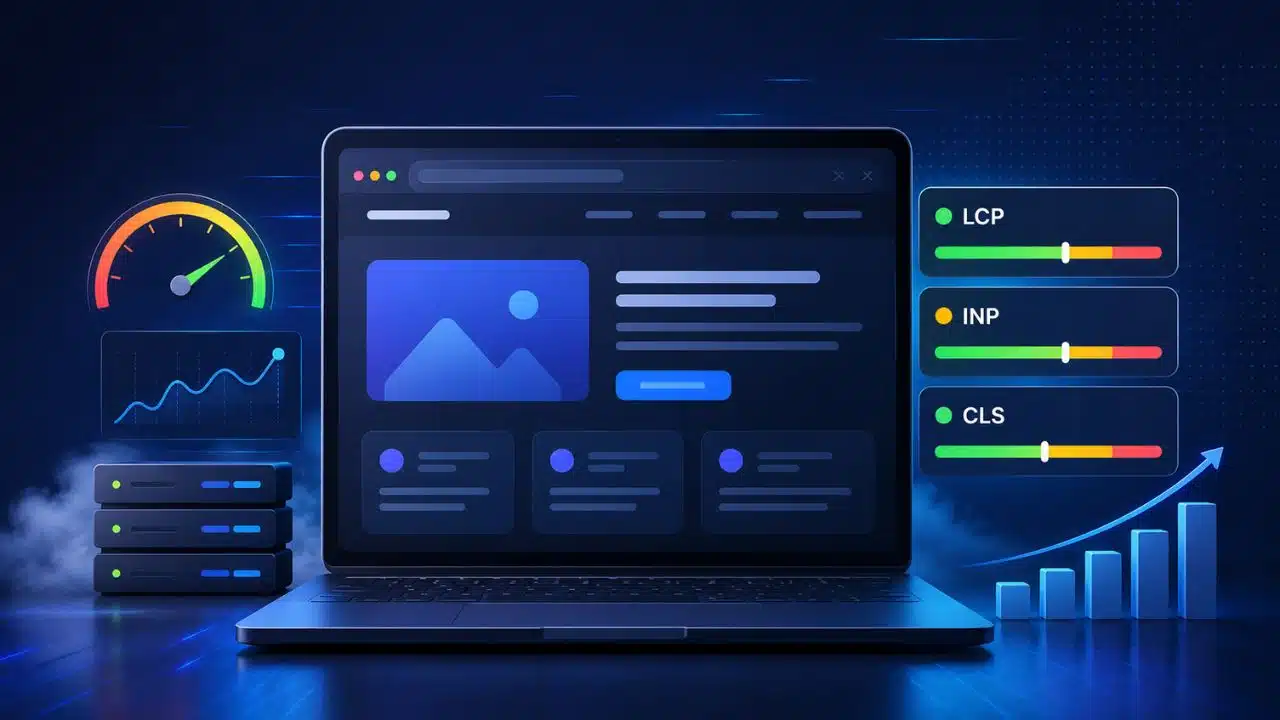
The basis of email trustworthiness is a technical signal. Authentication protocols such as SPF, DKIM, and DMARC ensure that emails are sent through your domain and that no third parties can send you mail. These are protocols executed behind the scenes to establish sender legitimacy with email providers.
The same design and tone create recognition and trust. Customers demand familiar and natural communication that aligns with your visual image and the style of message conveyance. The unexpected alteration of the templates, fonts, or patterns of communication may cause doubt and decrease the engagement rates.
Inboxes have visual trust signals that offer immediate credibility indicators. Popular logos, authenticated display name, and sender information are used to assist a recipient in identifying genuine emails in a short period of time.
This is where the value of a verified mark certificate comes in, especially with your verified brand logo appearing directly in the inbox to stir up more recognition and trust in you.
Business Impact of Trusted Emails
Better customer interaction means more open and click-through rates. Recipients who have the trust of your sender identity will actively participate in your content instead of ignoring emails without opening them or labeling them as spam.
Enhanced deliverability makes your messages reach target audiences. True domains that have been well authenticated are much less likely to be cleared as spam, improving campaign performance and ROI in all email marketing campaigns.
The long-term brand equity will be created as customers come to trust email and, consequently, trust the brand in general. This favorable preconception extends not only to email but also to purchasing behaviors and customer loyalty across all touchpoints.
The opportunity cost, loss of customers, and a tarnished image are included in the price of inaction. Brands that lose trust in email lose engagement metrics and have to pay a higher cost to gain acquisition, as their potential customers become less confident about what they are receiving.
How Businesses Can Strengthen Email Trust?
- Implement authentication schemes that begin with SPF, DKIM, and DMARC enforcement. These technical principles will avoid domain spoofing and enhance sender reputation among large email providers.
- Provide phishing awareness to the employees and the customers. Training internal teams would identify the threat regularly, and customer training would decrease the probability of attacks on your brand being successful.
- Adopt brand authentication, such as logo authentication and BIMI, with the VMC Certificate. These are the visual cues that offer instant trust signals to customers, helping to determine genuine communication from a scam.
- Constant performance and security posture forecast for email will be guaranteed by frequent monitoring and audits. The continuous evaluation will enable the detection of weaknesses before they affect the brand image or customer relations.
Takeaways
The reputation of the brand and the success of the business are directly linked to email trust. Companies that commit to comprehensive authentication, ongoing communication, and visual signs of trust develop sustainable competitive advantages. This includes stronger customer relationships and improved delivery performance.