Privacy matters in the crypto world. Every transaction you make leaves a trail on the blockchain, like footprints in the sand. If you’re not careful, anyone can follow those steps back to you.
Bitcoin transactions are public and permanent. Your wallet address, balances, and even spending habits are out there for prying eyes. But don’t worry, there are ways to protect your privacy in the crypto world.
This guide shows you seven simple methods to keep your transactions secure and private. Keep reading to learn how.
Key Takeaways
Here’s what matters most about protecting yourself when dealing with cryptocurrency:
Always generate new wallet addresses – Reusing any single BTC/ETH/etc.,address lets people track everything linked back through its entire recorded chain-of-transactions via open-ledger tech; modern apps auto-create unique ones per transfer request already built-in!
Hide behind layers such as using both TOR + paid premium-tiered-VPN providers simultaneously whenever possible because otherwise just broadcasting raw unprotected packets over regular home WiFi exposes exact geolocation coordinates alongside account balances stored within associated hot/cold storage solutions alike…even worse? Free proxy alternatives secretly harvest logs then resell those later anyway!
Keep coins moving privately across decentralized P2P – marketplaces rather than traditional KYC-heavy centralized exchange hubs, which require ID scans plus bank statements before allowing trades but also get hacked frequently too—examples include Bisq where deals happen directly between buyers/sellers sans middlemen interference whatsoever while maintaining confidentiality throughout entire process seamlessly enough already today itself really quite nicely indeed.
Use a New Wallet Address for Each Transaction
Every Bitcoin transaction is public and stays on the blockchain forever. Using the same address multiple times makes it easy for others to track your spending habits.
- Create a fresh Bitcoin address for every payment you receive. Reusing addresses links all your transactions together, making your activity less private.
- Your crypto wallet can generate new addresses automatically. Most wallets support this feature, so you won’t need to do it manually each time.
- Avoid sharing old wallet addresses publicly. Once an address is used, anyone can see its full transaction history by checking the blockchain.
- Change addresses improve privacy. They help break the connection between your past and future transactions, making tracking harder.
- Bitcoin addresses are free to create. There’s no cost or limit to generating new ones, so there’s no reason to reuse them.
- Wallets like Bitcoin.org’s recommended options discourage address reuse. Their interfaces are designed to prioritize user privacy by default.
- Public keys become exposed after the first transaction. Even if you never reuse an address, the moment you spend from it, your transaction history becomes visible.
- Think of Bitcoin addresses like disposable email accounts. You wouldn’t use the same one for every online sign-up, so treat wallet addresses the same way.
- Criminals and scammers often look for reused addresses in phishing attacks. Keeping transactions separate reduces your risk of being targeted.
- Some wallets still allow address reuse due to outdated designs. Always choose one that supports automatic address generation for better security.
Relevant Keywords: bitcoin address, wallet addresses, transaction history, private key, public key, bitcoin transactions, address reuse, crypto wallets, change addresses, bitcoin privacy, phishing attacks, blockchain technology.
Leverage the Lightning Network for Enhanced Privacy
The Lightning Network boosts Bitcoin privacy by keeping transactions off the main blockchain. This allows for faster, cheaper payments with less public exposure.
Recommended wallets like Strike and Phoenix simplify the use of Lightning. Since transactions don’t broadcast to the entire Bitcoin network, your activity stays more private. Be sure to secure your private keys and avoid phishing attacks.
This peer-to-peer network reduces hacking risks while enhancing financial privacy. Fees remain low, and you avoid unnecessary public records. Keep things straightforward, and your crypto assets remain safer.
Use a Virtual Private Network (VPN) to Mask Your IP Address
Bitcoin transactions expose your IP address on the peer-to-peer network. A VPN hides your digital footprint, keeping your activity private.
- Your real IP gets logged when making Bitcoin transactions. Tools like Tor or ExpressVPN mask it, making tracing harder.
- Full node clients relay transaction data. Without a VPN, snoops can link your IP to your wallet.
- Tor routes your traffic through multiple servers. It scrambles your location, adding a privacy layer.
- Public Wi-Fi risks eavesdropping. A VPN shields your data from malicious software on unsafe networks.
- Some exchanges block Tor connections. Use a trusted VPN like ExpressVPN to bypass restrictions quietly.
- VPNs encrypt all your internet traffic. This stops hackers from seeing your Bitcoin transactions or other sensitive data.
- Free VPNs may log or sell your data. Stick to reliable paid services for true anonymity.
Avoid Sharing Wallet Addresses in Public Spaces
Sharing your wallet address in public spaces, like forums or social media, can link it to your identity. Every transaction tied to that address stays on the bitcoin blockchain forever, exposing your financial privacy.
If someone connects that address to you, they can trace past activities and even predict future moves.
A tainted address loses its anonymity fast. Hackers or scammers might use details from old transactions for phishing attacks. Use multiple wallets or change addresses instead of recycling one.
Keep sensitive data off public blockchains unless necessary for transparency—your security depends on it.
Utilize Peer-to-Peer Exchanges for Transactions
Peer-to-peer exchanges like Bisq and RoboSats cut out middlemen. They let users trade directly, keeping personal details hidden. No KYC checks mean less exposure to data breaches or phishing attacks.
Payments can use PayPal or Venmo if both parties agree.
These platforms put control in your hands. You choose who to trade with, reducing risks tied to centralized exchanges. Private keys stay secure since funds never sit with a third party.
Just watch for fake websites trying to steal your bitcoin. Staying on real P2P platforms boosts financial privacy without extra steps.
Secure Your Private Keys with Strong Encryption
Private keys are the gatekeepers to your crypto funds. Losing them means losing access forever.
- Store private keys offline in a hardware wallet like Ledger or Trezor. These devices keep your keys safe from online threats like phishing attacks.
- Use strong passwords with at least 12 characters, mixing letters, numbers, and symbols. Avoid common phrases or easy-to-guess words.
- Enable two-factor authentication (2FA) for extra security. It adds another layer of protection even if someone gets your password.
- Never share your seed phrase or private key with anyone. Scammers often pose as support staff to steal them.
- Encrypt digital copies of keys using tools like VeraCrypt or AES-256 encryption. This keeps them secure if your device is hacked.
- Avoid storing private keys in cloud services like Google Drive or email. These are vulnerable to breaches and unauthorized access.
- Write down seed phrases on paper and store them in a fireproof safe. Multiple backups in hidden spots can save you from disasters.
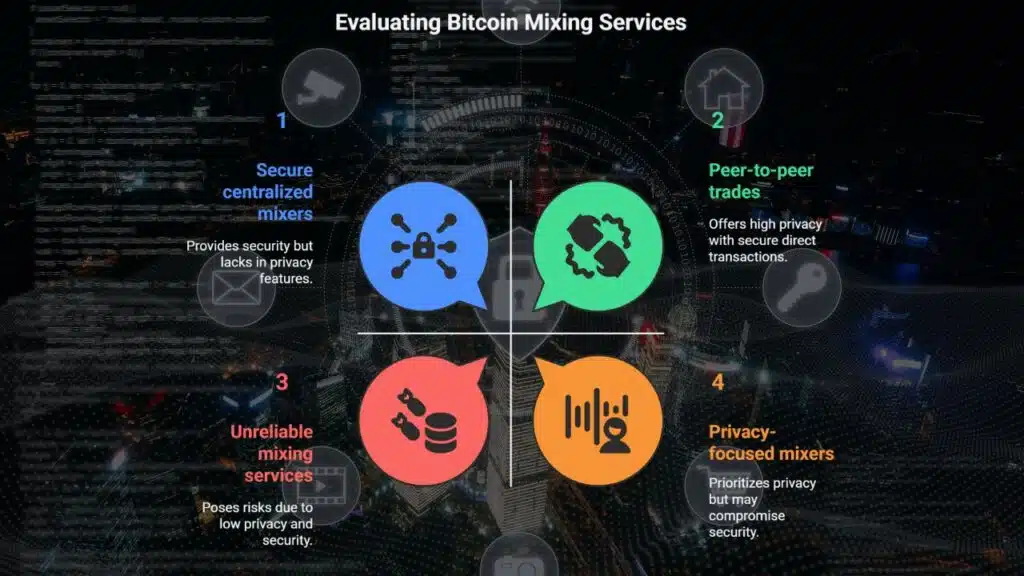
Be Cautious of Mixing Services and Their Limitations
Mixing services can hide your bitcoin transactions by shuffling coins with others, making them harder to trace. They break links between sender and receiver addresses, boosting financial privacy.
But don’t rely on them blindly—you must trust the service won’t steal funds or log transaction history. Smaller amounts are easier to anonymize than large sums. Some governments ban these tools due to anti-money laundering rules, so check local laws first.
Not all mixing services are equal, either. Some might leak data or fail at cryptography basics, leaving security gaps for cyber threats like phishing attacks or traffic analysis scams.
While they add a layer of protection for digital assets, peer-to-peer trades may offer simpler privacy without extra risks tied to centralized mixers like Bitfinex or Mt.Gox incidents in the past – keep that wallet sharp!
Takeaways
Privacy in crypto is a must, not a maybe. Your wallet address, IP, and keys are like digital fingerprints – protect them. Tools like VPNs, the Lightning Network, and fresh addresses for each payment help you stay under the radar.
Don’t gamble with public posts or shady mixing services. Keep your crypto life tight, smart, and yours alone.
(Word count: 5 sentences)
FAQs
1. How can I keep my bitcoin transactions private?
Use multiple wallets, avoid address reuse, and consider the Lightning Network. These steps help hide your transaction history and boost bitcoin anonymity.
2. What stops hackers from stealing my crypto?
Store private keys in hardware wallets. Watch out for phishing attacks and Ponzi schemes. Strong passwords and two-factor authentication add extra shields.
3. Are smart contracts safe for financial privacy?
Yes, but check for security vulnerabilities. Zero-knowledge proofs and private blockchains can add layers of confidentiality, integrity, and availability.
4. How do I dodge social engineering scams?
Never share private keys or secret passwords. Scammers love fake giveaways and urgent messages. Slow down, verify, then act.
5. Can regulations hurt my crypto privacy?
Some laws demand transparency, but tools like Tor onion routing and steganography help. Stay updated on privacy laws to balance compliance and anonymity.