Corporate boardrooms are currently buzzing with a single word. AI. Every leader wants it. Every manager expects it. Yet there is a massive disconnect between our tech dreams and our daily reality. Zoho Corp.’s State of Workforce Password Security 2026 report paints a sobering picture of this gap. While 90 percent of global leaders believe AI will strengthen their defense, a mere 8 percent are actually ready to deploy it today. This creates a staggering 82-point chasm. It is a mirage. We are essentially trying to build a penthouse on a sinkhole foundation.
In this climate, Workforce Identity Security is no longer just a checkbox. It is the ground beneath the entire enterprise. We are chasing the “next big thing” while our basic walls are still unpainted. Released ahead of World Password Day on May 7, this global survey, conducted by Tigon Advisory Corp. on behalf of Zoho, exposes exactly where these vulnerabilities lie. This data comes from 3,322 verified professionals. They represent nine global regions, from India to the US and the UK. Their collective experience shows that ambition is moving much faster than our actual ability to protect ourselves.

Security cannot be an afterthought. It is not a shiny tool you buy to fix a broken system. One in three businesses faced a confirmed cyberattack in the past year. Many of these firms had high hopes for automated defense. But you cannot automate a house of cards. If you lack visibility over who has access to what, AI will only accelerate your existing risks.
The Zoho-sponsored study highlights this “belief to deployment” trap. We see the finish line, but we have not started the race. This 82-point gap is a loud warning for every executive. We must secure the basement before we start decorating the roof. The numbers do not lie. We are enthusiastic, but we are not prepared.
The Invisible Attack Surface: Managing App Sprawl
The modern workstation is no longer a physical desk. It is a digital collection of browser tabs. We have traded office walls for a cloud of software. Every new tool promises efficiency but complicates Workforce Identity Security in ways we rarely see.
The Fifteen App Threshold
Data shows that 59 percent of employees now use at least 15 business apps every single day. We are juggling logins for email and chat and project management.
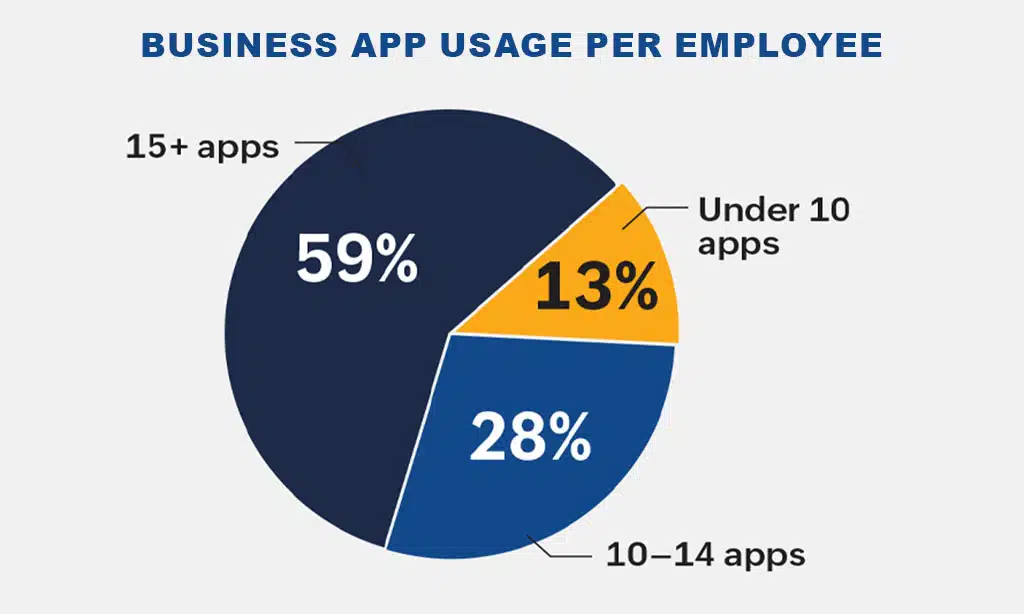
This explosion of tools creates a massive target for hackers. Most organizations simply cannot see the full extent of this digital footprint.
The APAC Digital Peak
The Asia Pacific region sits at the top of this trend. In APAC, 64 percent of the workforce relies on more than 15 apps to finish their tasks. This rapid adoption of cloud tools creates a unique pressure on security teams. While the region is moving fast, its defensive systems are often struggling to keep up.
Redefining the Perimeter
The physical office is a relic of the past for many. Currently, 35 percent of people work in a hybrid setup. Another 25 percent work entirely from home. This means the traditional security fence is gone. Every living room or coffee shop is now a corporate entry point. Our protection must travel with the person instead of staying at the desk.
The Regional Security Ledger
Global security is not a single story. Every region faces a different set of challenges. While the tools are often the same, the local reality dictates how well a company stays protected. Success depends entirely on where you sit in the world.
The Indian Paradox
India is currently racing toward the future. A massive 93 percent of Indian leaders believe in the power of AI to protect their data. They are backing this belief with capital. Ninety-one percent plan to increase their spending on security tools over the next five years. Yet they face a very harsh reality. Nearly half of Indian firms suffered an attack last year. This 47 percent attack rate is the highest in the world.
Expert Perspective: Building the Roof Before the Foundation

Says Chandramouli Dorai, Chief Evangelist, Cyber Solutions & Digital Signatures, Zoho Corp.: India’s security paradox is hiding in plain sight, 93% of organizations believe AI will strengthen their defenses, yet nearly half have already been breached and only 1 in 4 have basic password policies in place. The confidence far outpaces the controls. What concerns us most is that the greatest threat isn’t coming from sophisticated external actors. It’s coming from within, with malicious insiders ranking as the number one risk. Indian businesses are investing in the roof while the foundation is crumbling. AI can sharpen detection and response, but it cannot substitute for the fundamentals: knowing who has access to what, enforcing least-privilege principles, and closing the identity gaps that attackers walk through every day.”
The American Infrastructure Wall
In the United States, the will is there but the way is blocked. Ninety-one percent of US firms see the value in AI for defense. However, their legacy systems are holding them back. It is difficult to install new smart tech when your base is built on aging code. Most American companies are stuck in a waiting room. They cannot simply swap out their old foundations overnight.
The European Visibility Gap
Europe is the land of strict rules. Heavy laws like GDPR and NIS2 force companies to take data safety seriously. Even with these rules in place, there is a dangerous blind spot. Seventy-five percent of organizations in the UK and Europe still lack full visibility into their user identities. They have the paperwork but they lack the eyes.
A Tale of Two Paths
India has a distinct advantage in its speed. It is building new systems from the ground up. This allows Indian firms to skip the legacy baggage that slows down the West. While the USA and UK struggle to fix old foundations, India is adopting platform-native tools. This creates a unique window for Workforce Identity Security to take root.
Expert Perspective: A Global Strategy for a Borderless Threat
“The identity security crisis is not confined to India. Across the US, UK, and APAC, our research shows organizations are grappling with the same structural blind spots. These include incomplete visibility over workforce identities, under-adopted Zero Trust frameworks, and a widening gap between AI ambition and operational readiness. The threat landscape is borderless, and our response must reflect that reality.” ~ Chandramouli Dorai, Chief Evangelist, Cyber Solutions & Digital Signatures, Zoho Corp.
The Human Element in Security
Technology is only half the battle. The real risk lies in our daily habits and our chronic staffing shortages. We can buy the best software on the market, but it cannot replace a watchful eye or a trained mind. Security is a human practice. It lives in the choices we make every morning when we log into our systems.
The Danger of the Mundane
We often hunt for complex, movie-style threats. The truth is far more ordinary. Phishing remains the primary threat for 68 percent of companies. Simple, weak, or reused passwords follow at 61 percent. These small errors are far more dangerous than any exotic exploit. They are the unlocked windows of the corporate world. Most breaches do not happen because a hacker was a genius. They happen because a door was left open. Improving Workforce Identity Security means closing these small gaps before worrying about high-tech monsters.
Hackers target our psychology. They use fear or urgency to trick us into clicking a link. This is why phishing is so effective. It bypasses our firewalls and goes straight for our trust. It is much easier to trick a human than it is to break a machine. Our defense must reflect this reality. We need to make it difficult for employees to make a mistake.
A Global Talent Drought
Our desks are sitting empty. The world faces a projected 3.5-million person shortage in the cybersecurity workforce through 2026. This is not just a hiring problem. It is a structural defense crisis. Sixty-five percent of firms currently lack a Zero Trust strategy. They simply do not have enough hands to build a safer perimeter.
This gap puts a massive weight on the people we do have. When teams are stretched thin, they miss things. They burn out. An empty chair is an invitation for an attacker to walk right into your network. We are asking our existing teams to do the work of ten people. It is a recipe for exhaustion and error. We cannot secure our data if there is nobody there to watch the gate.
Systems Made for Real People
We need tools designed for the talent we have on hand. Our strategy must match the reality of our current team. This is why “opinionated” platforms are becoming the new standard for business. These tools come with smart safety settings already enabled by default. They do not wait for a human to make a perfect choice.
Instead, they guide users toward better habits without a lecture. We must stop dreaming of an army of security experts. We need to start using systems that work for the people already in the room. This shift removes the burden of choice from the user and places it on the system. It is the only way to scale safety in a world with too few experts. Success relies on making the safest path the most natural one for every employee to follow.
The 2026 Workforce Security Data Ledger
This table provides a sharp look at the structural gaps and regional paradoxes found within the report. Every percentage reflects the current tension between digital ambition and operational reality across all major markets.
| Security Metric | Global Benchmark | Regional Insight |
| AI Confidence Gap | 82% Difference | 90% of global leaders believe in AI vs 8% ready to deploy |
| Attack Incidence | 33% Annually | India leads global attack rates at 47% |
| App Overload | 59% Usage | 64% of APAC staff use 15+ apps daily |
| Identity Blind Spot | 88% Untracked | Orphaned accounts hide the true attack surface globally |
| Infrastructure Wall | 91% Blocked | Legacy systems stall AI adoption in the United States |
| Phishing Success | 68% Threat | The primary entry point for modern breaches everywhere |
| Visibility Crisis | 75% Blindness | UK and EU firms lack clear identity visibility despite rules |
| System Readiness | 98% Mandate | 98% of Indian organizations are very likely to deploy AI-driven security tools |
The Identity Visibility Gap
Organizations often believe they know exactly who is inside their network. However, the data suggests otherwise. True safety requires a clear view of every user and every account. Without this clarity, even the most expensive tools remain blind to the risks within their own walls.
The Ghost in the Machine
Orphaned accounts are a silent threat that many companies overlook. These are logins left behind by former employees or temporary contractors who no longer work there. When you factor in these digital ghosts, 88 percent of organizations lose track of who has access to their sensitive data. It is like having an expensive alarm system but leaving the keys with people who no longer live in the house. This gap makes it impossible to maintain a strong Workforce Identity Security posture. If you do not know an account exists, you cannot protect it.
The Price of Vendor Sprawl
Many firms try to buy their way out of risk by collecting a long list of different tools. This leads to a messy sprawl that is hard to manage. Currently, 30 percent of organizations are managing six or more security vendors at the same time. Instead of making things safer, this often creates more work for already tired teams. About 34 percent of leaders say that trying to make these tools work together is their biggest operational headache. Managing too many different systems makes it easy for a threat to slip through the cracks unnoticed.
Integration as a Non-Negotiable
The era of disconnected security tools is ending. Nearly every leader now recognizes that systems must talk to each other to be effective. A massive 98 percent of respondents view security integration as a basic requirement for future readiness. We need a single source of truth for every user across every app. If our tools do not work together, they are ultimately working against us. A unified platform approach is no longer a luxury for large firms. It is a basic necessity to stay ahead of the next breach. True protection comes from simplicity and connection.
The SMB Security Paradox
Smaller businesses often face the same threats as global giants but with only a fraction of the resources. They are the backbone of the economy yet remain the most vulnerable link in the digital chain. A breach that a large firm might survive could easily put a small company out of business forever.
The Defensive Capability Deficit
Size does not protect you from a cyberattack. In fact, over 50 percent of the respondents in the Zoho Corp. study represent small and medium businesses. These companies often operate without a single dedicated security professional on staff. They rely on general IT workers or even office managers to handle complex digital safety tasks. This lack of expert oversight creates a massive opening for hackers to exploit. Without a trained team to watch the gates, these firms are essentially operating without critical visibility.
The Shared Spreadsheet Trap
Many smaller firms still rely on informal and dangerous habits to manage their data. They often store sensitive passwords in shared spreadsheets or simple word documents. Some even rely on the built-in saving features of web browsers which are notoriously easy to compromise. This “spreadsheet security” is an invitation for disaster.
Moving away from these manual methods is now a requirement for survival. SMBs need managed platforms that offer high-level protection without the need for a massive internal team. These systems provide automated oversight and strong encryption that a manual list simply cannot match. Switching to a professional management tool is the fastest way for a small business to close its defense gap. It turns a major liability into a manageable part of the daily routine. Security must be accessible to everyone regardless of their company size or budget.
Building for the Future
The path forward requires a shift in how we think about our digital defenses. We cannot simply buy our way out of risk with the latest gadgets. Instead, we must focus on a logical order of operations to stay safe. Success depends on doing the right things at the right time.
Sequencing Success
We must start with the basics by securing every single set of credentials. This means implementing strong governance over who can access our systems from the very beginning. Once our house is in order, we can then move toward a Zero Trust framework to verify every user and device. AI-enhanced monitoring should be the final step rather than the first one. Using smart tech to watch a broken system will only create more noise. We need to fix the pipes before we install the smart meter.
The Core Imperative
Helen Yu of Tigon Advisory Corp makes a clear point about our current situation. She notes that budget is not the primary barrier for most companies.
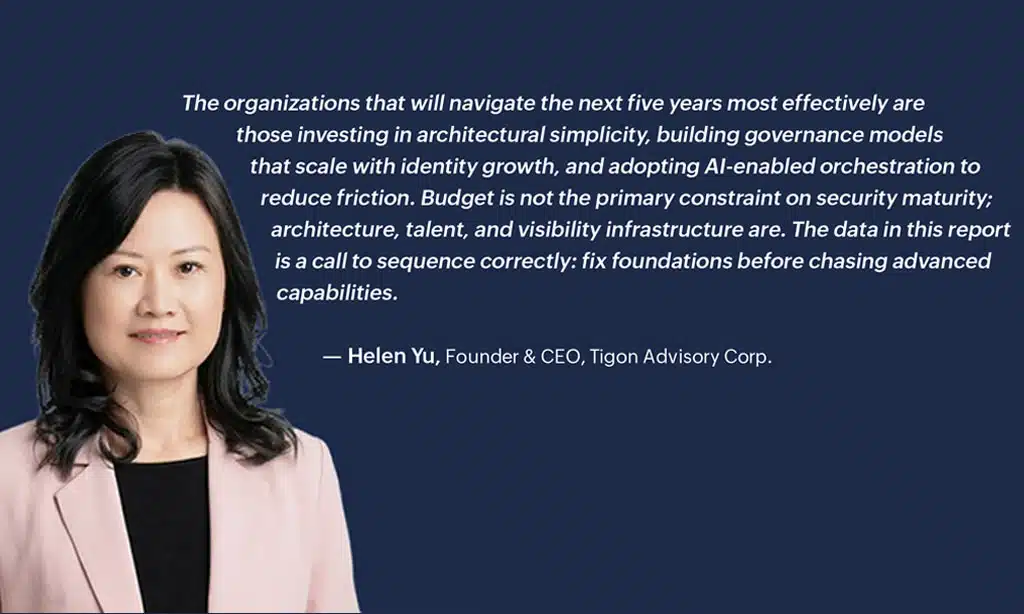
The real problem lies in our systems and how much we can actually see within them. We must fix our foundations before we start chasing advanced capabilities. If we ignore the base, even the most expensive AI will fail to protect us. It is time to stop looking for shortcuts and start doing the hard work of building a solid core.
A Clear Call to Action
The next five years will be defined by those who choose simplicity over complexity. We need to invest in frameworks that are easy to manage and even easier for employees to use. By reducing the number of tools and focusing on deep integration, we can close the gaps that attackers love. This approach turns security from a burden into a quiet strength. Every leader should prioritize a unified approach to Workforce Identity Security starting today.