Microsoft has confirmed that several state-backed Chinese hacking groups have exploited vulnerabilities in its on-premises SharePoint document servers. These attacks did not affect Microsoft’s cloud-based SharePoint service but targeted companies using servers hosted within their own IT infrastructure.
The cyberattacks were linked to groups known as Linen Typhoon, Violet Typhoon, and Storm-2603—all believed to operate out of China or have connections to Chinese state interests. Microsoft says the attackers exploited known flaws in SharePoint software to gain unauthorized access to sensitive data and encryption keys.
Security Patches Released Amid Ongoing Threats
In response, Microsoft has issued critical security updates and strongly advised all customers using on-premises SharePoint servers to apply the patches immediately. The tech giant warned that systems which remain unpatched are at high risk of further attacks.
“Investigations into other actors also using these exploits are still ongoing,” Microsoft said in its official security blog. The company pledged to continue publishing updates as it learns more about the nature and scope of the breaches.
How the Attacks Worked
According to Microsoft, the hackers exploited a vulnerability that allowed them to send malicious requests to vulnerable SharePoint servers. These requests enabled them to steal cryptographic keys, allowing unauthorized access to stored data and communications.
This technique, known as key material theft, potentially gives hackers long-term access to sensitive organizational data—even after initial detection or removal.
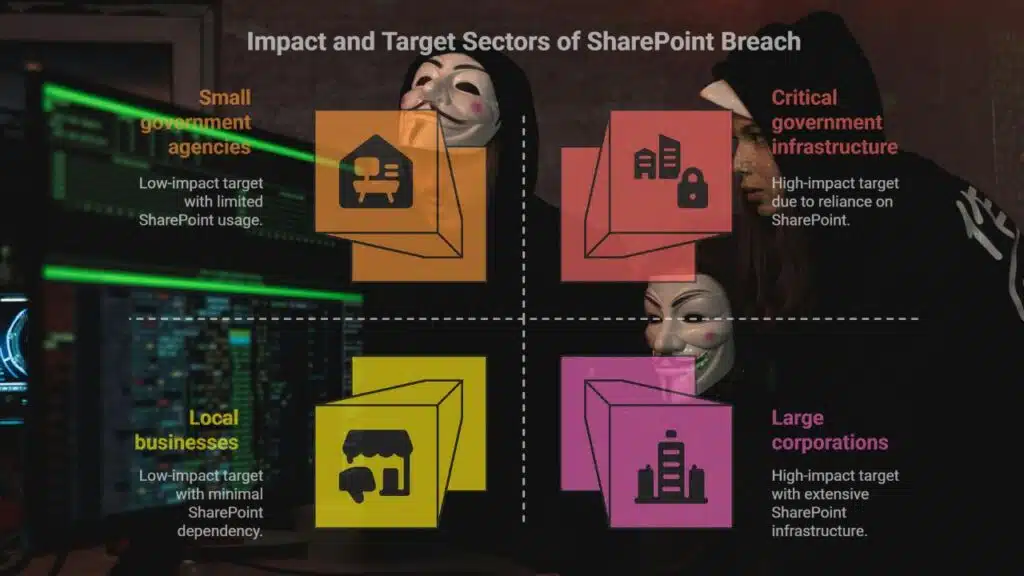
Global Impact and Target Sectors
Charles Carmakal, CTO at Mandiant Consulting, a division of Google Cloud, stated that his firm had identified “several victims across different sectors and global regions.” He emphasized that both government institutions and businesses relying on SharePoint were primary targets.
“This was exploited in a very broad and opportunistic way before Microsoft issued a patch,” Carmakal explained. “That’s why this breach is particularly significant.”
Repeat Patterns in China-Linked Cyber Campaigns
Carmakal also noted that the hacking techniques used in this case closely resemble those seen in earlier cyber campaigns linked to Beijing-sponsored actors. He described the behavior of the attackers as opportunistic, aiming to infiltrate as many unpatched systems as possible.
Profiles of the Involved Hacking Groups
Microsoft offered deeper insights into the history and focus of each group involved:
Linen Typhoon (also known as Hafnium or APT40): This group has been active for over 13 years. Its primary objective is to steal intellectual property, with a focus on organizations involved in government affairs, defense, strategic planning, and human rights.
Violet Typhoon (associated with APT31 or Zirconium): This threat actor is primarily engaged in espionage, targeting former government and military personnel, as well as NGOs, think tanks, media outlets, academic institutions, and sectors such as finance and healthcare across the US, Europe, and East Asia.
Storm-2603: Microsoft assessed this group to be a China-based threat actor with medium confidence. Although less documented, it has demonstrated capabilities in exploiting enterprise software.
Why the Breach Matters
Cybersecurity experts stress that the SharePoint vulnerability is especially critical because it involves a widely used enterprise product. Since many organizations host sensitive and confidential data on SharePoint, successful exploitation could lead to data leaks, persistent surveillance, and long-term system compromise.
Furthermore, exploiting cryptographic material allows hackers to bypass standard authentication and remain undetected for extended periods.
Urgent Call to Action
Microsoft urges all organizations still using on-premises SharePoint servers to immediately:
- Apply the latest security patches
- Review their server logs for unusual activity
- Rotate cryptographic keys and credentials
- Consider migrating to Microsoft’s cloud-based alternatives where feasible, which are not affected by this breach
The tech giant also promised to update customers through its official channels, including the Microsoft Security Blog.
Expert Warnings on Future Threats
Experts believe these attacks are part of a broader, long-term strategy by state-sponsored cyber groups to infiltrate critical infrastructure and gain access to strategic information.
Given the scale and sophistication of the current attacks, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) and international partners may also issue advisories to coordinate defense measures.
The Information is collected from CNBC and MSN.