Using a proxy has become very popular because it helps you stay anonymous, not worry about geographic restrictions, and you can also have more control over the online experience. The downside is that you can encounter a whole lot of mistakes when using a proxy. That’s why we made a quick list of stuff to consider and how you can avoid some of these proxy mistakes yourself.
Choosing the wrong proxy type
Data center proxies are fast and affordable, but they are easy to detect. Residential proxies are authentic, but they are more expensive and slower. And then there are mobile proxies, which are limited and costly, even if they are highly trusted. Match the proxy type to your specific use case and you won’t have a problem.
Using free proxies
Free proxies tend to be not as reliable. Not only that, but they have lower speed and poor performance. Plus, due to the IPs being used over and over, there is a much higher chance of getting blacklisted. And there’s also a lack of security and encryption. In some cases, you will also have potential data theft and logging. Invest in a paid proxy, check reviews and always stay away from a service which is lacking in transparency.
Not rotating the IP addresses
It’s not a good idea to use the same IP address for multiple requests. This is a common mistake, and it can be problematic in the case of web scraping or automation. The way you solve it is you start using rotating proxies, and you also set up automatic IP rotation. It’s also a good idea to distribute requests across multiple IPs if you can.
Relying solely on proxies
There are plenty of people who think that using a proxy is all the security that they need. But that’s not the case at all. Most of these proxies are not encrypting traffic, so your data will get exposed, and that will be a problem. What you want to do is to use secure browsers and also implement firewalls as well as anti-malware software.
No maintenance or monitoring
That’s the thing, even if you implemented a proxy, you still want to maintain and optimize it the best way that you can. Without that, performance is going to degrade over time, and IPs can easily become blacklisted. Plus, various tasks will fail without notice. What you want to do is to monitor the performance of your proxy, refresh/replace IPs when needed, and also start using analytics tools and your dashboard as well.
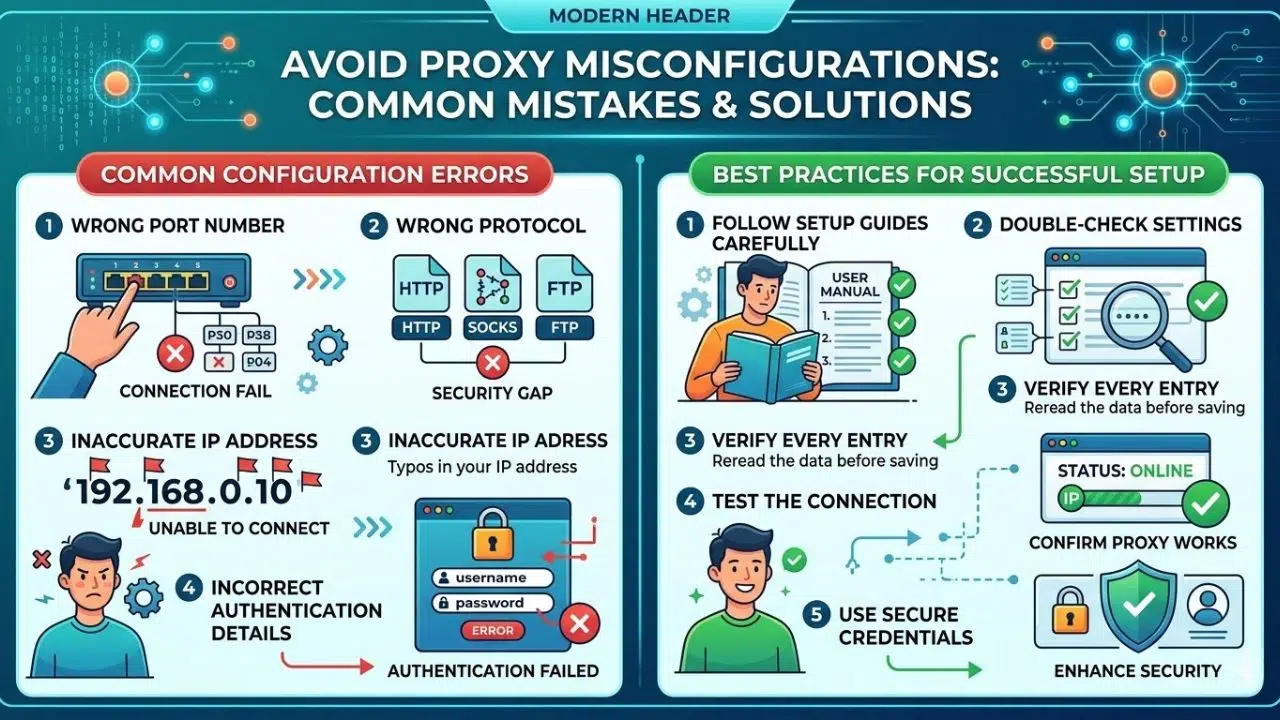
Misconfiguring the proxy settings
If you don’t configure your proxy properly, that will be an issue. And that will happen, when you are choosing the wrong port number, when you choose the wrong protocol and so on. In order to circumvent that, you should consider following the setup guides carefully, and also double-check configuration settings.
Not testing the proxy
It’s always an issue when you go ahead into something without testing. And using a proxy this way is definitely problematic. You can end up using a slow or dead proxy, blacklisted IPs or even incorrect IP locations. What you need to do is to run latency and speed tests. On top of that, it makes sense to check the IP reputation, not to mention you should assess the anonymity level where possible.
Ignoring geolocation requirements
Depending on the situation, you might have to deal with specific geographic location requirements. If you are using the wrong location, that might offer inaccurate data, it could trigger security alerts and it might as well prevent access to certain content. So, choose proxies that have good geotargeting and which match the IP location to the one you want. Testing the location accuracy before using is crucial, and it could help save a huge amount of effort and time.
Overloading a single proxy
Even if you are using the best proxy, even that can get overloaded at times. You don’t want to push too much traffic through a single proxy. That will lower speeds, increase the detection risks and also increase failure rates more than you might expect. Instead, what you want to do is distribute the workload and monitor the bandwidth usage. Scaling the proxy pool can also be something you want to consider, and that’s totally a thing to keep in mind.
Ignoring the proxy security/authentication settings
If you just use random settings for your proxy, that can be a problem. A good approach is to use username/password authentication on IP whitelisting and also enable the secure protocols. You should also update your credentials often if possible.
Using very few proxies for large tasks
If you want to scale your operation, you do want to use more proxies. Scaling the proxy pool based on the workload is an obvious approach and it will help you more than expected. You also want to plan capacity in advance, something that will help you more than expected.
Focusing just on pricing
Granted, prices will always matter when you invest in anything. But the problem with proxies in particular is that cheap ones will offer poor quality, high failure rates and you will lose productivity, not to mention time. The best approach is to balance cost and quality, and focus on the long-term return on investment.
Another problem is that you can sometimes neglect ethical use. There are people that use proxies to scrape sensitive data without permission, mis-use residential IPs and overload websites. The best approach here is to focus on respecting the website limits and staying responsible when it comes to the proxy use. That’s what will help make things better, and you can avoid various other issues down the line.
Closing thoughts
It’s very easy to make a large number of proxy mistakes. The most important thing is to use guidelines such as ours to understand what mistakes people make the most and prevent those as much as possible. Thankfully, using a professional proxy service will help you get past most of these problems. With that in mind, you always want to configure everything properly and optimize everything to the best of your capabilities. In the end, it’s always going to be worth the effort, especially if you focus on security and improving your internet privacy!