Losing your digital money feels like misplacing cash under the couch, except you may never get it back. Many folks worry about hackers, lost passwords, or broken wallets wiping out their savings in seconds. A recent 2025 analysis report shows crypto hacks hit a staggering $3.4 billion in a single year. That makes learning exactly how to secure crypto storage in 2026 an absolute priority for anyone holding digital assets.
You know, I found that taking just a few simple steps completely changed how secure I felt about my own portfolio. It turns out that securing your coins from thieves and tech failures is easier than you might think. So, grab a cup of coffee, and let us go through it together. I will walk you through the exact tools and steps you need to protect your funds.
Understanding How To Secure Crypto Storage In 2026
Keeping your digital money safe requires more than just a good lock and key. You need to pick the right stash spot, or you could be left with empty pockets.
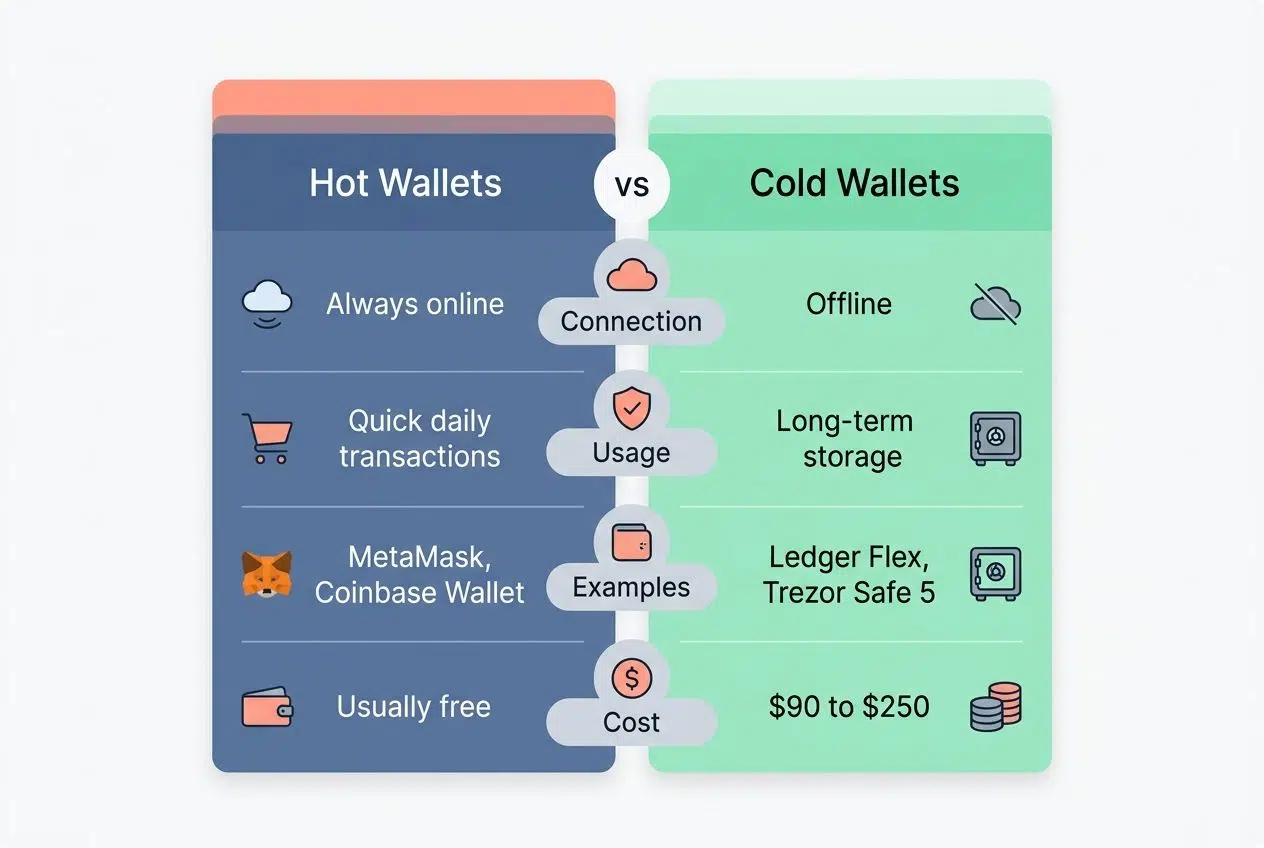
Hot Wallets vs. Cold Wallets
No two wallets are built the same, and the way you store your coins can make or break your crypto journey. Active internet connections define hot wallets, while cold wallets stay offline for maximum asset protection.
Here is a quick breakdown to help make sense of your options:
| Feature | Hot Wallets | Cold Wallets |
|---|---|---|
| Connection | Always online, internet-connected | Offline, no web access |
| Usage | Quick daily transactions in the US | Long-term storage, rare use |
| Examples (2026) | MetaMask, Coinbase Wallet, Zengo, Phantom | Ledger Flex, Trezor Safe 5, D’CENT Biometric |
| Security Level | High risk of hacks (44% of stolen crypto value in 2025) | Far less vulnerable to online attacks |
| Recovery | Digital recovery phrases are easier to restore, but easier to steal | Physical backup needed to prevent total loss |
| Cost | Usually free to download | Devices cost $90 to $250; steel plates cost $99 |
The Importance of Private Keys
Private keys act like the password to your digital wallet. If a thief gets this key, they steal all your crypto in seconds. Private keys use strong encryption and math puzzles that only you should solve.
A 2025 report from Chainalysis revealed that private key compromises accounted for nearly 44% of all stolen crypto. Losing control of these codes is much worse than losing a house key, because there is no locksmith for blockchain technology.
You cannot call customer service if you forget it. Your crypto simply becomes a ghost on the network forever. Strong cryptocurrency security starts with protecting those secret strings of letters and numbers at all costs.
Guard your private keys tighter than gold, because one slip could cost you everything.
Types of Cryptocurrency Wallets in 2026
Wallets look vastly different now than they did just a few years ago. You have quite a few options to keep your coins safe and sound. Each choice offers unique perks for your peace of mind.
Hardware Wallets
Hardware wallets keep your cryptocurrency safe by holding your private keys offline. These small devices plug into your computer or phone only when you need them.
In 2026, leading US sellers offer models like the $99 Ledger Nano X or the $129 Trezor Safe 5. Hackers cannot reach coins inside a hardware wallet unless they steal the physical device and guess your PIN code.
Top hardware wallets share a few vital security features:
- Strong encryption standards to protect your stored recovery phrase.
- EAL6+ Secure Element chips, which are the exact same chips used in high-end passports.
- Mandatory physical button presses to confirm any outgoing transaction.
Software Wallets
Software wallets live on your computer or phone, giving you fast access to your digital assets. Many people use apps like MetaMask or the Phantom wallet for quick US daily trades.
These wallets rely on passwords and encryption to protect private keys from hackers. Still, malware and phishing attacks often expose your coins if you download fake software.
To fight this, newer options like the Zengo app use seedless onboarding. This specific tool has protected over 1.5 million users without a single hack.
Paper Wallets
Paper wallets offer a cheap way to protect your cryptocurrency from hackers. You simply print your private keys and addresses onto a page, often in QR code form. No internet connection touches this kind of digital asset backup. Hackers simply cannot steal what stays off the grid.
However, you must use strong ink that will not fade over time. Keep the paper away from water or fire, as there is no recovery if you destroy it. Because of these physical risks, most security experts now recommend skipping paper and using metal seed plates instead.
Multi-Signature Wallets
Multi-signature wallets need two or more people to approve any movement of digital assets. Hackers cannot steal your cryptocurrency with just one stolen private key.
For example, a family might set up three keys and require approval from two before spending coins. Many US businesses choose this method for strong risk management.
Using a multi-signature setup offers immediate benefits:
- It eliminates the single point of failure if a hacker compromises one device.
- It prevents a total loss if a team member accidentally loses their access credentials.
- It allows groups to manage large investment portfolios with shared oversight.
Projects like Casa offer these services with advanced cybersecurity features. Multi-signature adds another wall between bad actors and your cold storage funds.
Cold Storage Options for 2026
Cold storage methods keep your digital coins safe and completely offline. Let us look at which offline storage method fits your specific needs.
Air-Gapped Devices
Air-gapped devices stay offline at all times. They never connect to the internet, Wi-Fi, or Bluetooth. People use special hardware wallet models for this extra layer of cryptocurrency security.
Even malware on your computer cannot touch an air-gapped device because it stays isolated. Transferring data to or from an air-gapped wallet needs a QR code or a microSD card.
For instance, the SafePal S1 Pro uses a built-in camera to scan QR codes for transactions without ever touching a web connection. Banks and cybersecurity experts trust these setups for storing digital assets safely. Extra steps take time but stop most cyberattacks cold in their tracks.
Metal Seed Backups
Metal seed backups keep your recovery phrases safe from fire, water, and shocks. Unlike paper or plastic, marine-grade stainless steel plates do not burn or rot.
Many crypto users lost everything in house fires because their backup was just paper stuffed in a desk drawer. In 2026, premium metal backups provide true peace of mind.
Top choices in the US market include:
- The Cryptosteel Capsule, which stores letter tiles in a fireproof steel tube for about $99.
- The Billfodl is a $99 marine-grade steel plate that resists extreme heat and moisture.
- The Cryptotag Zeus is an aerospace-grade titanium plate that costs around $129.
These devices let you slide or punch metal letter tiles into a frame to record your recovery words. You store these plates in a locked box at home or at a bank’s safety deposit vault.
DIY Burner Wallets
Sometimes you need a quicker, safer way to make short-term crypto transactions. DIY burner wallets work like throwaway wallets for digital cash.
People create one with free wallet apps on old phones or laptops that never connect to the internet. These burner wallets give you a spot for quick trades or testing new projects without exposing your main stash.
Most folks use burner wallets once and then toss them out. If malware finds its way onto that device later, it cannot touch your real savings stored in long-term cold storage. Think of these as single-use gloves for handling hot coins safely.
Advanced Cold Wallet Security Features
Cold wallets now have clever tricks up their sleeves for extra safety. Some make hackers feel like they are trying to break into a bank vault with a toothpick.
Multi-Party Computation (MPC)
Multi-Party Computation splits your private key into pieces and stores them in different spots. No one person holds the full key at any time.
Hackers face a hard task since they must breach several places at once to steal digital assets. By 2025, over 58% of digital asset custody providers will have integrated MPC for maximum cryptocurrency security.
MPC wallets provide several distinct advantages:
- They completely remove the need to manage a vulnerable seed phrase.
- They require multiple devices to say yes before any money moves.
- They allow seamless account recovery if you lose your primary mobile phone.
Major platforms like Coinbase use MPC technology to make it much harder for cybercriminals to grab your funds. This layer acts like armor for your cryptocurrency.
Biometric Authentication
Biometric Authentication uses your body traits, like fingerprints, to guard your crypto wallets. This makes it incredibly tough for thieves to steal digital assets.
Copying a fingerprint is much harder than swiping a password. Hackers might crack passwords with fancy computers, but they cannot fake biometrics easily. In 2026, devices like the D’CENT Biometric Wallet offer built-in fingerprint scanners for about $139. Many users see faster logins, too. Just tap a finger on the scanner, and the wallet opens up securely.
Tamper-Resistant Hardware
Tamper-resistant hardware acts like a digital vault with muscle. These devices can spot someone trying to mess with them.
If anyone tries physical force, the built-in sensors wipe out your private keys instantly. Secure element chips use advanced shielding against drills or extreme heat.
Many cold storage tools will lock themselves or destroy data if they notice prying attempts. Such safeguards help keep your cryptocurrency safe from hacks and sneaky hands alike. Think of it as having a bodyguard for your digital assets who never sleeps.
Steps to Set Up a Secure Cold Wallet
Getting a cold wallet ready is easier than you might think. Follow these exact steps before putting any funds inside to guarantee your peace of mind.
Secure Procurement of Wallets
Buying a hardware wallet requires care and attention to detail.
- Always buy wallets directly from the official company website. Fake US sellers try to steal your cryptocurrency with tampered devices.
- Check if the wallet has modern security features like biometric logins or an EAL6+ secure chip.
- Make sure the hardware wallet package comes sealed and looks undamaged on arrival.
- Only update firmware after you check for real updates on the manufacturer’s verified webpage.
- Never buy secondhand wallets from auction sites like eBay, because a previous owner could extract your funds later.
Backing Up Recovery Phrases
Backing up recovery phrases keeps your cryptocurrency safe from disaster.
- Write your recovery phrase on paper using a pen, not a printer. Handwritten notes reduce risks from hackers.
- Store the paper copy in a locked safe at home or in a bank deposit box.
- Protect the paper from water damage by sealing it inside special waterproof pouches.
- Never take photos of your recovery phrase or type it into your phone. Hackers scan iCloud and Google Drive for these exact images.
- Use a metal plate made from 316 marine-grade stainless steel, like a Billfodl, for a permanent backup. Paper burns, but metal survives.
Performing a Dry Run Test
A dry run test checks if your cold storage setup works correctly. It helps you test asset protection without stress.
- Write down your recovery phrase on paper, away from all cameras or computers.
- Use that seed phrase to set up a new device, like a Trezor Safe 5.
- Send a tiny amount of cryptocurrency, like $5 worth of Bitcoin, to the new wallet.
- Wipe the device completely, then restore it using only your written backup phrase.
- Check that your $5 balance reappears successfully. This proves your backup works.
- Review each step for missing details before storing your life savings.
Enabling Layered Security Protocols
Layered security protects digital assets using a mix of strong tools.
- Use two-factor authentication for each exchange login to block hackers with stolen passwords.
- Require a physical button press from your hardware wallet before moving any coins.
- Set up fingerprint scans where possible for quick but secure access.
- Turn on email or app alerts for every transaction, so you spot odd activity fast.
- Use multi-signature approval rules needing more than one person’s permission before funds can move.
Best Practices for Safeguarding Your Cryptocurrency
Keep your digital assets safe with smart habits and regular checkups. Small actions now save you a massive headache later on.
Regularly Updating Wallet Firmware
New wallet updates help stop hackers dead in their tracks. Firmware updates fix security holes and add great new features.
- Most hardware wallet brands release updates every few months to close security gaps.
- Wallet makers use firmware upgrades to block new cyberattacks.
- Old firmware leaves your cryptocurrency wallet open to risks that hackers already know how to exploit.
- Before updating, always check the maker’s official website to avoid phishing traps.
- Most modern hardware wallets let you finish updates in under ten minutes.
Avoiding Public Wi-Fi for Transactions
Safe internet habits play a huge role in keeping your digital assets away from thieves.
- Public Wi-Fi at US airports or coffee shops lacks strong security, letting hackers snoop on your activity.
- Bad actors set up fake Wi-Fi hotspots with names similar to trusted ones, tricking users into connecting.
- If you enter private keys using public Wi-Fi, thieves capture sensitive data right off your device.
- Sticking to secure home networks reduces the risk of cyberattacks significantly.
- Using a trusted virtual private network like NordVPN gives extra protection by hiding your activity.
- Hardware wallet makers warn against sending funds while connected to open Wi-Fi.
Using Multi-Signature Approvals
Multi-signature approvals act like needing two distinct keys to open a safe deposit box.
- Each transaction needs approval from two or more devices, making scams much harder to execute.
- This method uses several private keys, meaning no single person can move your funds alone.
- If a thief steals one device, they still cannot steal your cryptocurrency.
- Most top hardware wallets now support multi-signature setups.
- Having multiple signers spreads responsibility and lessens the chance of costly mistakes.
Common Mistakes to Avoid
Small errors can open the door to big risks. Stay sharp, because some slips are incredibly easy to make.
Losing Private Keys
Losing private keys is a nightmare for any crypto holder. Private keys control your absolute access to digital assets. Without your private key, you lose all your crypto. Tech support cannot recover it for you. In fact, experts estimate millions of dollars in Bitcoin vanish each year simply because users lose their keys.
Here are the most common ways people lose their keys:
- Storing private keys on an internet-connected computer where malware can find them.
- Saving screenshots of recovery phrases in their phone’s photo gallery.
- Writing the phrase on a regular piece of paper that later gets thrown away by mistake.
If someone gets your key, they control your funds, and blockchain transactions are final.
Storing Seed Phrases Online
Storing your seed phrases online leads to absolute disaster. Hackers love an easy target, and cloud storage is a golden ticket. Cybercriminals use phishing scams to steal seed phrases from Google Drive or Apple iCloud. In early 2025, countless digital assets vanished due to seed phrase leaks traced directly back to online files.
Email accounts frequently fall victim to breaches, making them unsafe for sensitive information. Hackers use automated tools that scan your files for common names like “wallet_backup.txt”.
Security professionals urge users to favor offline cold storage options like hardware wallets or metal plates. Online convenience looks great until a hacker drains your account in sixty seconds.
Overlooking Regular Maintenance
Crypto wallets need routine care, just like your car. Skipping routine checks puts your digital assets at severe risk.
- Ignoring wallet firmware updates makes your assets easier to hack.
- Forgetting to test recovery phrases once a year leaves you clueless if you ever need them.
- Letting software wallets run on old operating systems invites dangerous malware.
- Not reviewing account activity means cybercriminals can slip in quietly.
- Allowing dust to settle on cold storage USB drives risks hardware failure from moisture.
Future Trends in Crypto Storage Security
Wallets in 2026 continue getting smarter and safer. Hardware wallets now use tiny fingerprint scanners, guaranteeing only you can access your digital assets.
Multi-party computation lets several devices help unlock a wallet, making it nearly impossible for thieves to grab your coins. Developers are even testing backup keys with secure chips that self-destruct if someone physically tampers with them.
New AI security tools spot odd transaction activity fast. These smart tools warn you of trouble before any funds leave your account. Metal seed backups are also getting lighter and tougher, offering incredible protection against fire or water damage. Technology keeps raising the bar, racing ahead as new threats appear across the web.
The Bottom Line
Learning how to secure crypto storage in 2026 demands active steps and smart choices. Using cold storage protects digital assets from aggressive cyberattacks.
Always protect private keys at all costs. If you lose them, your coins are gone for good. Mix your security tools by using layered protection, like multi-signature setups or biometric hardware locks.
Hackers become much more clever every year. In 2026, skipping software updates is exactly like leaving your front door wide open in a busy city. Keep asset protection at the top of your list by backing up seed phrases offline with sturdy metal plates. Digital wallets change constantly, but strong cybersecurity habits never go out of style.