In the evolving digital landscape, Web3 technology is reshaping how we interact online. As decentralized applications (dApps) and blockchain technologies gain popularity, protecting digital identity has become crucial.
Traditional identity protection methods often rely on centralized authorities, leaving users vulnerable to data breaches and hacks.
Web3 tools provide a decentralized and secure approach to safeguarding your online presence, ensuring greater privacy, security, and control over personal data.
This article explores 10 Web3 tools to protect your digital identity in an increasingly decentralized world.
Why Web3 Tools Are Essential for Digital Identity Protection
- Data Breaches: Centralized servers store vast amounts of user data, making them prime targets for hackers.
- Identity Theft: Unauthorized access to personal details can lead to financial fraud and impersonation.
- Privacy Concerns: Many online platforms collect and monetize user data without consent.
How Web3 Enhances Digital Identity Security
- Decentralization: Eliminates reliance on single points of failure.
- Self-Sovereign Identity (SSI): Users maintain full control over their data.
- Enhanced Privacy: Cryptographic techniques like zero-knowledge proofs protect identity details.
- Interoperability: Identity credentials can be used across multiple dApps and blockchain networks.
10 Web3 Tools to Protect Your Digital Identity
Below are some of the best Web3 tools designed to enhance identity security and privacy.
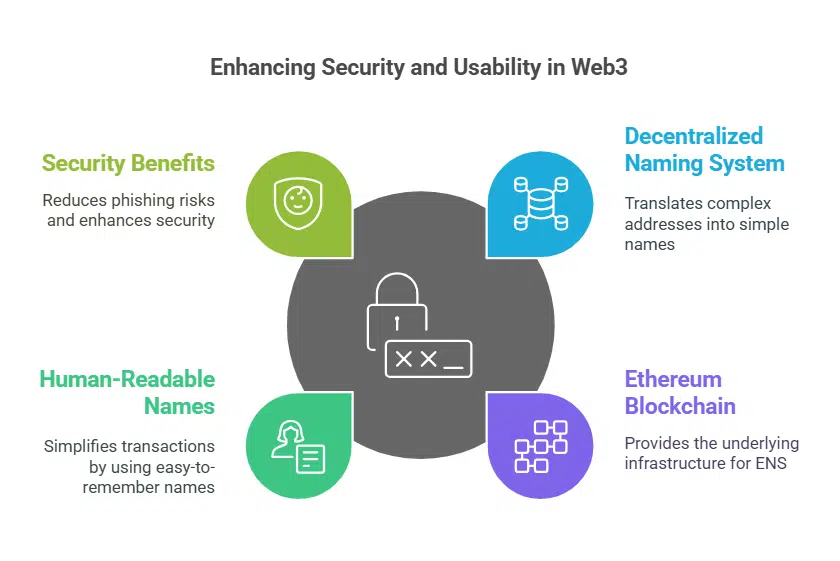
1. ENS (Ethereum Name Service)
ENS is a decentralized naming system that replaces complex blockchain addresses with human-readable domain names. By converting long, alphanumeric wallet addresses into easily recognizable names, ENS minimizes errors in transactions and enhances overall security.
It reduces the risk of phishing attacks, prevents address misinterpretation, and enables a more user-friendly experience for interacting with Ethereum-based services.
ENS is widely adopted within the Web3 ecosystem, providing seamless integrations with decentralized applications, wallets, and smart contracts.
Key Details:
| Feature | Description |
| Type | Decentralized domain service |
| Blockchain | Ethereum |
| Security Benefit | Reduces phishing risks by using readable addresses |
Why Use ENS?
- Simplifies transactions with human-readable wallet names.
- Prevents address spoofing and phishing attacks.
- Works across various Ethereum-based dApps.
2. Unstoppable Domains
Unstoppable Domains provides blockchain-based domain names that offer censorship-resistant, self-owned web identities.
Unlike traditional domains controlled by centralized registrars, these domains give users full ownership, eliminating risks of domain seizures and censorship.
They support a variety of blockchain networks, ensuring seamless integration with decentralized applications.
Additionally, they enable users to associate wallet addresses, making cryptocurrency transactions simpler and more secure.
Key Details:
| Feature | Description |
| Type | Blockchain-based domain service |
| Blockchain | Ethereum, Polygon, Zilliqa |
| Security Benefit | Eliminates need for third-party domain management |
Why Use Unstoppable Domains?
- Provides a single domain for wallets, websites, and logins.
- Censorship-resistant with full user ownership.
- No renewal fees, unlike traditional domains.
3. Sovrin
Sovrin is a decentralized identity network that allows users to manage their credentials securely through self-sovereign identity solutions.
By leveraging blockchain technology, Sovrin eliminates reliance on centralized identity providers, giving users complete control over their personal information.
The platform enables verifiable, cryptographic identity authentication, allowing individuals and organizations to establish trusted interactions without compromising privacy.
Sovrin is widely recognized for its ability to provide scalable, secure, and privacy-centric identity solutions for various industries, including finance, healthcare, and government services.
Key Details:
| Feature | Description |
| Type | Self-sovereign identity system |
| Blockchain | Hyperledger Indy |
| Security Benefit | Users control their identity data without intermediaries |
Why Use Sovrin?
- Provides verifiable digital credentials for secure authentication.
- Enables trustless identity verification.
- Prevents unauthorized access to sensitive personal data.
4. Civic
Civic offers decentralized identity verification services that allow users to prove their identity without sharing excessive personal information.
By utilizing blockchain technology and biometric authentication, Civic ensures that users retain full control over their credentials while minimizing the risk of identity theft.
The platform provides seamless and secure login solutions without requiring traditional passwords, offering businesses and individuals a robust alternative to centralized identity management.
Civic’s services are widely used in industries requiring Know Your Customer (KYC) compliance, enabling organizations to verify identities without compromising user privacy.
Key Details:
| Feature | Description |
| Type | Decentralized identity verification |
| Blockchain | Ethereum |
| Security Benefit | Allows for secure login without passwords |
Why Use Civic?
- Reduces the risk of identity theft through biometric authentication.
- Provides KYC-compliant solutions for businesses.
- Users retain control over their personal data.
5. uPort
uPort provides decentralized identity management tools that empower users to authenticate themselves securely on the blockchain. It enables individuals to create and control their own self-sovereign identity without the need for a central authority.
By using cryptographic credentials, uPort allows users to verify and share their identity in a trustless manner while maintaining full privacy.
The platform is designed to integrate seamlessly with various dApps and services, making it a versatile solution for Web3 identity verification and authentication.
Key Details:
| Feature | Description |
| Type | Identity management protocol |
| Blockchain | Ethereum |
| Security Benefit | Eliminates reliance on centralized identity providers |
Why Use uPort?
- Provides verifiable, self-owned digital identities.
- Enables secure logins without relying on third parties.
- Supports multi-chain interoperability.
6. BrightID
BrightID is a decentralized identity verification tool designed to prevent sybil attacks and ensure fair participation in Web3 communities. Unlike traditional verification systems that rely on centralized authorities, BrightID uses a unique social graph approach, where users verify each other through trusted connections.
This enables privacy-preserving identity authentication without requiring personally identifiable information.
By leveraging cryptographic techniques and decentralized networking, BrightID ensures that online communities, governance systems, and reward distribution mechanisms remain resistant to fraudulent multi-account abuse.
Key Details:
| Feature | Description |
| Type | Decentralized identity verification |
| Blockchain | Multi-chain compatible |
| Security Benefit | Ensures real user verification without compromising privacy |
Why Use BrightID?
- Prevents bots and duplicate identities in online communities.
- Uses social verification instead of personal data sharing.
- Ideal for decentralized governance and fair voting.
7. Fractal
Fractal is a decentralized identity and authentication protocol that ensures privacy-first identity verification for Web3 applications. It leverages blockchain technology to enable secure, trustless authentication, allowing users to prove their identities without relying on centralized entities.
With an emphasis on self-sovereign identity, Fractal empowers individuals to have complete control over their credentials, minimizing the risk of identity theft and data breaches.
The platform integrates seamlessly with dApps, making it a reliable solution for businesses and individuals who prioritize security and privacy in the Web3 ecosystem.
Additionally, Fractal supports compliance with KYC and AML regulations, providing a balance between user anonymity and regulatory adherence.
Key Details:
| Feature | Description |
| Type | Privacy-focused identity verification |
| Blockchain | Ethereum, Polkadot |
| Security Benefit | Ensures secure and private authentication |
Why Use Fractal?
- Enables private identity verification without exposing sensitive data.
- Integrates seamlessly with decentralized applications.
- Prevents identity fraud through cryptographic verification.
8. SelfKey
SelfKey is a blockchain-based self-sovereign identity system that allows users to control and manage their identity credentials securely. By leveraging decentralized technology, SelfKey ensures that individuals and businesses can create, own, and manage their identities without relying on third-party intermediaries.
The platform offers a comprehensive suite of identity verification and KYC compliance tools, enabling users to access financial services, exchanges, and various online platforms with ease.
SelfKey also includes an integrated identity wallet, allowing users to securely store and manage multiple identity documents while maintaining full privacy and control.
Its zero-knowledge proof verification ensures that identity credentials are only shared when absolutely necessary, reducing exposure to potential data breaches and identity theft.
Key Details:
| Feature | Description |
| Type | Self-sovereign identity management |
| Blockchain | Ethereum |
| Security Benefit | Gives users full control over their identity data |
Why Use SelfKey?
- Stores personal identity data securely in a decentralized manner.
- Enables seamless KYC verification for businesses and individuals.
- Provides an identity wallet for managing multiple credentials.
9. Veramo
Veramo is an open-source decentralized identity framework that allows developers to build applications with verifiable credentials and DID (Decentralized Identifiers). It provides a flexible and extensible identity management system that supports multiple identity providers and verification mechanisms.
Veramo enables developers to create, issue, and verify digital credentials in a decentralized and trustless environment, ensuring security and privacy for end users.
The framework integrates seamlessly with various blockchain networks and supports cross-chain interoperability, making it a versatile tool for Web3 identity solutions.
Veramo also includes robust APIs, SDKs, and plugins to facilitate identity integration for both decentralized applications and traditional enterprise solutions.
Key Details:
| Feature | Description |
| Type | Decentralized identity framework |
| Blockchain | Multi-chain compatible |
| Security Benefit | Ensures user-controlled verifiable credentials |
Why Use Veramo?
- Provides a flexible and modular identity management system.
- Supports multiple identity verification methods.
- Helps developers integrate identity solutions into their applications.
10. Onfido
Onfido is a leading AI-driven identity verification platform that uses machine learning to authenticate users while maintaining privacy and security.
The platform leverages advanced biometric recognition and document verification techniques to ensure secure user authentication across various industries, including finance, healthcare, and Web3 applications.
By analyzing identity documents and facial biometrics in real-time, Onfido enhances fraud detection and minimizes the risks of identity theft.
The service also incorporates liveness detection, ensuring that digital interactions are genuine and not compromised by deepfake technology or synthetic identities.
Onfido’s API-driven approach allows seamless integration with Web3 platforms, facilitating secure onboarding and authentication without compromising user privacy.
Key Details:
| Feature | Description |
| Type | AI-powered identity verification |
| Blockchain | Multi-chain compatible |
| Security Benefit | Uses biometrics and AI for secure authentication |
Why Use Onfido?
- Uses facial recognition and biometric authentication for security.
- Prevents fraud through AI-powered verification.
- Widely used by financial institutions and Web3 platforms.
Takeaways
The rise of Web3 is transforming digital identity management by eliminating reliance on centralized authorities and increasing user control. The tools listed above provide innovative ways to protect your identity, enhance security, and maintain privacy in the decentralized ecosystem.
Whether securing a blockchain-based domain or verifying identity through zero-knowledge proofs, adopting Web3 identity protection tools is a crucial step toward a safer digital future.
If you’re looking to strengthen your online security, consider integrating these Web3 tools to safeguard your digital identity today!