Out of nowhere, some terms catch fire across the web when chatter spikes around rumors or digital events. Take “thejavasea.me leaks aio-tlp371” – odd-looking, yes, but it’s part of a larger pattern involving exposed data, online safety concerns, and how people piece together clues about possible security lapses. Though confusing on the surface, phrases like this often mirror real worries within tech circles. Meaning emerges once context settles in. What seems random today might point to something concrete tomorrow. Curiosity drives much of what spreads through forums and message boards. Behind strings of letters and dots, users search for truth amid noise.
This piece looks at what this term could mean, where its search interest comes from, because understanding leaks matters more now. Since privacy gaps grow wider each day, yet people keep sharing freely online. A clearer view helps separate fact from noise, while avoiding fuel for reckless actions. Instead of spreading guesses, or pushing risky curiosity, staying informed makes better sense. Context shapes how we act, especially when personal data slips into public spaces by accident. Staying aware beats reacting fast without thinking first.
The Growing Interest Around thejavasea.me leaks aio-tlp371 me
Talk of thejavasea.me leaks aio-tlp371 points to a web address brought up in different corners of the internet. When sites tie into leaks, alarms go off fast since secrets might be spilling out. These places might collect what’s already public, store things users send in, or simply stir rumors – no matter the case, their names pop up once people start debating safety online. As tension around personal data grows, so does chatter about domains like this one.
Spotting real cyber problems means looking past the noise online. Just because someone says “leak” doesn’t mean data actually spilled. Trends around such words often grow from guesses, mistakes, or small group talk instead of proof. What feels widespread might just be echo.
Understanding Leaks in Today’s Digital World
A drip of info on the web often spreads fast. That slip could mean secret data floating around. Sometimes it’s files showing up out of nowhere. Other times, private messages start doing rounds. A gap in security might let things through. Hidden details get exposed without warning. Info meant to stay closed gets found open
- Unauthorized exposure of private data
- Early release of digital content
- Shared databases circulating without consent
- Misinterpreted claims within online forums
Leaked stuff once meant only secret data slipping out – think logins or private messages falling into the wrong hands. These days, online chatter uses the term for almost any surprise reveal, whether it’s a hidden game level or files claimed to be stolen.
When things are unclear, people start typing searches such as “thejavasea.me leaks aio-tlp371,” trying to confirm bits they’ve stumbled upon online.
What thejavasea.me leaks aio-tlp371 Might Mean?
A closer look at “thejavasea.me leaks aio-tlp371” suggests it’s more of a backstage tag than something meant for public use. When leaks come up, labels like this often pop out – not names people know, but markers behind the scenes. These bits usually point to system tracking, maybe how files get sorted when nobody’s watching
- Archive names
- Compiled data collections
- Project or batch identifiers
- Placeholder codes used within communities
Hard to pin down exactly when there’s no solid proof available online. That lack of clarity? It keeps people searching, trying to figure out if it’s an actual security leak, some glitch in the system, or just chatter spreading online.
Leak related keywords spread through casual online talk
Curiosity drives most of these spikes. People see strange words tied to hidden things – immediately, their minds want answers. Something about mystery pulls attention fast. Often, it’s not planned. A term appears out of nowhere online, then spreads without warning. The unknown tugs harder when it feels forbidden. Attention grows quietly at first, then floods in waves.
Messaging apps, online forums, social networks – these spaces speed things up. One unclear image or comment might spark loads of guesses. When searches for that phrase grow, systems push it further into view. That pushes the loop onward.
This happens because people want answers fast – more than they care about checking if those answers are right, particularly around hacking worries or data exposure. Sometimes urgency pushes truth aside when screens go dark and secrets feel exposed.
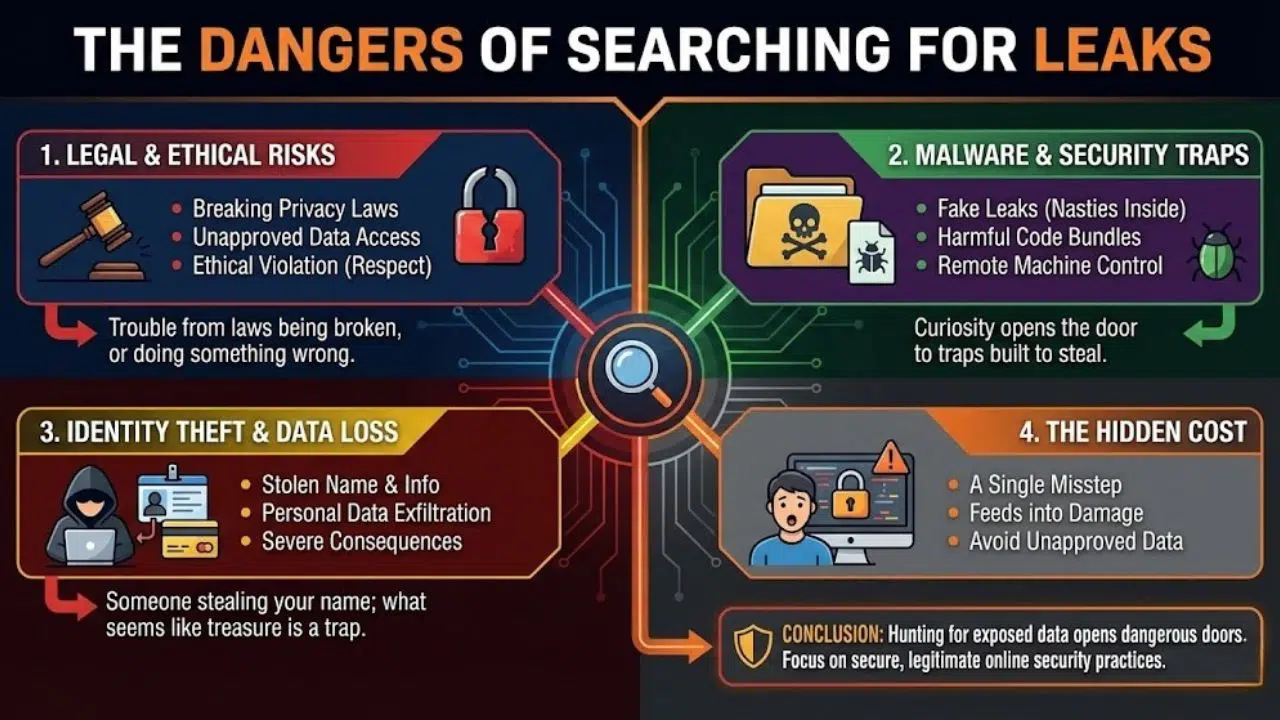
The Dangers of Searching for Leaks
Looking into online security can help, yet hunting for exposed data opens dangerous doors. Trouble might come from laws being broken, viruses sneaking in, someone stealing your name, or doing something that just feels wrong.
Curiosity often opens the door – fake leaks hide nasty surprises inside download packages. These bundles carry harmful code instead of real data, waiting for someone to click. A single misstep can hand control of your machine to strangers online. What seems like a treasure might just be a trap built to steal everything.
Looking at unapproved data might break privacy rules, also going against basic online respect. Stumbling on private details, even without sharing them, still feeds into something damaging.
Cybersecurity Awareness Is Important
A whisper about data slipping out shows how well people understand online safety. Real or just talk, each moment like this can remind folks to guard their info better.
Good habits with passwords matter a lot. When one login shows up in a leak, using it elsewhere opens many doors. An extra check at sign-in blocks more threats, even when codes get out.
Finding out if your data has been exposed? Checking with tools like Have I Been Pwned gives a clearer picture. Staying aware of account safety just makes sense – it shows what risks might already be real.
The Role of Misinformation in Leak Stories
Some words tied to leaks come from real events. Others pop up without proof. False stories spread fast on the web. A single image taken wrong can look like evidence. Made-up reports show up now and then. Old data gets reused, dressed as fresh news. Names change but the facts stay shaky.
Thinking carefully matters when checking claims. Trusted proof usually appears through well-known cyber experts, public reports, or dependable tech news sources. When that kind of backup is missing, proceed with care. A lack of solid backing tends to mean risks could be higher.
What separates fact-driven accounts from neighborhood rumors matters when sorting truth online. Clear thinking depends on it.
Privacy Ethics and Digital Responsibility
Not just about broken systems, leaks often drag ethics into the spotlight. When private details spill, actual people face consequences – no permission asked. Laughing off stolen info makes light of something serious. Privacy stops being abstract when names and lives show up in public logs.
Mind how far you reach online, stay clear of files not meant for you, while helping guard information others trust you with. See right from wrong just like spotting digital threats – both shape safer habits across the web. What counts shows up in small choices made daily without praise.
People Keep Looking Up Leak Terms
Curiosity keeps people hunting leaks even when it’s risky – something about not knowing pulls at them. Fear slips in too, that nagging sense that something important is hidden. Wanting secrets others don’t have plays a role as well. Online masks make hesitation fade, one small click at a time.
What people search shapes what shows up online. If plenty start typing something such as “thejavasea.me leaks aio-tlp371,” that string sticks around in results, true or not.
What happens online shows that getting noticed doesn’t mean being trusted. Sometimes clicks come without credibility tagging along. Attention piles up where proof is thin. A crowd gathers even when substance stays absent. Visibility grows while verification lags behind.
Understanding Unclear Internet Terms
Finding strange terms in cybersecurity? Slow down first. Jumping to worst-case scenarios misses quieter truths – maybe it’s just jargon, maybe a glitch, perhaps someone made an error. Look around corners before deciding what it means
A term like that might come from behind-the-scenes lingo, tight-knit groups, trial data, or keywords built just for search engines. Without solid sources backing it up, assumptions lose weight fast. Instead of jumping to answers, pause – proof matters most here.
Stillness in reading keeps panic away, yet sharpens attention.
Improving Safety of Personal Online Information
Curiosity sparked by leaks might nudge you to check how well your accounts are locked down. When passwords get refreshed, risk drops without drama. Multi-step login steps pop up extra shields where hackers look for weak spots. Recovery options? Worth scanning once in a while – holes hide there. Software patches roll out quietly, yet they plug gaps before trouble slips through.
Fresh thinking shapes real protection online. Strong routines block risks even when threats aren’t making headlines yet.
The Bigger Picture in Leak Patterns
A single phrase – “thejavasea.me leaks aio-tlp371” – can ripple across screens before anyone grasps its roots. Information races ahead, yet understanding lags behind. People moving through today’s web face a steady pull between wanting to know and needing to stay alert. Clarity rarely keeps pace with speed.
Today, knowing about cyber risks means going beyond just tech skills. Questioning things that aren’t proven becomes key. Sticking to safer web habits takes effort. Seeing how privacy affects people helps too.
Final Thoughts on thejavasea.me leaks aio-tlp371
Starting off oddly, “thejavasea.me leaks aio-tlp371” draws eyes without explaining itself. Though facts stay hazy, talk around it shows how people react when tech feels risky. Conversations shift toward habits online – what gets noticed, what gets ignored. Awareness matters more now simply because confusion spreads fast. Clarity rarely leads; curiosity does.
Starting fresh each day helps more than fixating on vague rumors about data leaks. Staying sharp online means building better routines – like double checking facts with trusted outlets, while handling delicate subjects thoughtfully. When news moves fast, clear thinking shows up stronger than quick reactions. Careful steps matter most when everything feels rushed.