Mid-market companies now juggle between 200 and 400 cloud applications, and nearly half of those live completely outside of IT’s view. When any department manager with a corporate card can spin up a new software trial in minutes, your technology stack balloons before anyone even notices.
This friction-free adoption drives immediate productivity but creates a massive blind spot for your organization. Implementing effective SaaS sprawl management is the only way to regain control over your security posture and stop bleeding budget on unused licenses. We are going to walk through exactly how to identify hidden applications, consolidate your redundant tools, and build guardrails that keep your software ecosystem lean and efficient.
The Root Causes Behind the Expansion of Cloud Software
Decentralized purchasing is the primary driver of software bloat in modern companies. Product vendors intentionally optimize for frictionless sign-ups, making it incredibly easy for individual employees to adopt new tools without submitting a formal IT request. By the time the technology department discovers the new application, the contract is already live and company data is already circulating within it. Lean IT teams simply do not have the bandwidth to track every single browser extension or cloud platform manually. To successfully execute SaaS sprawl management, you have to understand that this chaotic expansion is a systemic organizational issue rather than just a technology problem.
Here is a breakdown of the specific factors driving unauthorized software adoption across different departments:
| Root Cause | Operational Reality |
| Decentralized Budgets | Department heads possess independent discretionary funds to buy niche tools |
| Frictionless Trials | Freemium models bypass traditional procurement and security reviews entirely |
| Hybrid Work Models | Remote employees seek out localized solutions for their immediate workflow needs |
| Specialized AI Tools | Teams rapidly adopt fragmented artificial intelligence apps for single-use tasks |
Identifying these underlying behaviors is the first step toward changing the way your organization approaches software procurement.
Shifting from Gatekeeping to Collaborative Procurement
IT departments must stop acting as roadblocks and start positioning themselves as strategic buying partners. When employees feel supported in their software requests, they are far less likely to hide their tech purchases from the security team.
Best for: Organizations struggling with high rates of shadow IT and departmental silos.
Why We Chose It: Collaboration significantly reduces the friction that typically drives employees to bypass security protocols.
Things to consider: It requires establishing a dedicated software review board that meets weekly to prevent request bottlenecks.
Identifying the Real Financial Impact of Unused Licenses
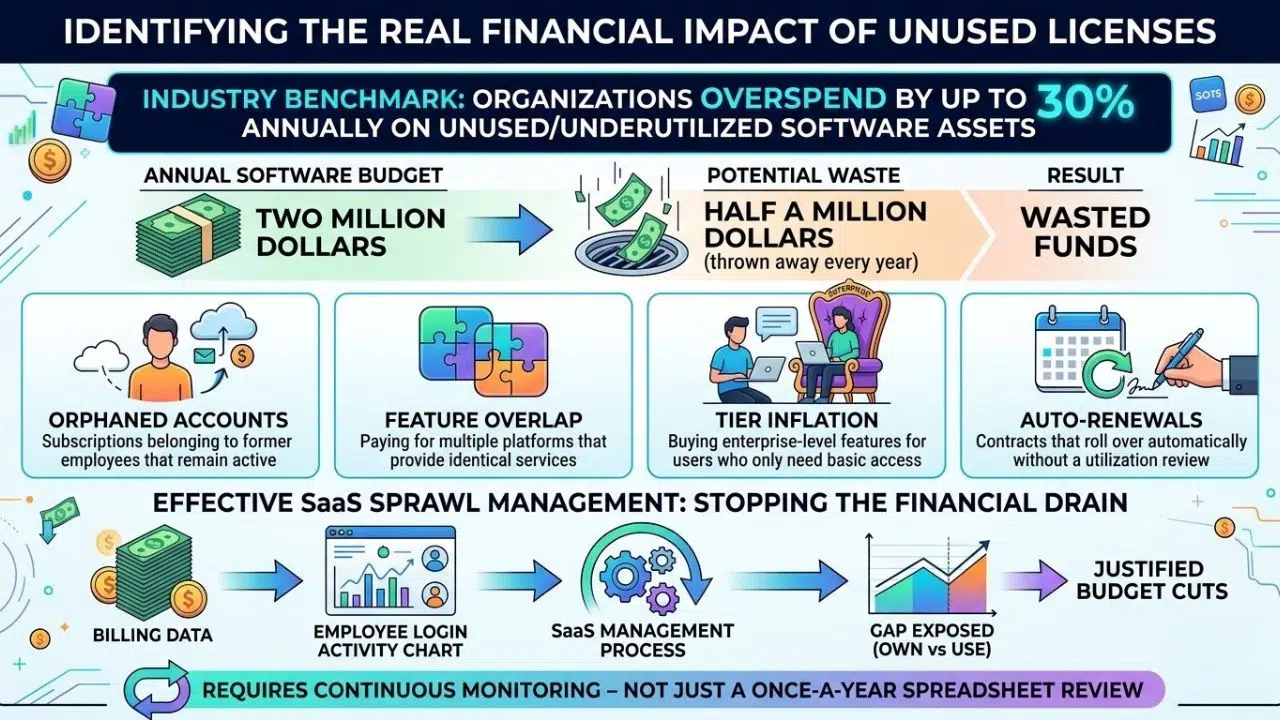
Industry benchmarks show that organizations overspend by up to 30 percent annually on unused or underutilized software assets. If your annual software budget is two million dollars, you are potentially throwing away half a million dollars every single year. These wasted funds stem from employees holding premium licenses they never use or departments paying for applications that duplicate existing functionality. Effective SaaS sprawl management directly targets this financial leakage by matching your billing data against actual employee login activity. Once you expose the gap between what you own and what you actually use, justifying budget cuts becomes a straightforward mathematical exercise.
The table below illustrates the typical areas where software budgets leak unnoticed:
| Expense Category | Description of Waste |
| Orphaned Accounts | Subscriptions belonging to former employees that remain active |
| Feature Overlap | Paying for multiple platforms that provide identical services |
| Tier Inflation | Buying enterprise-level features for users who only need basic access |
| Auto-Renewals | Contracts that roll over automatically without a utilization review |
Stopping this financial drain requires continuous monitoring rather than just a once-a-year spreadsheet review.
Calculating Your True Software Utilization Rate
You have to dig into the analytics dashboard of every major application to see who has logged in within the last thirty days. If an employee has not accessed a platform in a month, their premium license should immediately downgrade to a free viewer role or be revoked entirely.
Best for: Finance and IT teams looking to instantly free up budget for new strategic initiatives.
Why We Chose It: Hard login data removes all emotional attachment and departmental politics from license reduction conversations.
Things to consider: Vendor reporting dashboards are notoriously confusing, making it difficult to extract accurate active user metrics.
How to Conduct a Comprehensive SaaS Audit
You cannot manage a software ecosystem that you cannot accurately see or measure. An audit requires pulling objective data from expense reports, single sign-on providers, and browser endpoints to find every active subscription in the company. Traditional SaaS sprawl management relies heavily on asking department heads what they use, which always results in an incomplete picture. You need an automated discovery process that flags applications bypassing your official security gates. This true baseline of reality allows you to see the exact size of your shadow IT problem and immediately begin the cleanup process.
The following table outlines the essential data sources you must review during your discovery phase:
| Discovery Source | Information Uncovered |
| Expense Reports | Credit card transactions revealing unapproved departmental software purchases |
| Identity Providers | Applications connected through your central authentication systems |
| Email Scans | Welcome emails and invoice receipts from unknown software vendors |
| Endpoint Agents | Browser extensions and lightweight utilities installed directly on company laptops |
Gathering this intelligence gives you the leverage needed to confront redundant spending across the business.
Categorizing the Stack and Eliminating Redundancies
Group your discovered applications into functional categories to reveal immediate opportunities for consolidation. Discovering that your company pays for Slack, Microsoft Teams, and a separate project management chat tool simultaneously is a classic example of communication bloat that you can easily eliminate.
Best for: Mid-market companies that have grown rapidly through mergers or aggressive hiring.
Why We Chose It: Categorization provides the clearest visual proof of wasted resources to executive leadership.
Things to consider: You will face pushback from individual teams who prefer their specific niche tools over the centralized enterprise standard.
Building Robust SaaS Governance Policies
Once you clean up the existing software mess, you must build guardrails to prevent the chaos from immediately returning. A solid governance policy dictates exactly how new software is requested, vetted, and approved across the entire organization. This structural framework is the absolute backbone of sustainable SaaS sprawl management because it shifts accountability back to the actual software users. Clear policies ensure that legal, financial, and security reviews happen before a single line of company data enters a new application. By standardizing this workflow, you eliminate the frantic, reactive troubleshooting that plagues modern IT departments.
A well-structured governance framework should clearly outline responsibilities across different phases of the software lifecycle:
| Governance Phase | Key Responsibility |
| Initial Request | Employee submits a detailed business case and list of required features |
| Security Vetting | IT reviews compliance standards, data privacy, and necessary integrations |
| Financial Approval | Procurement negotiates contract terms and consolidates billing schedules |
| Lifecycle Review | Management conducts quarterly checks on tool utilization and overall ROI |
Implementing these rules requires serious executive sponsorship to ensure department heads actually comply with the new workflows.
Implementing the One In, One Out Rule
To keep your software portfolio incredibly lean, require teams to retire an old application before adopting a new one in the same exact category. If the marketing team desperately wants a new analytics platform, they need to demonstrate why the current one is failing and commit to fully migrating off it.
Best for: Fast-growing departments prone to endlessly chasing the latest software trends.
Why We Chose It: It forces employees to critically evaluate the true necessity of a new purchase before spending company money.
Things to consider: Ensure the new application truly replaces all the critical functionality of the retired one to avoid massive workflow disruptions.
Automating User Lifecycle Management
Manual onboarding and offboarding processes are massive contributors to software bloat and severe security vulnerabilities. When an employee leaves the company, relying on a spreadsheet checklist to revoke their access across fifty different applications guarantees that something will be missed. Automating these exact workflows is a non-negotiable aspect of modern SaaS sprawl management. It instantly reclaims expensive licenses for reuse and secures sensitive company data from unauthorized access by former staff. Connecting your human resources system directly to your identity management platform creates a seamless, error-free access pipeline.
Here is a comparison of manual lifecycle management versus an automated approach:
| Process | Manual Management | Automated Lifecycle |
| Provisioning | Hours or days of waiting for IT ticket resolution | Instant access via predefined, role-based templates |
| Deprovisioning | High risk of orphaned accounts remaining active | Immediate access revocation across all connected applications |
| License Reallocation | Rarely tracked properly, leading to continuous over-purchasing | Licenses are instantly returned to the available company pool |
| Audit Readiness | Chaotic, defensive data gathering right before an inspection | Real-time, continuous compliance logs ready for immediate review |
Taking the human element out of routine access management frees up your technology team to tackle actual strategic problems.
Leveraging Zero-Touch IT Operations
By integrating systems natively, you can trigger software provisioning the exact moment a new hire is added to the payroll software. Conversely, marking an employee as terminated in the system instantly severs all access tokens, locks their email, and transfers their cloud files to their manager.
Best for: Mid-to-large enterprises dealing with high employee turnover or managing seasonal contractors.
Why We Chose It: It completely eliminates human oversight from the most vulnerable access points in your entire corporate network.
Things to consider: The initial technical setup requires incredibly complex mapping of role-based access controls across every single department.
Deploying a SaaS Management Platform
Spreadsheets simply cannot keep up with the dynamic nature of cloud software licensing, unexpected pricing changes, and fluctuating user adoption rates. A dedicated SaaS Management Platform acts as the central command center for your entire technology stack. Deploying one of these platforms elevates your SaaS sprawl management from a painful reactive cleanup project to a highly proactive optimization strategy. These tools continuously scan your environment to expose unauthorized applications, alert you to upcoming renewals, and highlight underutilized premium licenses. Having a single source of truth allows you to negotiate with software vendors from a position of absolute data-backed strength.
When evaluating a management platform, prioritize systems that offer the following core technical capabilities:
| Feature | Business Value |
| Continuous Discovery | Automatically detects unapproved applications actively bypassing your single sign-on portal |
| Usage Intelligence | Tracks actual active login frequency versus the total number of paid seats |
| Renewal Alerts | Prevents automatic contract renewals on unwanted or abandoned software subscriptions |
| Automated Workflows | Executes bulk employee offboarding and instant license reclamation across the stack |
Selecting the right software partner is the most crucial step for achieving long-term visibility and financial control.
Choosing the Right Tool for Your Stack
The market is filled with powerful platforms explicitly designed to tackle software bloat and hidden costs. You need a system that integrates completely natively with your existing identity provider and financial software to pull highly accurate usage and spend data.
Best for: Lean technology teams managing highly complex, hybrid software environments across multiple global offices.
Why We Chose It: These dedicated platforms replace guessing with hard data, consistently proving their financial return on investment within the first quarter.
Things to consider: The initial integration phase will likely uncover a shocking amount of shadow IT that requires immediate and careful triage.
Fostering a Culture of Software Accountability
Technology alone will not solve the problem if your company culture encourages reckless software acquisition. You have to educate your employees about the severe security risks associated with plugging third-party applications into your corporate data environment. When staff members understand that a random productivity tool could expose client data to hackers, they become much more cautious about bypassing security protocols. Good SaaS sprawl management requires continuous communication between IT, finance, and the everyday users doing the actual work. Make your approved software catalog highly visible and incredibly easy to access so employees do not feel the need to go rogue.
Here are the specific communication strategies to keep your teams aligned with software policies:
| Strategy | Implementation Method |
| Regular Training | Include software security and procurement rules in all new hire onboarding sessions |
| Visible Dashboards | Share department-level software spending metrics openly to encourage financial accountability |
| Streamlined Requests | Create a simple, transparent IT ticketing portal specifically for requesting new applications |
| Feedback Loops | Survey employees annually to see if the currently approved tools actually meet their needs |
Empowering your workforce with the right tools while enforcing sensible boundaries is the ultimate goal of software governance.
Maintaining Long-Term Operational Hygiene
Clean your digital house regularly by scheduling quarterly reviews of every major software contract. Look closely at newly acquired tools, changing usage patterns among your staff, and potential security vulnerabilities that have emerged since the last check.
Best for: Organizations that want to prevent slow, silent software creep from destroying their IT budget over time.
Why We Chose It: Routine maintenance is drastically cheaper and far less disruptive than executing a massive corporate software purge every three years.
Things to consider: It requires dedicated calendar time and strict discipline from IT leadership to avoid postponing these critical reviews.
Frequently Asked Questions About SaaS Sprawl Management
What is the first step in effective SaaS sprawl management?
The absolute first step is discovery, because you cannot manage what you cannot see. Start by running a full company-wide audit. Pull data from expense reports, single sign-on (SSO) systems, and browser agents to uncover every single application your team is actively using, especially the hidden ones.
How does shadow IT contribute to software bloat?
Shadow IT happens when employees or department heads buy software without getting approval from the IT department. Since it takes just a few minutes to swipe a corporate card for a new monthly subscription, unvetted apps quickly multiply. This frictionless buying creates massive sprawl and serious security blind spots across your network.
Can managing SaaS sprawl actually save my company money?
Absolutely. Industry data shows most companies waste up to 30 percent of their software budget on abandoned licenses, redundant tools, and forgotten auto-renewals. A solid management strategy directly targets and cuts these specific wasted costs, putting real money back into your IT budget.
Who should be responsible for monitoring the software stack?
While IT typically leads the charge, successful management is a team effort. IT handles security and integration, finance monitors the billing and contract renewals, and department heads must take accountability for the actual utilization of the tools they request.
Final Thoughts
Managing your software shouldn’t feel like an endless game of whack-a-mole. While the rapid growth of cloud applications gives your teams incredible flexibility, letting it run wild burns through your budget and opens up nasty security loopholes. Effective SaaS sprawl management is ultimately about shifting your organization from a reactive cleanup mode to a proactive, strategic posture.
Once you get true visibility into your technology stack, cut the dead weight, and set up clear, frictionless guidelines for future purchases, you put your company back in the driver’s seat. Start small with a thorough discovery audit, collaborate closely with your department heads to understand their needs, and watch how quickly your unnecessary IT waste disappears.