We are voluntarily locking our most valuable digital assets behind a screen door with a broken latch. We expect a simple string of text to protect our bank accounts, our medical histories, and our corporate networks against automated machines capable of guessing billions of combinations per second. The end of traditional passwords is not a feature update or a polite suggestion from your local IT department. It is a fundamental survival requirement for our online lives. We have treated the alphanumeric login as a heavy vault door for decades, but the math simply no longer supports the illusion of safety.
As we navigate an incredibly volatile digital landscape this year, the shift toward a passwordless existence is no longer about saving a few seconds at the login screen. It is a necessary and urgent upgrade to our collective digital safety that we can no longer afford to ignore.
The Catalyst For Change
The sheer scale of our vulnerability was laid bare in early 2026 when a massive data dump released over sixteen billion compromised records onto the dark web. Security researchers called it the Mother of All Breaches. This catastrophic event proved that our reliance on shared secrets is a completely failing strategy. We are watching a global digital infrastructure collapse under the weight of its own flawed design.
When a major regional healthcare network in the Midwest went offline for a week and cancelled hundreds of critical surgeries last month, it was not due to a sophisticated algorithmic hack by a rogue artificial intelligence. It happened because a senior administrator used a pet name and a birth year to secure a central patient database. A single point of human failure brought a massive medical facility to its knees. The hackers did not break in. They simply logged in.
The Failure of Mandated Complexity
The corporate response to these breaches has historically been a tired playbook of mandated complexity. Administrators force you to add special characters, numbers, and capital letters while demanding you change the phrase every ninety days. These security measures have never actually stopped hackers. They merely frustrate everyday users into writing their credentials on sticky notes or reusing the exact same weak phrase across fifty different websites.
The technology industry essentially gaslit the public into believing these security breaches were a user failure. Developers built systems that run completely counter to human memory and patience. They demanded that people memorize dozens of unique strings that resemble nuclear launch codes. When users inevitably failed and reused the same phrase, the industry blamed them for getting hacked. This is a fundamentally abusive relationship between software developers and the end user, and it is finally coming to an end.
The Human Cost Of The Memory Game
We need to talk about the immense cognitive load we all carry just to exist in modern society. The average professional in 2026 now manages over one hundred and fifty distinct online accounts. Logging into a portal to pay a utility bill, check a medical result, or access a bank account often feels like a high stakes memory test. We have normalized a daily routine of extreme frustration and anxiety.
The dreaded account recovery loop is a uniquely modern form of psychological torture. You type your phrase, you get an error message, and you request a reset link. You wait for an email, click the link, and create a new phrase only to be told it cannot match your previous three entries. This friction actively discourages people from engaging with essential digital services and creates a massive barrier to digital equity. Older adults and marginalized communities often simply give up, locking themselves out of the modern economy because the gateway is too aggressively hostile.
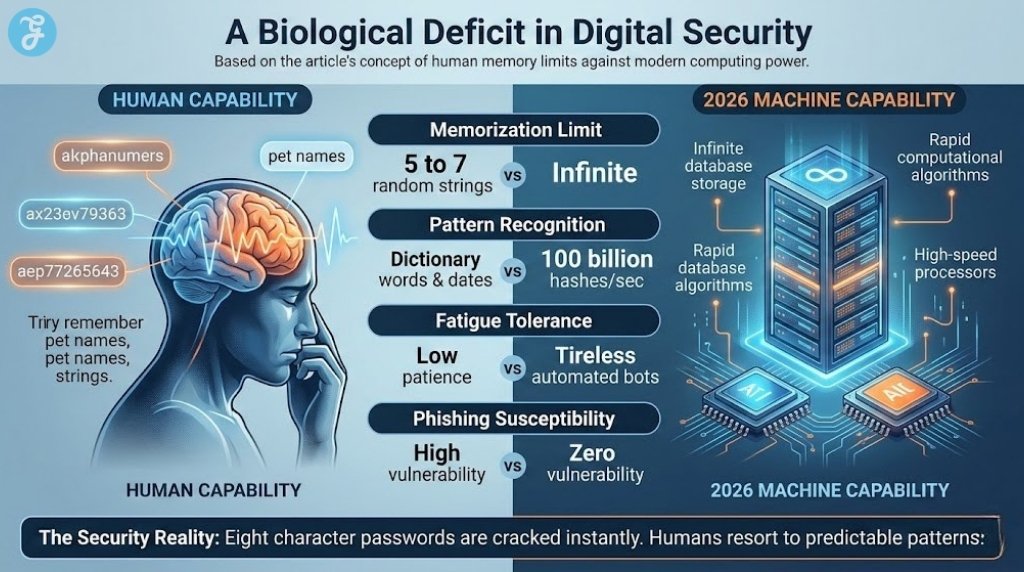
To understand the absurdity of our current posture, we must compare the biological limits of human memory against the mathematical reality of modern computing power.
The Biological Deficit In Digital Security
| Authentication Metric | Human Capability | 2026 Machine Capability | The Security Reality |
| Memorization Limit | 5 to 7 random strings reliably | Infinite database storage | Humans will always resort to predictable patterns |
| Pattern Recognition | Relies on dictionary words and dates | Processes 100 billion hashes per second | Eight character passwords are cracked instantly |
| Fatigue Tolerance | Low patience for constant resets | Tireless automated brute force bots | Users actively bypass security protocols to save time |
| Phishing Susceptibility | High vulnerability to visual deception | Zero vulnerability to fake websites | Humans will hand over keys if the website looks real |
Humans are creatures of habit. When forced to change a password, the vast majority of people simply take their old password and add a number one or an exclamation point to the end. Hackers know this. Their automated scripts are programmed to immediately test these exact predictable variations. We are playing a game of chess against a supercomputer, and we are voluntarily giving up our queen on the first move.
The Economic Cost Of Inaction
Follow the money and you will find that the push for new authentication is a desperate financial imperative. Corporate IT departments are bleeding capital into the void of the reset loop. In 2026 the average cost of a single password reset for an enterprise company has hit seventy dollars. This accounts for the lost productivity of the employee, the time spent by the helpdesk technician, and the administrative overhead of routing the support ticket. When you consider that over half of all IT support tickets globally are related to locked accounts, the sheer waste of human capital becomes staggering.
We must also look at the devastating financial toll of corporate ransomware. This booming criminal industry thrives almost entirely on compromised credentials. When a hacker buys a stolen login on a dark web forum for ten dollars, they bypass millions of dollars worth of firewall protections. Businesses are bleeding massive amounts of capital while trying to defend an indefensible perimeter. The cost is not just measured in ransom payouts to cybercriminal syndicates. We also have to account for the lost revenue when thousands of employees are locked out of their workstations for days at a time.
The financial bleeding will only stop when we remove the weapon from the battlefield entirely. If there is no password to steal, the entire economic model of the credential stuffing industry collapses overnight.
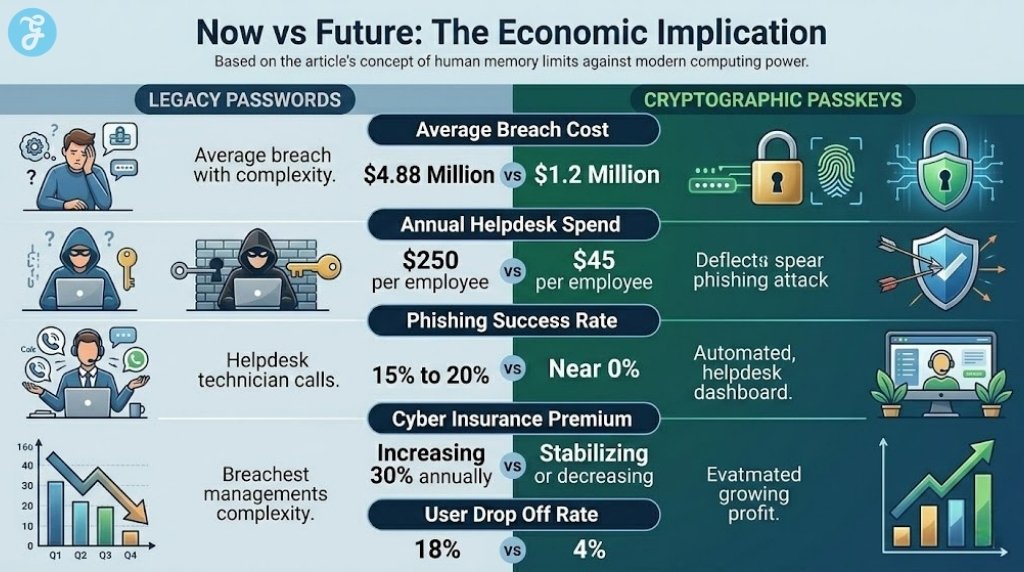
Now vs Future: The Cost Of Inaction
| Business Metric | Staying With Legacy Passwords | Upgrading To Cryptographic Passkeys | The 2026 Financial Impact |
| Average Breach Cost | $4.88 Million per incident | $1.2 Million per incident | Massive reduction in targeted credential risk |
| Annual Helpdesk Spend | $250 per employee | $45 per employee | Huge savings on reset related administrative overhead |
| Phishing Success Rate | 15% to 20% | Near 0% | Cryptographic keys physically cannot be phished |
| Cyber Insurance Premium | Increasing 30% annually | Stabilizing or decreasing | Underwriters now heavily penalize legacy security |
| User Drop Off Rate | 18% abandon cart at login | 4% abandon cart at login | Significant boost to e-commerce conversion revenue |
Cyber insurance underwriters finally recognize the inherent risk of relying on human memory. Many major insurers now refuse to cover companies that lack modern hardware token policies or strict biometric integration. This financial pressure is finally forcing boardrooms to treat authentication as a critical business continuity issue rather than an IT afterthought.
The transition requires an initial capital expenditure to upgrade legacy systems and educate the workforce. However the return on investment is absolutely undeniable when you factor in the reduction of helpdesk tickets and the massive drop in successful phishing campaigns. Refusing to upgrade your authentication framework in 2026 is an act of blatant fiscal negligence. The companies that cling to alphanumeric strings will simply be priced out of the cyber insurance market within the next two years.
The Geopolitical Stakes: State Hackers At Your Digital Doorstep
We tend to view account security as a personal annoyance or a corporate liability, but it has rapidly escalated into a matter of urgent national defense. Geopolitics is now the dominant driver of cybersecurity risk. State sponsored threat actors from rival nations are actively harvesting credentials on an industrial scale. They are not looking to steal your credit card numbers or your social media photos. They are looking for a quiet foothold into critical infrastructure, defense contractors, and global supply chains.
A compromised water treatment facility or a disrupted energy grid often traces back to a single negligent employee using a weak login. Nation state hackers exploit the fact that a defense contractor might share the exact same weak password with a local food delivery service. When that poorly secured delivery service is breached, the spies extract the data and use those exact credentials to infiltrate the defense network.
This is exactly why moving to a cryptographic standard is a patriotic imperative. We cannot protect our power grids and our financial institutions if the people running them rely on a pet name from childhood. Upgrading our national authentication standard is just as important as reinforcing our physical borders. Citizens who practice poor digital hygiene inadvertently provide perfect cover for foreign intelligence operations.
Global Benchmark: Authentication Readiness
| Global Region | Primary Authentication Stance | Passkey Adoption Rate | Geopolitical Driver |
| European Union | Strict Regulatory Mandates | 55% | Deep focus on digital sovereignty and strict data privacy laws |
| North America | Enterprise led Zero Trust | 39% | High volume of state backed corporate espionage |
| Asia Pacific | Rapid Biometric Integration | 62% | Government driven mobile first digital identity initiatives |
| Latin America | Transitioning from SMS codes | 13% | High vulnerability to cyber enabled banking fraud |
The variation in regional confidence is very telling. While European and Asian markets are aggressively legislating the death of the password, North America relies on a fragmented corporate approach. This leaves massive gaps in the armor of Western digital infrastructure. When a regional hospital network is entirely dependent on the password habits of an exhausted third shift nurse, the entire community is at risk of a total operational shutdown.
The Counter-Punch: Why Centralized Vaults Fail
There is a very loud contingent of security experts who argue that we do not need to kill the password entirely. They claim that centralized digital password managers are the perfect solution to our memory problem. You only need to remember one extremely complex master phrase to unlock a vault that holds hundreds of generated alphanumeric strings. They argue this fixes the reuse problem without requiring a massive overhaul of internet architecture.
This approach certainly improves basic hygiene by preventing password reuse, but it leaves a massive and terrifying vulnerability glaring right at us. A digital vault is like putting all your most valuable possessions in a titanium safe and then leaving the key under the welcome mat. The underlying architecture still relies on a shared secret being transmitted across the internet.
If a bad actor captures your single master phrase through a sophisticated spear phishing email or a keystroke logger, your entire digital life is instantly compromised. The hacker gets the keys to your bank, your email, your medical records, and your corporate network all at once. Password managers consolidate risk rather than eliminating it. They are a temporary bandage applied to a fundamental architectural flaw. Passkeys change this dynamic by eliminating the shared secret entirely. There is nothing for the user to type and therefore nothing for the hacker to steal.
The Moral And Practical Solution: Embracing The New Standard
The practical solution is already deployed in the devices we carry in our pockets every single day. The technology industry has finally aligned behind a universal standard called WebAuthn and FIDO2. This is the architecture that powers passkeys and biometric enclaves.
The transition moves us from “something you know” to “something you have” and “something you are.” Traditional passwords are knowledge based, which makes them incredibly vulnerable to social engineering and brute force attacks. Passkeys are possession based and stored securely in a dedicated hardware enclave on your phone or laptop.
When you log into a website using a passkey, your device generates a unique cryptographic puzzle. You unlock your device using a biometric scan like a fingerprint or facial recognition. Your device then solves the puzzle and confirms your identity to the server without ever transmitting any secret data. Even if the server is completely breached by hackers, the public keys stored there are completely useless without the physical device sitting in your hand. This effectively closes the door on credential stuffing and phishing forever. You cannot be tricked into typing your password into a fake banking website because there is no password to type.
We must demand that our banks, our healthcare providers, and our employers adopt this standard immediately. Every day we delay is another day we expose vulnerable people to financial ruin and identity theft. Security should not require a photographic memory. It should be built seamlessly into the tools we use to navigate the modern world.
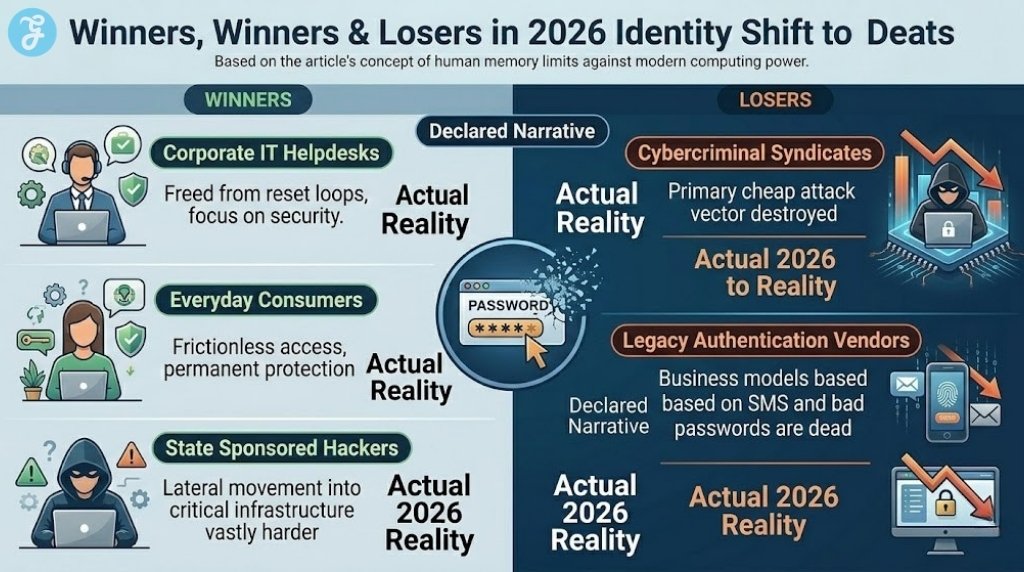
Winners vs Losers In The Identity Shift
| Market Entity | Declared Narrative | Actual 2026 Reality |
| Corporate IT Helpdesks | Losing control over user credentials | Strategic Winners (Freed from reset loops to focus on actual security) |
| Cybercriminal Syndicates | Adapting to new security measures | Massive Losers (Their primary cheap attack vector is completely destroyed) |
| Everyday Consumers | Confused by new login methods | Ultimate Winners (Frictionless access and permanent protection from breaches) |
| Legacy Authentication Vendors | Pivoting to offer new hybrid solutions | Financial Losers (Business models based on SMS texts and bad passwords are dead) |
| State Sponsored Hackers | Unbothered by consumer tech shifts | Strategic Losers (Lateral movement into critical infrastructure becomes vastly harder) |
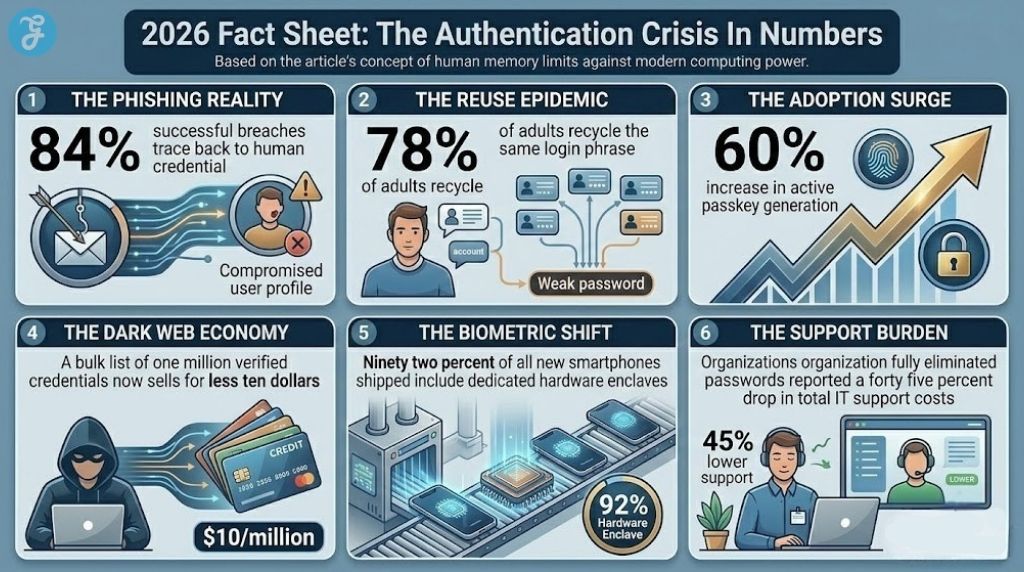
2026 Fact Sheet: The Authentication Crisis In Numbers
We must ground our perspective in the hard market data of the current year. The statistics prove that the old ways are completely dead and the new standard is rapidly taking over.
-
The Phishing Reality: Over eighty four percent of successful corporate breaches in early 2026 trace back to a compromised human credential rather than a software vulnerability.
-
The Reuse Epidemic: Despite two decades of warnings, seventy eight percent of adults still recycle the exact same login phrase across their banking and social media accounts.
-
The Adoption Surge: Major consumer tech platforms report a sixty percent increase in active passkey generation compared to the previous calendar year.
-
The Dark Web Economy: A bulk list of one million verified credentials now sells for less than ten dollars, making high volume attacks incredibly cheap for amateur criminals.
-
The Biometric Shift: Ninety two percent of all new smartphones shipped in 2026 include dedicated hardware enclaves designed specifically to store cryptographic passkeys safely.
-
The Support Burden: Organizations that fully eliminated passwords reported a forty five percent drop in total IT support costs within their first fiscal quarter.
End of Traditional Passwords And The Future Of Identity
In the next twelve to eighteen months we will witness the “Passkey Default” era solidify across the entire internet. Major platforms and financial institutions will simply stop asking you to create a password when you sign up for a new service. They will prompt you to save a passkey to your device and move on. The alphanumeric string will be relegated to a legacy fallback option much like the rotary phone or the physical floppy disk.
The death of the traditional login will ultimately divide the digital world into two distinct camps. There will be those who have secured their identity with hardware bound cryptography and those who remain highly vulnerable to the next massive data leak. The era of the special character requirement is dead, and we are all much safer for it.
We can no longer allow lazy corporate infrastructure to dictate our personal security. If the technology already exists in your pocket right now to make your digital life completely unhackable, why are you still trusting your entire financial and personal identity to a dog’s name and an exclamation point?