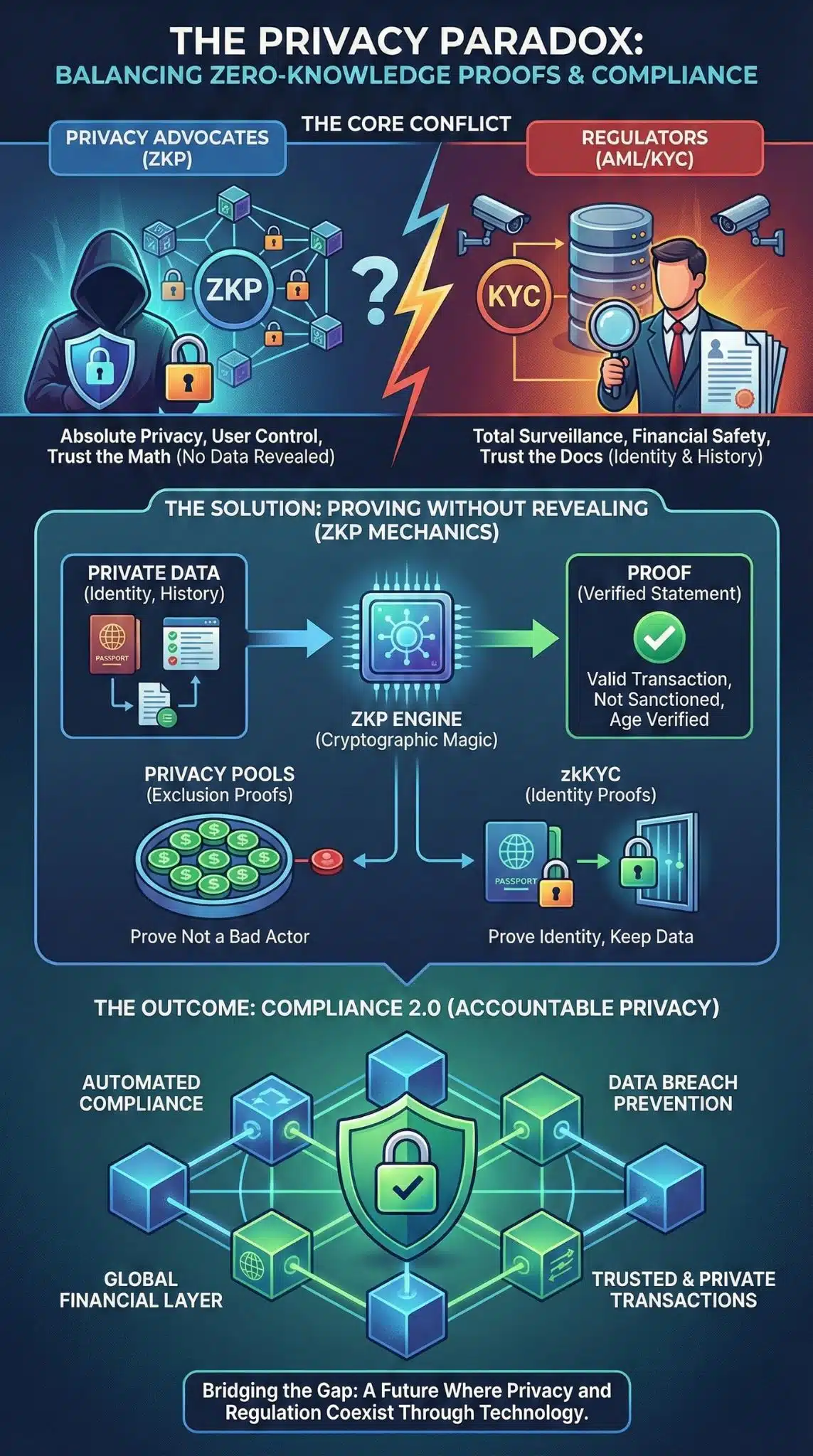
In the world of digital finance, two unstoppable forces are colliding. On one side, we have the crypto ethos of absolute privacy and self-sovereignty. On the other, the unyielding wall of global financial surveillance designed to stop money laundering and terror financing. For years, this seemed like a zero-sum game: you either had privacy, or you had compliance. You couldn’t have both.
Enter Zero-Knowledge Proofs (ZKPs). This cryptographic magic allows you to prove something is true without revealing the data that makes it true. Imagine walking into a bar and proving you are over 21 without handing over your ID card that shows your name, address, and exact birth date. In the financial world, this means proving your funds are clean without showing your entire transaction history to the world.
However, regulators are skeptical. The 2022 sanctions against Tornado Cash sent a chill through the industry, signaling that “code is speech” might not be a sufficient defense against Anti-Money Laundering (AML) laws. The tension of Zero-Knowledge Proofs vs. Regulatory Compliance is now the most critical battleground in crypto. It asks a fundamental question: Can we build a financial system that protects user privacy while satisfying the regulator’s need to catch bad actors?
The Core Conflict: Absolute Privacy vs. Total Surveillance
The financial world operates on a “trust but verify” model, but in traditional banking, verification requires total exposure. When you open a bank account, the bank knows who you are, where you live, and where your money comes from. Blockchain was supposed to change this by making the ledger public but the identities private. However, transparent ledgers like Bitcoin turned out to be the ultimate surveillance tool—chain analysis firms can now link almost any wallet to a real-world identity.
The Right to Financial Privacy
Privacy advocates argue that financial data is as sensitive as medical records. In an era of surveillance capitalism, users have a legitimate right to shield their spending habits from corporations and hackers. ZKPs offer “technological privacy,” ensuring that valid transactions can occur without exposing the sender, receiver, or amount. This isn’t just about hiding crime; it’s about preventing competitors from seeing your supply chain payments or protecting individuals in authoritarian regimes.
The Regulator’s Mandate (AML & KYC)
Regulators view privacy tools as “mixers” that break the chain of custody. If a regulator cannot trace the flow of funds from A to B, they assume the worst: money laundering, tax evasion, or sanctions evasion. The Know Your Customer (KYC) and Anti-Money Laundering (AML) frameworks are built on identity. They demand to know who is behind the transaction. The conflict of Zero-Knowledge Proofs vs. Regulatory Compliance stems from this mismatch: regulators want identity-based compliance, while ZKPs offer behavior-based validation.
The Privacy-Compliance Standoff
| Feature | Privacy Advocates (ZKP) | Regulators (AML/KYC) |
| Primary Goal | Data minimization and anonymity. | Financial transparency and accountability. |
| Verification Method | Mathematical proofs (Cryptographic). | Identity checks and document collection. |
| Data Visibility | “Trust the math, not the person.” | “Trust the documents, verify the person.” |
| Risk Perspective | Transparent ledgers expose users to hackers. | Opaque ledgers hide criminals and terrorists. |
How Zero-Knowledge Proofs Change the Game
To understand the solution, we have to look under the hood. Zero-Knowledge Proofs allow a “Prover” to convince a “Verifier” that a statement is true without revealing the underlying information.
Proving Without Revealing
In a standard crypto transaction, you prove you have the funds by broadcasting the transaction, which reveals your balance and history. With ZKP systems like zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Argument of Knowledge), you generate a proof off-chain. You submit this proof to the blockchain. The blockchain verifies the proof is mathematically sound and processes the transaction. The ledger records that a valid transaction happened, but it contains zero information about who sent it or how much was sent.
Selective Disclosure and Programmable Privacy
This is where it gets interesting for compliance. ZKPs can be programmed to reveal some things but not others. This is called “Selective Disclosure.” For example, a user could generate a ZKP that proves:
- They are not on an OFAC sanctions list.
- They are a resident of a specific jurisdiction (e.g., the EU).
- Their transaction amount is below the reporting threshold ($10,000).
They prove all three facts to the compliant smart contract without ever revealing their name or passport number. This capability is the strongest argument for Zero-Knowledge Proofs vs. Regulatory Compliance—it technically satisfies the requirement of preventing illicit finance without destroying privacy.
Types of Zero-Knowledge Proofs
| Type | Description | Pros | Cons |
| zk-SNARKs | The most common form (used by Zcash, Tornado Cash). | Small proof size, very fast verification. | Requires a “trusted setup” phase; quantum vulnerable. |
| zk-STARKs | A newer, more scalable evolution. | No trusted setup required; quantum resistant. | Larger proof sizes allow for slower verification. |
| Bulletproofs | Designed for confidential transactions (Monero). | No trusted setup; short proofs. | Verification is more computationally intensive. |
The Regulatory Landscape: From Bans to Frameworks
Regulation is moving fast. The “Wild West” days are ending, and governments are putting specific frameworks in place that directly impact privacy technologies.
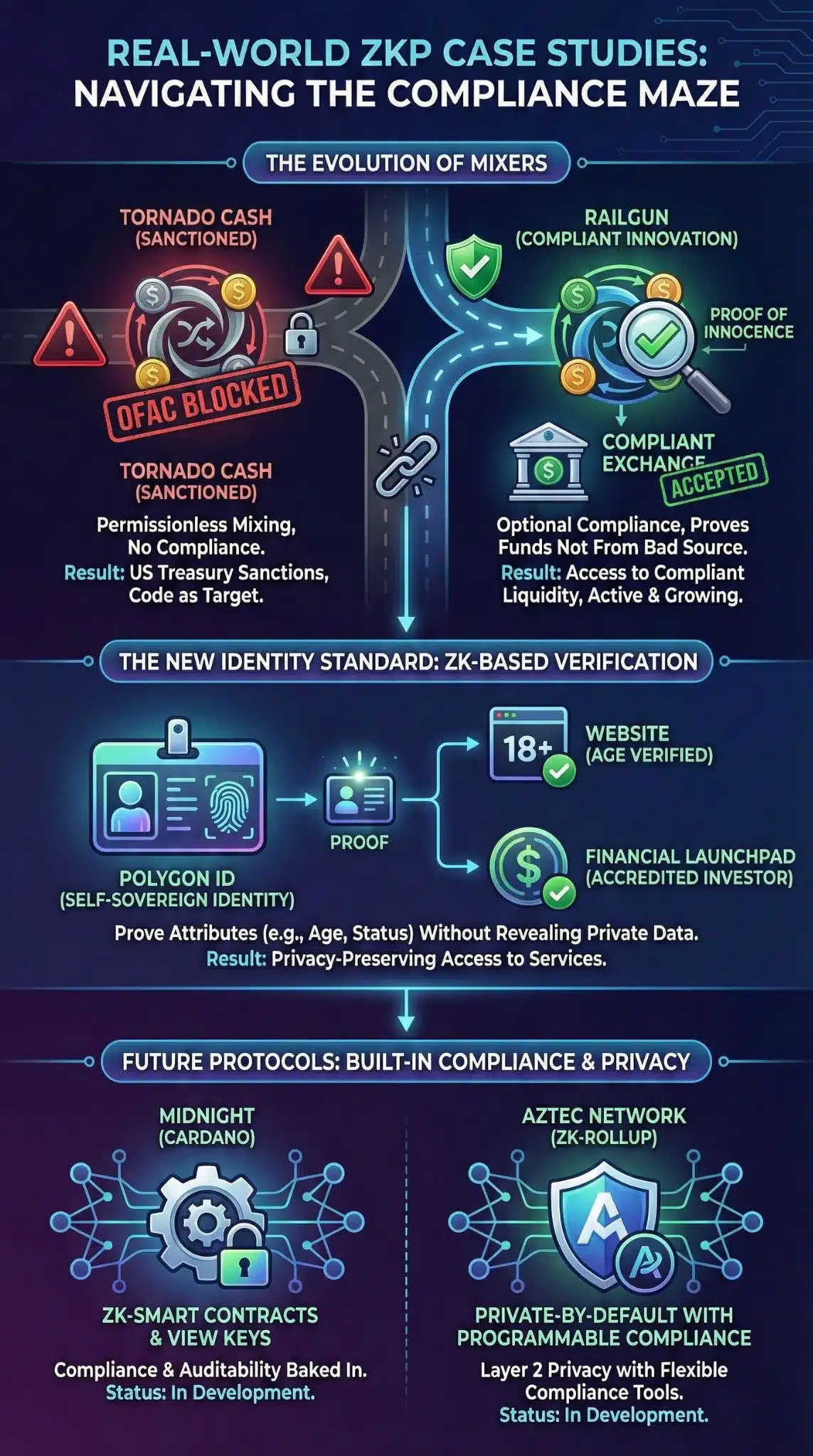
The Shadow of Tornado Cash
In August 2022, the US Office of Foreign Assets Control (OFAC) sanctioned the Tornado Cash smart contracts. This was historic because they sanctioned code, not just a person. Tornado Cash used ZKPs to mix funds, breaking the link between sender and receiver. Regulators argued that because North Korean hackers used it, the tool itself was non-compliant. This set a dangerous precedent: if a ZKP tool cannot prevent bad actors from using it, the tool itself is illegal. This created a massive chilling effect on developers building privacy infrastructure.
EU’s MiCA and the Travel Rule
Across the Atlantic, the European Union’s Markets in Crypto-Assets (MiCA) regulation is setting the global standard. MiCA imposes strict rules on Crypto Asset Service Providers (CASPs). Furthermore, the “Travel Rule” requires exchanges to pass customer information (name, address) alongside transactions. For ZKP protocols, this is a hurdle. If a protocol is decentralized, who collects this data? Who sends it? The EU has signaled they are open to “privacy-enhancing technologies,” but only if they don’t impede AML monitoring.
Key Regulations Impacting ZKPs
| Regulation | Jurisdiction | Impact on ZKPs |
| OFAC Sanctions | USA | Establishing that immutable smart contracts can be sanctioned if used for laundering. |
| MiCA (Markets in Crypto Assets) | EU | strict rules for stablecoins and CASPs; pushes for identifiable transactions. |
| FATF Travel Rule | Global | Requires “originator” and “beneficiary” data to travel with funds, challenging anonymous ZKP transfers. |
| GDPR | EU | Ironically supports ZKPs because they minimize data collection (Right to be Forgotten). |
Bridging the Gap: Compliance-Friendly Privacy Solutions
The industry is not standing still. Developers are actively building “Compliance 2.0” tools that utilize Zero-Knowledge Proofs vs. Regulatory Compliance tensions to create a hybrid model.
Privacy Pools
Proposed by heavyweights like Vitalik Buterin, “Privacy Pools” are the direct answer to the Tornado Cash dilemma. In a Privacy Pool, honest users can cryptographically prove that their funds did not come from a known bad source (like a hack or a sanctioned wallet).
- How it works: Users generate a ZKP that says, “I am part of this large group of deposits, BUT I am definitely NOT part of that smaller group of stolen funds.”
- Result: Honest users get privacy relative to the general public, but they can prove their innocence to regulators or exchanges without revealing their exact history.
Decentralized Identity (DID) and zkKYC
Instead of uploading your passport photo to every crypto exchange (creating a massive “honeypot” for hackers), you verify your identity once with a trusted provider. That provider issues a verifiable credential (VC) to your wallet.
When you want to use a compliant DeFi protocol, you present a ZKP that proves you hold a valid “Non-Sanctioned US Citizen” credential. The DeFi protocol verifies the math and lets you in. They never see your name, and they don’t store your data. This is zkKYC (Zero-Knowledge Know Your Customer).
Emerging Compliance Solutions
| Solution | Mechanism | Benefit for User | Benefit for Regulator |
| Privacy Pools | Exclusion proofs (proving you aren’t bad). | Privacy from public; access to compliant liquidity. | Isolates bad actors; allows innocent funds to move. |
| zkKYC / zkID | Identity proofs (proving you are verified). | No repeated data uploads; protection from identity theft. | Assurance that the user has passed KYC checks. |
| View Keys | Optional transparency. | User can generate a key to show only an auditor their history. | Auditors can verify tax/compliance without public leaks. |
Real-World Case Studies
Theory is fine, but how is this playing out in the market right now?
Polygon ID and the New Identity Standard
Polygon has launched Polygon ID, a self-sovereign identity solution based on ZKPs. It allows users to create a digital identity wallet. A practical use case is age verification. A user can prove to a website they are over 18 using a ZKP. The website receives a “True/False” signal. This is now being adapted for financial compliance, where a user proves “Accredited Investor Status” to join a launchpad without uploading bank statements.
The Evolution of Mixers
While Tornado Cash is sanctioned, new protocols are rising. Railgun is a privacy system for DeFi that uses zk-SNARKs. It recently integrated a “Proof of Innocence” feature. This feature allows users to mathematically prove their funds are not from the OFAC blocked list. By doing so, they maintain their privacy while ensuring that compliant exchanges (like Coinbase or Binance) might accept their deposits, solving the liquidity fragmentation issue.
Protocol Comparison
| Protocol | Privacy Tech | Compliance Approach | Status |
| Tornado Cash | zk-SNARKs | None (Permissionless). | Sanctioned by US Treasury. |
| Railgun | zk-SNARKs | Proof of Innocence (Optional). | Active, gaining traction. |
| Midnight (Cardano) | ZK-Smart Contracts | Built-in compliance & view keys. | In Development. |
| Aztec Network | ZK-Rollup | Private-by-default with programmable compliance. | In Development. |
Final Thoughts
The narrative of Zero-Knowledge Proofs vs. Regulatory Compliance is shifting from conflict to collaboration. We are moving away from the binary choice of “anarchy vs. surveillance” toward a nuanced middle ground.
The technology for “accountable privacy” exists. Privacy Pools and zkKYC prove that we can strip the financial system of its surveillance nature without opening the doors to money launderers. The hurdle now is not technological—it is political. Regulators must be willing to accept mathematical proofs as a substitute for invasive data collection.
If they do, ZKPs could save the internet. They offer a future where data breaches are impossible because companies don’t hold our data, and where compliance is instant, automated, and invisible. If they don’t, the crypto industry may bifurcate into a “compliant, public” chain and a “dark, private” chain, destroying the dream of a unified global financial layer.
For now, the smartest players are those building the bridges: the tools that allow users to remain private, yet provably innocent.