Popular Articles
Natural Sunscreen Vs Conventional: Which One Should You Get?
I care about greener swaps, but I draw a very thick line at gambling with sun protection. Reusable bottles, low-waste...
TikTok For B2B Brands: What’s Actually Converting In 2026
We are almost half done with 2026 and TikTok for B2B Brands is no longer a joke. The joke is...
Claude vs ChatGPT vs Gemini: Which LLM Dominates Enterprise AI Workflow Automation?
Claude vs ChatGPT vs Gemini is no longer a simple chatbot comparison. After reviewing all three through real enterprise workflow...
Reusable Coffee Cups: 8 Tested for Insulation, Leaks, and Ease of Use!
Reusable Coffee Cups sound like a small life upgrade until one leaks inside your bag and turns your laptop sleeve...
Building AI Research Agent: Tools, Architecture, And Real Results!
Building an AI research agent sounds exciting until you actually try to make one useful. Then the fantasy disappears very...
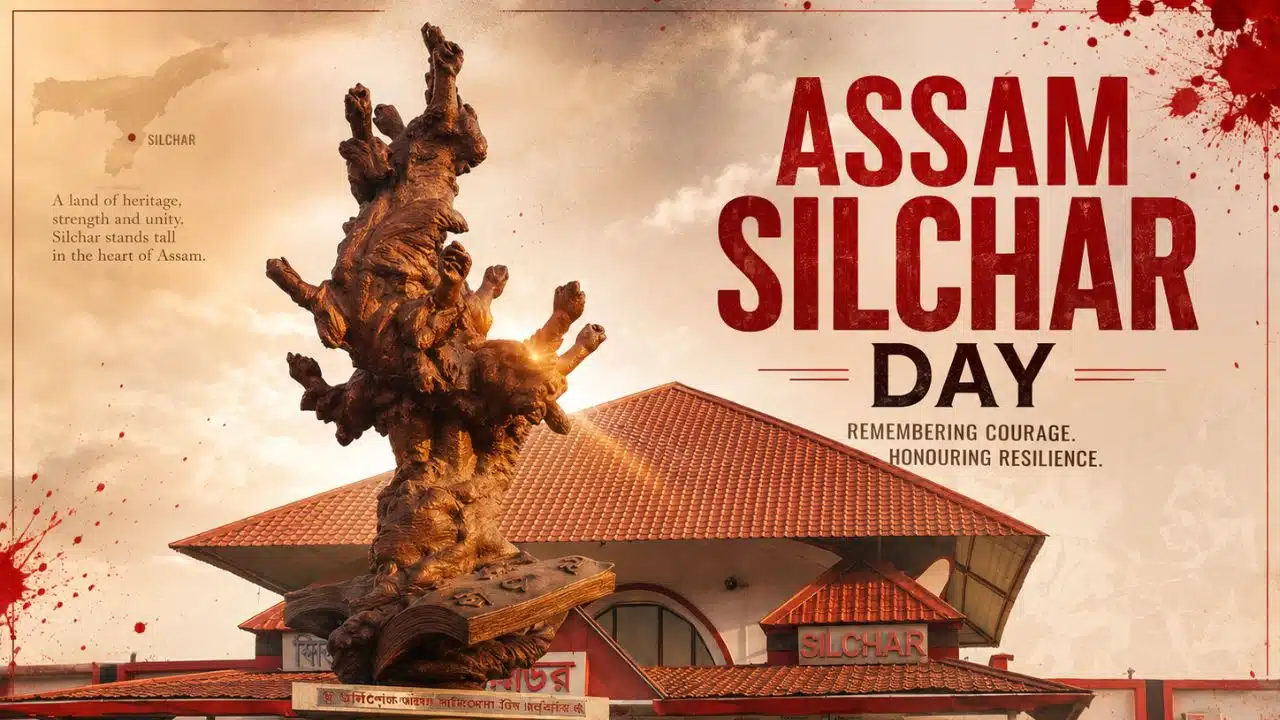
Tears in the Morning Light: The Blood-Stained Tracks of Silchar’s May 19
The crackling dawn of May 19, 1961, promised a new beginning for the Barak Valley, yet it would end in...
Latest Articles
How Page Speed Affects Your SEO Rankings
Ever wonder why a website feels fast on a desktop but struggles to generate leads? Real-world visitors rarely browse on...
Natural Sunscreen Vs Conventional: Which One Should You Get?
I care about greener swaps, but I draw a very thick line at gambling with sun protection. Reusable bottles, low-waste...
How To Open A Bank Account As A Non-US Resident
Trying to open a US bank account as a non-resident can easily feel overwhelming, as institutions frequently demand an endless...
TikTok For B2B Brands: What’s Actually Converting In 2026
We are almost half done with 2026 and TikTok for B2B Brands is no longer a joke. The joke is...
Claude vs ChatGPT vs Gemini: Which LLM Dominates Enterprise AI Workflow Automation?
Claude vs ChatGPT vs Gemini is no longer a simple chatbot comparison. After reviewing all three through real enterprise workflow...
Internal Linking Strategy That Boosts Rankings
Publishing a high-quality article only to see it underperform is a common frustration. Often, the missing piece is a robust...