Ever feel like your house is quietly listening to your conversations? You probably rely on your smart speaker to check the weather, and your fitness tracker to count your steps. These gadgets make our daily routines so much easier. But they also quietly gather an astonishing amount of information about us every single day. Many of us feel a bit uneasy about who actually sees our personal data and where it goes. It turns out, smart devices collect a lot of details even when we are fast asleep.
Understanding AI data privacy in smart devices is a necessary step for anyone living in a modern home. Tech companies use artificial intelligence to guess what you want before you even type it in. Sometimes, this information gets sold to third parties without you ever realizing it.
I am going to walk you through exactly what your smart devices collect and why it matters. We will look at how AI systems gather your information and the privacy risks involved.
What is AI Data Privacy?
Now that we have set the stage, let’s talk about what AI privacy actually means for your daily life. AI privacy is the practice of protecting your personal information from being collected or misused by artificial intelligence systems.
These systems constantly gather details about you, like your voice patterns and your daily shopping habits. Taking control of AI privacy means you get to decide how companies use that information to build your digital footprint.
According to a 2026 survey by Pew Research Center, 70% of adults in the US have little to no trust in companies to use artificial intelligence responsibly.
That lack of trust makes perfect sense when you realize how much background monitoring happens in our homes. In 2026, RubyHome reported that over 77 million US homes actively use smart home devices.
Your smart speaker is always waiting for a wake word, and your phone constantly maps your face. These biometrics create incredibly detailed profiles about your personal life.
Companies use this personal information to train their AI tools, but you deserve to know what data collection actually takes place. Understanding AI privacy gives you the power to enjoy your Internet of Things devices safely.
How Smart Devices Collect Data
Your smart devices pull in mountains of information about you every single day, often without you even noticing. They use microphones, cameras, and location services to map out your preferences and daily routines.
Predictive AI and data gathering
Predictive AI systems act like digital fortune tellers for tech companies. They soak up massive amounts of data to guess what you might do or buy next.
For example, the 2026 Amazon Echo Show 21 uses a feature called Alexa+ to act as a proactive digital family coordinator. Instead of just answering questions, it anticipates your routines and manages your schedule based on past habits.
To make these smart predictions, companies need to gather specific types of data:
- Location history: Tracking where you go helps them suggest nearby stores or restaurants.
- Voice recordings: Analyzing your tone and requests refines their natural language processing.
- Shopping habits: Monitoring your past purchases helps them predict your future needs.
- Daily routines: Logging when you turn off the lights tells them your sleep schedule.
The more data these AI tools collect, the smarter they become. Your Internet of Things devices feed this surveillance data back to corporate servers silently while you go about your day.
Tracking user behavior and preferences
Your smart devices track your behavior to build a complete profile of your interests. They monitor what you search for online and which apps you open most frequently.
Tech companies value your preferences because your data drives massive profits. In fact, Mordor Intelligence projects the global data broker market will reach over $315 billion in 2026.
Data brokers buy and sell your information to advertisers, who then target you with highly personalized ads.
| Data Type Tracked | How It Is Used | The Privacy Impact |
|---|---|---|
| Search History | To predict future purchases | Builds a profile of your interests and health concerns |
| Voice Commands | To improve AI tools | Records intimate conversations in your home |
| App Usage | To identify your daily routines | Reveals your schedule and free time habits |
This behavioral tracking creates a map of your life that gets sold to third parties. Your consent often gets buried in long terms and conditions that nobody has time to read.
Data collected through connected ecosystems
Smart devices rarely work entirely on their own anymore. Your smartphone talks to your smartwatch, which links to your home security system.
This constant chatter creates a connected ecosystem that shares your digital footprint across multiple platforms. Fitness trackers monitor your heart rate, while connected cars log your daily driving routes.
The problem is that owning more devices multiplies the amount of personal information you give away. An action as simple as controlling your lights with a voice command feeds data points into a larger surveillance network.
Risks Associated with AI Data Privacy in Smart Devices
As AI systems gather more of your data, the risks to your privacy increase significantly. Let’s look at exactly what happens when your personal information sits in a corporate database.
Collection of sensitive data
Your smart home ecosystem collects far more sensitive data than just your favorite music playlists. These devices gather your financial details, exact location, and even biometric information like fingerprints and facial scans.
A major privacy concern is how easily this sensitive information can be misused or exposed. The US Government Accountability Office noted in 2026 that AI makes it incredibly easy to cross-reference multiple datasets, which can reveal private details you thought were anonymous.
Hackers actively target this information because it is incredibly valuable.
- Biometrics: Fingerprints and facial recognition patterns cannot be changed if they are stolen.
- Health metrics: Sleep data and heart rates reveal intimate details about your physical condition.
- Location data: GPS tracking shows exactly where you live, work, and drop off your kids.
- Voice patterns: Audio clips can be used by scammers to clone your voice using AI tools.
Companies claim they need your digital footprint to improve their services, but the security risks are real.
Data collection without explicit consent
Many companies collect your information without ever asking for clear, upfront permission. They hide their data collection policies deep within confusing terms of service documents.
You tap “agree” to use a new app, and the company immediately starts tracking your habits and location. This lack of transparency means you never actually consented to share your personal information in a meaningful way.
Internet of Things devices transmit your data to distant servers, where it gets stored and analyzed. This sneaky practice strips away your control and makes your information a bigger target for cybersecurity threats.
Unchecked surveillance and bias
Constant monitoring from smart devices creates a foundation for unchecked surveillance in your own home. Your fitness tracker logs your health metrics, and your smart speaker captures background conversations.
When AI systems learn from collected data without proper oversight, they often develop harmful biases that lead to unfair decisions.
Algorithms trained on biased information can unfairly restrict access to credit, housing, or employment. For instance, facial recognition systems historically show higher error rates for people with darker skin tones.
These biases persist because developers do not always actively audit their AI systems for fairness. This means your smart technology might not work equally well for everyone in your family.
Data leakage and exfiltration
Keeping massive databases of personal information creates a goldmine for cybercriminals. Data exfiltration happens when hackers break into these servers, steal your information, and sell it on the dark web.
This is not a rare occurrence. According to IBM’s 2025 breach report, one in five organizations experienced a data breach due to “shadow AI” use, costing them an average of $670,000 per incident. These breaches often happen when employees paste sensitive customer data into public AI chatbots.
To keep your data safe, it helps to know how these leaks typically happen:
- Shadow AI usage: Employees pasting private data into unauthorized public chatbots.
- Unpatched software: Hackers are exploiting outdated firmware on smart home devices.
- Weak passwords: Using the same simple password across all your connected ecosystems.
- Excessive permissions: Granting an app access to your camera when it only needs your Wi-Fi.
Regulations Governing AI and Privacy
Governments are finally stepping up to protect your personal information from AI surveillance. These new laws force companies to change how they handle your data.
General Data Protection Regulation (GDPR)
The European Union launched the GDPR to give people real power over their own personal data. This strict law applies to any company handling data from EU residents, regardless of where the business is headquartered.
GDPR requires organizations to get clear, explicit consent before tracking your behavior or collecting biometrics. If a company violates these privacy rules, they face massive fines that can reach millions of dollars.
This regulation completely changed global data security standards, forcing tech companies to take user consent seriously.
EU Artificial Intelligence (AI) Act
The EU Artificial Intelligence Act is a major law designed specifically to control how companies use high-risk AI tools. It focuses heavily on protecting citizens from dangerous surveillance practices.
The rules set by the EU AI Act are very strict:
- Bans on facial scraping: Companies cannot indiscriminately scrape photos from the internet to build facial recognition databases.
- Transparency requirements: Businesses must tell users when an AI system makes an important decision about them.
- Risk assessments: Developers must test high-risk AI tools for safety before releasing them to the public.
- Heavy penalties: Rule-breakers can be fined up to 6% of their total global yearly sales.
These requirements push manufacturers worldwide to build privacy protections into their smart technology from the very beginning.
US Privacy Regulations
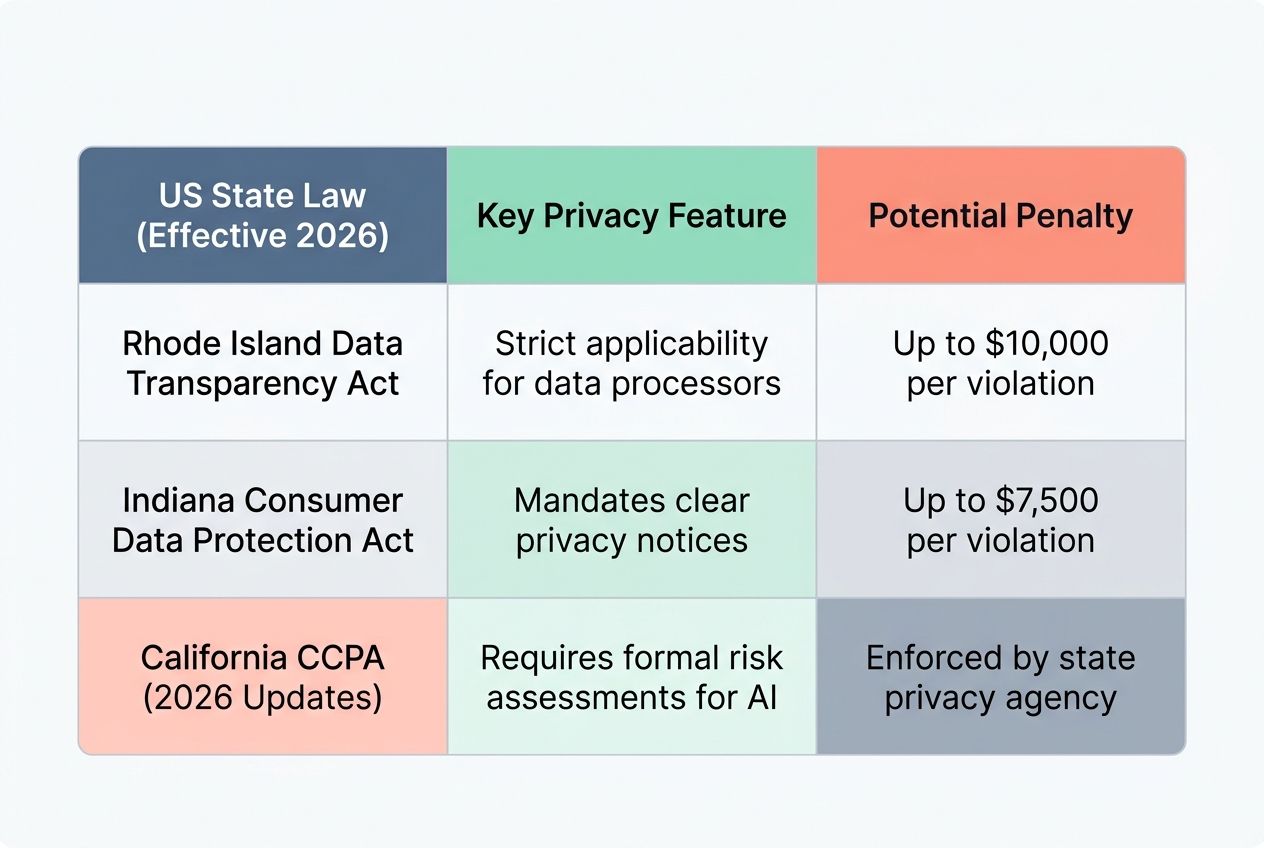
Unlike Europe, the United States relies on a patchwork of state laws rather than one federal privacy rule. However, 2026 brought a massive wave of new protections for US consumers.
On January 1, 2026, comprehensive data privacy laws officially took effect in Indiana, Kentucky, and Rhode Island. These states join places like California and Colorado in giving residents the right to access, correct, or delete their personal information.
| US State Law (Effective 2026) | Key Privacy Feature | Potential Penalty |
|---|---|---|
| Rhode Island Data Transparency Act | Strict applicability for data processors | Up to $10,000 per violation |
| Indiana Consumer Data Protection Act | Mandates clear privacy notices | Up to $7,500 per violation |
| California CCPA (2026 Updates) | Requires formal risk assessments for AI | Enforced by the state privacy agency |
On top of that, twelve US states now require businesses to recognize Global Privacy Control signals, which let you automatically opt out of data tracking across different websites.
China’s Interim Measures for Generative AI Services
China approaches AI regulation with a strong focus on government oversight and content security. Their Interim Measures for Generative AI Services require companies to register their AI algorithms with state authorities.
Tech companies in China must ensure their AI systems align strictly with local laws and values. This centralized approach means the government maintains close supervision over how user data is collected and processed.
While Western laws prioritize individual privacy rights, China’s framework focuses more heavily on maintaining social stability and national security.
Best Practices for AI Privacy
You do not have to wait for new laws to protect your personal information. There are plenty of proactive steps you can take right now to secure your digital footprint.
Conducting regular risk assessments
Think of a risk assessment as a routine health checkup for your smart home ecosystem. You should audit your connected devices every few months to spot vulnerabilities before hackers do.
Start by making a simple list of every smart device in your house, from your thermostat to your video doorbell. Then, check what kind of data each device is actively gathering.
To make this process easy, try following these assessment steps:
- Review network traffic: Log into your Wi-Fi router settings or use a network scanning app to see exactly which devices are connected.
- Check microphone settings: Verify which of your gadgets are currently allowed to listen for wake words.
- Audit location sharing: Turn off GPS tracking for apps that do not actually need it to function.
- Remove unused devices: Unplug and factory reset any smart gadgets you no longer use.
Taking a few minutes to evaluate your setup helps you catch surveillance risks early.
Limiting unnecessary data collection
Companies usually try to collect far more information than they actually need to run their services. You can easily push back against this practice by being stingy with your permissions.
Ask yourself if your new flashlight app really needs access to your contacts and your microphone. If the answer is no, simply deny those permissions in your phone’s settings.
By starving these apps of unnecessary data, you significantly shrink your digital footprint. This means companies have less of your personal information to sell to advertisers or lose in a data breach.
Seeking explicit user consent
Trustworthy smart devices should always ask for your permission before they start logging your habits. Companies need to tell you exactly what information they want and why they need it.
A truly secure smart home respects your boundaries and lets you say no to data collection without disabling basic features.
If an app hides its consent forms in a maze of fine print, that is a massive red flag. You should always look for clear opt-in buttons that give you direct control over your biometrics and voice recognition data. Strong cybersecurity starts with organizations that value transparency and put your privacy concerns first.
Implementing strong security measures
Once you decide what data you are willing to share, you need strong security measures to protect it. Encryption tools are your best friend here, as they scramble your sensitive data so hackers cannot read it.
You should always enable multi-factor authentication on your smart device accounts. This adds a second layer of security, like a text message code, so a stolen password is not enough to compromise your account.
Keeping your software updated is also incredibly important. Regular patches fix the vulnerabilities that bad actors rely on to access your home network.
How to Protect Your Privacy with Smart Devices
Guarding your personal information from AI surveillance does not require a computer science degree. Here are the most effective ways to take control of your smart technology today.
Monitoring device permissions
Every time you download a new app, it asks for permission to access your camera, location, or contacts. Tapping “allow” without thinking is like handing a stranger the keys to your digital life.
Take ten minutes this weekend to open your smartphone settings and review your app permissions. You might be surprised to find out how many random games have access to your microphone.
Here are the permissions you should restrict immediately:
- Precise Location: Change this to “Approximate” or “While Using the App” for weather and shopping apps.
- Microphone: Disable this for any app that does not involve voice or video calling.
- Camera: Turn this off for social media apps when you are not actively posting.
- Background App Refresh: Stop apps from secretly gathering data while you are not using them.
Using privacy-focused AI tools
You can still enjoy the benefits of AI without giving away all your secrets. Many developers are now creating privacy-focused tools that process information securely.
Switching to privacy-conscious platforms drastically reduces your security risks because they do not store or sell your data.
| Everyday Tool | Privacy-Focused Alternative | Why It Is Better |
|---|---|---|
| Standard Search Engines | DuckDuckGo or Brave Search | Blocks online trackers and does not save search history |
| Default Texting Apps | Signal | Uses end-to-end encryption for all your messages |
| Standard AI Note Takers | Plaud NotePin | Processes voice notes locally without selling data |
Using these tools protects your biometric data and location history from the massive data broker market.
Regularly updating software and firmware
Running outdated software is the easiest way to invite hackers into your smart home. Manufacturers constantly release new updates to fix bugs and patch security holes.
You need to update your smart speaker, security cameras, and Wi-Fi router as soon as those patches become available. These updates act like a fresh deadbolt on your digital front door.
The best strategy is to turn on automatic updates for all your Internet of Things devices. This simple habit keeps your personal information safe from data exfiltration while you sleep.
Disconnecting devices when not in use
Smart devices are designed to be always-on listeners. If you are not actively using a gadget, there is no reason for it to be constantly connected to the internet.
If you have a smart speaker in your guest room, simply unplug it until you actually have guests. Disconnecting devices cuts off the constant flow of surveillance data to corporate servers.
This action takes only a few seconds, costs absolutely nothing, and instantly improves your cybersecurity by removing a potential target for hackers.
The Future of AI and Privacy
The good news is that the tech industry is finally waking up to our privacy concerns. Let’s look at how future technology will protect your personal information.
Advancements in privacy-preserving AI
Smart technology is getting much better at protecting your identity while still being helpful. Engineers are building new AI models that process data directly on your device, rather than sending it to the cloud.
This approach, often called edge computing or federated learning, means your phone learns your habits locally. Your personal details never actually leave your house.
Some of the most exciting privacy advancements include:
- Federated learning: AI models train on your device, keeping your raw data completely local.
- Differential privacy: Systems add mathematical noise to data, making it impossible to identify you personally.
- Homomorphic encryption: Computers can process and analyze data while it remains fully scrambled and secure.
- Local NPU processing: New gadgets use built-in neural processing units to handle AI tasks without internet access.
These techniques ensure that your voice recognition data and biometrics stay private, even if a corporate server gets breached.
Balancing innovation with ethical considerations
Companies are finally realizing that they cannot push innovation at the expense of our privacy. The most successful tech brands are now building privacy into their products from day one, rather than treating it as an afterthought.
Balancing AI with ethics means asking tough questions about what data is truly necessary. A smart thermostat does not need to know your browsing history to keep your house warm.
By limiting unnecessary data collection and seeking explicit user consent, companies build genuine trust. The future of the Internet of Things belongs to devices that respect your digital footprint while still making your life easier.
Final Words
You now know exactly how your smart devices use AI systems to track your daily habits. It is clear that privacy risks are everywhere, from sensitive data exposure to silent, background surveillance. Thankfully, strict rules like the GDPR and the 2026 US state privacy laws are forcing companies to do better. But you hold the real power to protect your personal information right now.
Take a few minutes today to check your phone permissions and unplug the gadgets you do not use. Start using privacy-focused tools, and always keep your software updated.
FAQs
1. What kind of data do smart devices collect about me?
Your smart gadgets gather highly specific details about your daily routines, and with over 51% of US households using them in 2026, that is a massive amount of personal information. Things like your voice commands, location, and even the exact times you open your fridge or turn off your lights are constantly tracked.
2. What privacy risks are associated with AI in smart home devices?
The privacy risks associated with AI in smart home devices include continuous recording of user conversations without consent, mislabeling user preferences, and sharing user behavior patterns with third-party advertisers
3. Can my smart speaker listen to private talks?
Yes, devices like Amazon Alexa and Google Assistant can accidentally record your conversations due to false wake word triggers, which happen when they mistakenly hear a phrase similar to their name.
4. How do companies use the information from my connected appliances?
Companies analyze your daily habits to build detailed consumer profiles, which they then use to serve you highly specific targeted ads. For example, Samsung recently started a US pilot program displaying banner ads directly on the touchscreen of their smart refrigerators based on household usage data.
5. Is there any way I can limit what my digital helpers gather about me?
You can take back some control by opening your device settings, like going to the privacy menu in your Alexa app to stop saving voice recordings. You can also press the physical mute button on your speaker, or simply unplug the gadget during a private chat with your family.