The rapid evolution of Web3 has brought revolutionary changes to the internet, enabling decentralized applications (dApps), blockchain transactions, and digital asset ownership. While these innovations offer new opportunities, they also introduce new risks.
Security threats like phishing scams, wallet hacks, and malicious smart contracts are rampant in the Web3 ecosystem. Understanding the best practices for staying secure in Web3 is crucial to safeguarding your digital assets and personal information.
Unlike traditional Web2 platforms, where centralized entities manage security, Web3 users bear full responsibility for protecting their assets. Cybercriminals are continuously developing new attack methods, making it essential to stay informed and implement robust security measures.
This guide delves into seven best practices for staying secure in Web3, offering insights, real-world examples, and actionable strategies to help you navigate the decentralized web safely.
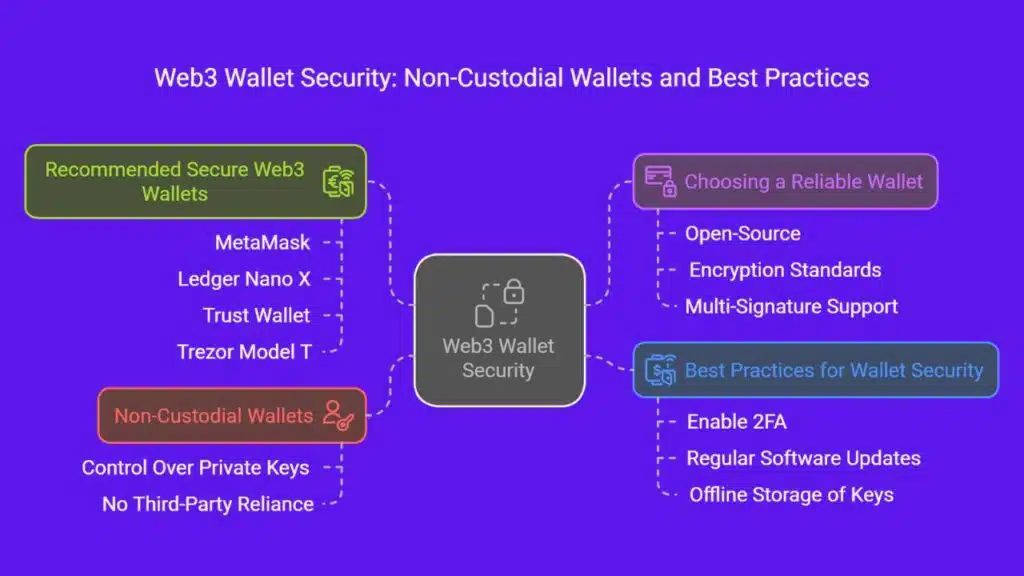
1. Use a Secure and Non-Custodial Wallet
A Web3 wallet is your primary gateway to blockchain-based applications and digital assets. Choosing the right type of wallet and using it securely can significantly reduce your exposure to cyber threats. Non-custodial wallets provide better security since they allow users to control their private keys, unlike custodial wallets, where third-party services manage your funds.
What is a Non-Custodial Wallet?
A non-custodial wallet allows users to retain full control over their private keys, eliminating reliance on third-party services like centralized exchanges. Unlike custodial wallets, which store your assets on your behalf, non-custodial wallets ensure that you are the sole owner of your funds.
Choosing a Reliable Wallet
Selecting a secure wallet is a critical step in Web3 security. Consider the following factors:
- Open-source: Transparency ensures security through community audits.
- Encryption standards: Strong encryption prevents unauthorized access.
- Multi-signature support: Provides additional layers of protection.
Recommended Secure Web3 Wallets
| Wallet | Type | Features |
| MetaMask | Software | Browser extension, mobile app, dApp support |
| Ledger Nano X | Hardware | Offline storage, Bluetooth connectivity |
| Trust Wallet | Software | Multi-asset support, staking options |
| Trezor Model T | Hardware | Secure offline storage, open-source |
Best Practices for Wallet Security
- Enable two-factor authentication (2FA) where applicable.
- Regularly update your wallet software to fix vulnerabilities.
- Store private keys and seed phrases offline, never in cloud storage.
2. Protect Your Private Keys and Seed Phrases
Your private keys and seed phrases are the most critical aspects of Web3 security. They grant complete control over your assets, meaning anyone with access can steal your funds. Cybercriminals employ sophisticated tactics such as malware, phishing, and social engineering to trick users into revealing their keys. Protecting them should be a top priority.
Why Private Keys Matter
Your private keys are the gateway to your assets. If someone gains access to them, they can steal your funds instantly.
Secure Storage Methods
- Hardware wallets: Store private keys offline for maximum security.
- Paper wallets: Physically write down your seed phrase and store it in a safe place.
- Fireproof and waterproof storage: Use safes or metal wallets for added protection.
| Secure Storage Method | Advantages |
| Hardware Wallet | Keeps keys offline, highly secure |
| Paper Wallet | No digital trace, immune to online hacking |
| Metal Wallet | Fireproof, waterproof, and long-lasting |
Common Mistakes to Avoid
- Never share your seed phrase with anyone.
- Avoid storing private keys in cloud storage or note-taking apps.
- Be cautious of scammers impersonating wallet providers.
3. Be Cautious of Phishing Attacks and Scams
Phishing scams are one of the most prevalent threats in Web3. Attackers create fake websites, emails, or messages that mimic legitimate Web3 platforms to trick users into revealing their login credentials or private keys. Knowing how to identify and avoid these scams is essential for securing your digital assets.
Recognizing Phishing Attempts
Phishing scams trick users into revealing their private keys or login credentials. Red flags include:
- Emails claiming urgent security issues requiring immediate action.
- Fake websites mimicking legitimate Web3 platforms.
- Suspicious links sent via direct messages on social media.
| Common Scam Type | How It Works | Prevention Tips |
| Email Phishing | Fake emails impersonating companies | Always verify the sender before clicking links |
| Social Media Scams | Fraudulent accounts offering giveaways | Check official pages for legitimacy |
| Fake Websites | Cloned sites stealing credentials | Always type the official URL manually |
Avoiding Fake Airdrops and Ponzi Schemes
- Always verify airdrop sources from official project channels.
- Research tokenomics and the project’s legitimacy before investing.
Safe Browsing Practices
- Use trusted browser extensions like MetaMask or WalletConnect.
- Verify URLs before connecting your wallet to any dApp.
4. Enable Multi-Signature Security for Transactions
Multi-signature (multi-sig) security adds an extra layer of protection by requiring multiple approvals before executing transactions. This reduces the risk of unauthorized transfers, making it a valuable security measure for individuals and businesses alike.
Multi-sig wallets are particularly beneficial for organizations, investment groups, and high-value asset holders who need a more robust authorization process before processing funds. Implementing multi-signature security minimizes the risks associated with phishing attacks, insider threats, and compromised private keys.
Benefits of Multi-Sig Wallets
- Prevents a single point of failure: Ensures that no single person or device can authorize a transaction, reducing risks of fraud and hacking.
- Requires multiple confirmations for transactions: Transactions need multiple signers’ approvals, adding an extra layer of security.
- Enhances security for shared wallets: Ideal for DAOs, joint investments, and business accounts where multiple parties are involved.
- Mitigates unauthorized access: Even if one key is compromised, attackers cannot execute transactions without additional signatures.
| Multi-Sig Wallet Provider | Key Features |
| Gnosis Safe | Supports multiple signers, customizable security settings |
| Electrum | Open-source, multi-sig support for Bitcoin transactions |
| Casa | User-friendly interface, enhanced personal security features |
| BitGo | Enterprise-grade multi-sig security for institutions |
To maximize security, users should distribute signing authority among trusted parties and avoid keeping all keys on a single device.
5. Stay Updated with Web3 Security Trends
Web3 security threats evolve rapidly, with hackers constantly finding new vulnerabilities in blockchain networks, smart contracts, and decentralized applications. As cyber threats grow more sophisticated, staying informed about the latest risks and security solutions is crucial to safeguarding digital assets. Users must adopt proactive security measures, regularly monitor developments, and utilize reliable security tools to minimize exposure to potential threats.
Trusted Sources for Security Updates
- Web3 security blogs (e.g., CertiK, SlowMist, Immunefi) provide in-depth analysis and reports on security vulnerabilities.
- Blockchain security communities (e.g., Reddit, Twitter, Telegram) offer real-time discussions and alerts on emerging threats.
- Official project documentation and GitHub repositories help users verify the authenticity and security of smart contracts.
- Bug bounty programs (e.g., Immunefi, HackerOne) reveal potential risks and reward ethical hackers for reporting vulnerabilities.
6. Verify Smart Contracts Before Interaction
Smart contracts are self-executing codes that run on blockchain networks, facilitating various transactions and agreements. While they provide automation and transparency, interacting with unaudited or malicious smart contracts can result in financial losses and security breaches.
Hackers often exploit vulnerabilities in poorly written contracts, leading to rug pulls, reentrancy attacks, and phishing scams. To mitigate risks, users must verify contracts before engaging with them.
How to Audit Smart Contracts
- Use blockchain explorers like Etherscan and BscScan to inspect contract details and confirm legitimacy.
- Check security audit reports from firms like CertiK, OpenZeppelin, and Trail of Bits before investing in any Web3 project.
- Verify contract interactions by reviewing permissions granted to smart contracts through tools like Revoke.cash.
- Avoid unaudited contracts or those lacking transparency in governance and source code.
| Security Tool | Purpose |
| Etherscan | Blockchain explorer for verifying contract details |
| CertiK | Security audit provider for smart contracts |
| Revoke.cash | Tool for revoking unnecessary contract permissions |
| OpenZeppelin Defender | Smart contract monitoring and security services |
7. Diversify and Secure Your Investments
Diversifying your assets across multiple wallets and platforms is a fundamental security strategy in Web3. Relying on a single wallet or exchange increases the risk of total asset loss in the event of a breach. By spreading funds across different storage solutions, users can minimize exposure to hacks, fraud, and operational failures. Additionally, using different types of wallets for various purposes enhances security and ease of use.
Best Practices
- Use hot wallets for daily transactions and frequent trades. These wallets provide convenience but should only hold a limited amount of assets due to their online exposure.
- Use cold wallets for long-term storage of valuable assets. Hardware wallets and offline storage options are the safest ways to secure cryptocurrencies and NFTs.
- Segment your funds by purpose, such as having separate wallets for DeFi activities, long-term investments, and NFT collections.
- Regularly review and update security settings on all wallets to ensure they align with the latest security protocols.
| Storage Type | Use Case | Security Level |
| Hot Wallet | Daily transactions & trading | Moderate |
| Cold Wallet | Long-term asset storage | High |
| Multi-Sig Wallet | Shared or business transactions | Very High |
Takeaways
Securing your assets in Web3 requires a proactive approach. By following these best practices for staying secure in Web3, you can significantly reduce risks and protect your digital identity.
Implementing strong security measures, staying informed, and using trusted tools are essential for navigating the decentralized world safely.