The rise of digital platforms has increased efficiency, collaboration, and access to information across industries. At the same time, it has amplified exposure to security failures that can compromise sensitive data at scale. One such incident that has drawn sustained attention is thejavasea.me leaks aio-416, a topic that continues to surface in discussions around data integrity, digital trust, and platform accountability.
This subject matters because it sits at the intersection of technology operations, ethical responsibility, and long-term digital risk. Whether you are a business leader, a technical professional, or an informed digital user, understanding what happened and why it matters is essential to navigating today’s information environment responsibly.
This article provides a deep, structured examination of thejavasea.me leaks aio-416. It moves beyond surface-level commentary to explain the underlying dynamics, the broader implications, and the strategic lessons that organizations and individuals can draw from the situation.
Understanding the Context Behind thejavasea.me Leaks AIO-416
At its core, thejavasea.me leaks aio-416 refers to a documented instance of exposed digital material associated with the thejavasea.me platform, categorized under an internal or reference identifier known as AIO-416. While the label itself is technical, the implications are not. It represents a failure in safeguarding information that was not intended for unrestricted access.
Such leaks typically occur when systems designed to manage, store, or distribute data lack sufficient controls. This can include weak access permissions, poor infrastructure oversight, or inadequate monitoring of how content is indexed and retrieved. The significance of thejavasea.me leaks aio-416 lies less in the identifier and more in what it reveals about systemic vulnerabilities.
From a strategic perspective, these events highlight how digital ecosystems can fail quietly before consequences become visible. By the time users become aware, exposure has often already occurred.
What the Service Environment Involved
To understand thejavasea.me leaks aio-416 properly, it is important to consider the type of digital environment in which such an issue can arise. Platforms that aggregate, host, or distribute digital content often rely on layered systems. These include databases, access logic, automation tools, and third-party integrations.
When these layers are not aligned under a cohesive governance model, gaps emerge. A single misconfigured endpoint or automated process can bypass intended restrictions. In the case of thejavasea.me leaks aio-416, the exposure suggests that internal segmentation between public-facing and restricted material was insufficiently enforced.
This is not an uncommon problem. Many platforms scale functionality faster than security oversight, especially when growth metrics are prioritized over resilience.
The Methodological Breakdown of How Leaks Occur
Data exposure events like thejavasea.me leaks aio-416 rarely result from a single catastrophic error. More often, they emerge from a sequence of smaller decisions that compound over time.
Typically, the process follows a pattern. Data is stored centrally. Access rules are defined but not regularly audited. Automation scripts or indexing tools are introduced for efficiency. Over time, edge cases appear where data becomes reachable through unintended pathways.
What makes these situations difficult to detect is that systems continue to function normally. Users experience no visible disruption. Internally, teams assume controls are working as designed. The leak only becomes apparent when external actors discover and share the exposed material.
This reinforces the importance of continuous verification rather than one-time configuration.
Core Principles Highlighted by the Incident
Several foundational principles emerge when analyzing thejavasea.me leaks aio-416. The first is that security is not a static state. Controls that were sufficient at one stage of platform maturity may become inadequate as complexity increases.
The second principle is accountability. Digital platforms carry an implicit responsibility to protect the data they handle, regardless of whether that data belongs to users, partners, or internal operations. Failure to do so undermines trust, which is difficult to rebuild once lost.
Finally, transparency matters. How organizations respond after exposure often shapes public perception more than the exposure itself. Silence or deflection amplifies reputational damage.
Who Is Most Affected by This Type of Exposure
The immediate impact of thejavasea.me leaks aio-416 is felt by users whose data or content may have been exposed. However, the ripple effects extend much further.
Platform operators face long-term credibility challenges. Technical teams may experience increased scrutiny and pressure. Partners may reconsider integrations. Even unrelated users can lose confidence, leading to reduced engagement.
From a leadership standpoint, these incidents test governance structures. They reveal whether risk management is embedded into decision-making or treated as an afterthought.
Measurable Consequences and Outcomes
While not all consequences are immediately visible, data exposure events often produce measurable outcomes over time. These can include reduced user activity, increased support costs, and the need for costly infrastructure overhauls.
In strategic terms, thejavasea.me leaks aio-416 underscores how reactive remediation is always more expensive than proactive prevention. Organizations frequently invest significantly more after an incident than they would have spent on preventive audits and controls.
There is also the less tangible but equally critical cost of lost trust. Trust erosion affects brand equity, stakeholder relationships, and long-term sustainability.
How This Differs From Isolated Technical Errors
It is tempting to view incidents like thejavasea.me leaks aio-416 as isolated technical mistakes. This framing is misleading. While technical missteps may trigger exposure, the root causes are often organizational.
These include unclear ownership of data governance, insufficient cross-team communication, and leadership that underestimates digital risk. Unlike a one-off system failure, leaks reveal deeper structural weaknesses.
Understanding this distinction is crucial for meaningful change. Fixing a single bug does not address systemic vulnerability.
Real-World Strategic Scenarios
Consider a digital platform scaling rapidly to meet demand. Features are deployed quickly. Security reviews are postponed. Over time, complexity outpaces oversight. Eventually, exposed data surfaces externally.
This scenario mirrors the dynamics behind thejavasea.me leaks aio-416. It demonstrates how well-intentioned growth strategies can inadvertently create risk when governance does not evolve in parallel.
For executives, the lesson is clear. Digital strategy must integrate security as a core pillar, not a secondary consideration.
Common Challenges Addressed by This Case
One major challenge highlighted is the difficulty of maintaining visibility across complex systems. As platforms grow, no single individual fully understands every dependency.
Another challenge is cultural. Teams may fear slowing innovation by raising security concerns. This creates an environment where risks are acknowledged but not addressed.
Thejavasea.me leaks aio-416 illustrates the cost of these challenges when left unresolved.
Strategic Impact on Organizations and Leadership
From a leadership perspective, incidents like thejavasea.me leaks aio-416 force a reevaluation of priorities. They prompt questions about oversight, accountability, and risk appetite.
Organizations that respond strategically use these moments to strengthen governance frameworks, clarify roles, and invest in long-term resilience. Those that respond defensively often repeat similar mistakes.
The difference lies in whether leadership treats exposure as an anomaly or as feedback on systemic health.
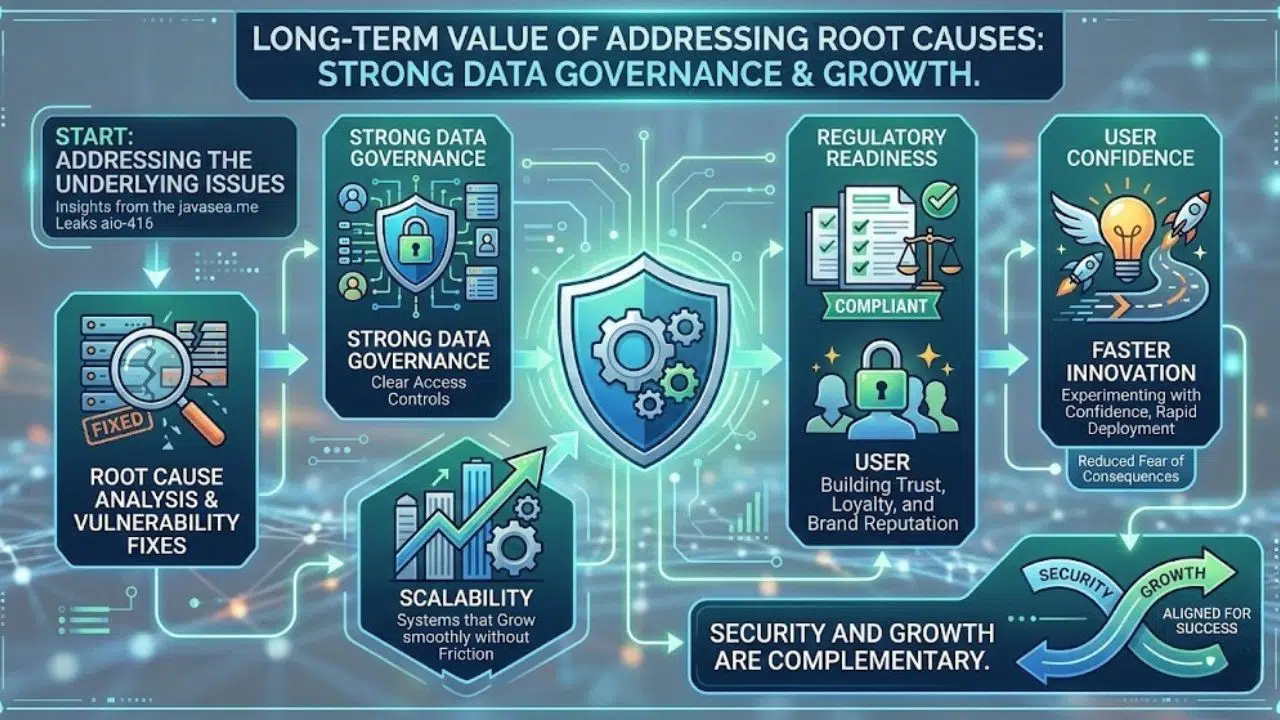
Long-Term Value of Addressing the Root Causes
Addressing the underlying issues revealed by thejavasea.me leaks aio-416 offers long-term value beyond risk reduction. Strong data governance supports scalability, regulatory readiness, and user confidence.
It also enables faster innovation. When systems are well-governed, teams can move quickly without fear of unintended consequences.
In this sense, security and growth are not opposing forces. They are complementary when aligned correctly.
Authority and Trust in the Modern Digital Landscape
In today’s environment, trust is a strategic asset. Users and partners increasingly evaluate platforms based on how they handle data and respond to issues.
Thejavasea.me leaks aio-416 serves as a reminder that trust is built through consistent, ethical behavior over time. It is reinforced by evidence-based practices, clear accountability, and transparent communication.
Organizations that internalize these principles position themselves for sustainable success.
Ethical Considerations and Responsibility
Beyond technical and strategic dimensions, there is an ethical layer. Platforms hold power over information that can affect individuals and communities. With that power comes responsibility.
Ethical stewardship requires anticipating harm, not merely reacting to it. It involves designing systems that default to protection rather than exposure.
The lessons from thejavasea.me leaks aio-416 extend into this ethical domain, emphasizing the human impact of digital decisions.
Frequently Asked Questions
What does thejavasea.me leaks aio-416 refer to?
It refers to an identified instance of exposed digital material associated with the thejavasea.me platform, categorized under an internal reference labeled AIO-416. The term highlights a data exposure issue rather than a single isolated file.
Why is thejavasea.me leaks aio-416 considered significant?
The significance lies in what it reveals about systemic vulnerabilities in digital platforms. It illustrates how insufficient governance and oversight can lead to unintended data exposure with long-term consequences.
Is thejavasea.me leaks aio-416 the result of hacking?
Available analysis suggests that such incidents more commonly stem from misconfiguration or process failures rather than direct external attacks. This distinction is important for understanding prevention strategies.
Who bears responsibility in cases like thejavasea.me leaks aio-416?
Responsibility typically rests with platform operators and leadership structures that oversee data governance. Effective accountability involves both technical teams and executive decision-makers.
What lessons can organizations learn from thejavasea.me leaks aio-416?
Organizations can learn the importance of continuous security auditing, clear ownership of data governance, and integrating risk management into strategic planning rather than treating it as a technical afterthought.
How can similar incidents be prevented in the future?
Prevention requires regular access reviews, strong internal controls, transparent processes, and leadership commitment to security as a strategic priority.
Final Thoughts
Thejavasea.me leaks aio-416 is more than a technical reference. It is a case study in how digital systems, organizational culture, and leadership priorities intersect. By examining it closely, we gain insight into the real cost of overlooking governance in favor of speed or convenience.
For organizations and individuals alike, the long-term value lies in learning from these events. Building resilient digital environments requires foresight, discipline, and ethical commitment. Those who apply these lessons position themselves not only to avoid future exposure, but to earn lasting trust in an increasingly complex digital world.