The enterprise landscape has shifted entirely to the cloud, making SaaS security the top priority for IT leaders this year. Finding the best SaaS security tools 2026 requires balancing deep configuration visibility with automated threat response across hundreds of third-party applications.
Modern security teams no longer rely on perimeter defense but instead focus on the identity and data layers within each application. This guide analyzes the essential platforms designed to stop data exfiltration and configuration drift in your cloud ecosystem.
How We Picked Our Top 10 List?
Our evaluation process is rigorous and relies on public data from the current year. We prioritize the long-term safety of user data above any short-term convenience. This ensures that the tools we recommend are stable for the foreseeable future.
We applied the following weightings to our research and comparison efforts.
| Criteria | Weighting | Focus Area |
| Integration Depth | 40% | Support for 150+ major SaaS apps |
| Threat Detection | 30% | Real-time AI-driven anomaly tracking |
| Ease of Setup | 30% | Deployment time and UI simplicity |
10 Best SaaS Security Tools in 2026 Explained!
The following platforms represent the gold standard for protecting your business-critical applications this year. We have evaluated these tools based on their ability to secure sensitive data while maintaining high operational speed.
1. Netskope One
Netskope remains a top-tier choice in 2026 by combining its industry-leading CASB with a unified security service edge. It provides granular visibility into how data moves between sanctioned and unsanctioned applications.
Analysts should note the following performance capabilities and operational requirements for this platform.
Special Features:
-
Real-time zero delay data loss prevention
-
Graph-powered visualization of hidden risks
-
Next-gen secure web gateway integration
Things to Consider:
-
Complex initial setup for large enterprises
-
High premium pricing for advanced tiers
-
Requires a unified agent for maximum effectiveness
Best for: Global enterprises requiring strict data sovereignty and DLP controls.
2. Obsidian Security
Obsidian is the premier choice for organizations that prioritize identity and supply chain security in 2026. It unifies the management of permissions and OAuth scopes into a single model. This prevents breaches that often occur through third-party integrations and plug-ins.
The platform offers the following advantages and considerations for modern security teams.
Special Features:
-
Automated SaaS supply chain breach notifications
-
Least privilege policy enforcement for integrations
-
Continuous monitoring of user activity and anomalies
Things to Consider:
-
Focuses heavily on identity rather than network traffic
-
Requires deep integration with HR and IT systems
-
Pricing is based on the number of users and apps
Best for: Security operations teams focused on identity threat detection and response.
3. Zscaler Unified SaaS Security
Zscaler has expanded its Zero Trust Exchange in 2026 to include a fully unified SaaS security module. It uses AI to identify suspicious activity and block access to risky applications before they can compromise your data.
Users should weigh these specific benefits and infrastructure requirements before deployment.
Special Features:
-
AI-powered threat detection for automated blocking
-
Seamless zero-trust network access integration
-
Comprehensive visibility into shadow IT applications
Things to Consider:
-
Best used as part of the broader Zscaler ecosystem
-
Can be complex to manage without dedicated training
-
Infrastructure heavy approach compared to pure SSPM
Best for: Organizations already using Zscaler for zero-trust network security.
4. Adaptive Shield (By CrowdStrike)
Now fully integrated into the CrowdStrike Falcon ecosystem, Adaptive Shield provides deep posture management. It identifies security drifts across all application controls and provides step-by-step remediation instructions.
The integration provides the following unique strengths and operational challenges for IT admins.
Special Features:
-
Automated posture assessment against industry benchmarks
-
Detailed remediation guides for misconfigurations
-
Unified visibility within the Falcon security console
Things to Consider:
-
Optimized primarily for existing CrowdStrike customers
-
Some features are locked behind higher Falcon tiers
-
Periodic syncing is required for real-time accuracy
Best for: Enterprises standardizing their security operations on the CrowdStrike platform.
5. Wiz
Wiz has revolutionized SaaS security by using a security graph to highlight toxic combinations of risks. In 2026, it excels at identifying attack paths that span from your cloud infrastructure into your SaaS applications.
This platform provides the following visual and automated security measures.
Special Features:
-
Toxic risk combination identification via graph
-
Deep visibility into SaaS-to-cloud interdependencies
-
Automated compliance frameworks for HIPAA and GDPR
Things to Consider:
-
Can be overwhelming for smaller IT teams
-
High resource usage during initial discovery scans
-
Premium price point reflects its enterprise focus
Best for: Large organizations with complex multi-cloud and SaaS environments.
6. AppOmni
AppOmni specializes in continuous configuration monitoring for the most widely used enterprise applications. It is particularly strong at managing the deep settings of platforms like Salesforce, ServiceNow, and Microsoft 365.
Teams should consider these specific operational advantages and limitations.
Special Features:
-
Standardized security controls across major app suites
-
Monitoring of risky third-party app connections
-
Guided fixes for posture and exposure issues
Things to Consider:
-
Best for core enterprise suites rather than niche apps
-
Requires individual app connectors for deep visibility
-
Average annual costs can be higher for mid-market users
Best for: Enterprises centered on Salesforce and Microsoft 365 environments.
7.Grip Security
Grip acts as a SaaS security control plane that focuses on discovering and managing your entire SaaS estate. It is the most effective tool for finding shadow SaaS and reclaiming control over identity drift in 2026.
The system offers the following discovery and management capabilities.
Special Features:
-
Universal discovery of both sanctioned and shadow apps
-
Automated remediation of identity risks
-
Consolidation of identity management across the estate
Things to Consider:
-
High entry price point for smaller businesses
-
Focuses on discovery more than deep per-app settings
-
Management console requires dedicated oversight
Best for: Organizations facing significant shadow IT and identity management challenges.
8. Reco AI
Reco provides identity-centric SaaS security with a strong emphasis on AI governance and user behavior. It maps user permissions and monitors OAuth connections to find hidden security gaps in your environment.
Security analysts should review the following features and pricing considerations.
Special Features:
-
AI governance and monitoring of AI app usage
-
Deep visibility into machine and human identities
-
Business context-aware risk prioritization
Things to Consider:
-
Quote-based pricing can be difficult to predict
-
Requires high level of app integration to be effective
-
UI may feel complex for non-security personnel
Best for: Teams needing deep visibility into AI app usage and identity governance.
9. Varonis
Varonis is a leader in data security that has evolved into a powerful SaaS protection platform in 2026. It focuses on finding where sensitive data is stored and ensuring that only the right people have access to it.
The platform provides the following data-centric security controls.
Special Features:
-
Automated data classification and protection
-
User behavior analytics to detect data exfiltration
-
Least privilege automation for data folders
Things to Consider:
-
Resource intensive to deploy and maintain
-
Primarily focused on the data layer rather than settings
-
Pricing can scale quickly with data volume
Best for: Organizations with massive amounts of sensitive unstructured data.
10. Wing Security
Wing specializes in mid-market SaaS security with an emphasis on automated discovery and remediation. It is designed to be a low-friction solution that provides rapid value for growing companies.
The following details define the Wing Security value proposition in 2026.
Special Features:
-
Low-friction automated remediation workflows
-
Extensive discovery of third-party app connections
-
Compliance monitoring for SOC 2 and HIPAA
Things to Consider:
-
May lack the deep customization of larger platforms
-
Focused primarily on the most popular 200+ apps
-
Support response times can vary for basic tiers
Best for: Mid-market companies needing strong discovery and automated remediation.
How Should You Choose The Best Option For You
Selecting the right platform depends on whether you prioritize data, identity, or infrastructure security. You should first evaluate where your most sensitive information lives and which applications carry the highest risk for your organization.
| Category | Top Pick | Primary Reason |
| Data Protection | Netskope One | Best in class real-time DLP |
| Identity Security | Obsidian | Unified identity and supply chain model |
| Risk Visibility | Wiz | Graph-powered toxic combination detection |
| Shadow IT | Grip Security | Universal discovery of unsanctioned apps |
SaaS Cybersecurity Software Overview
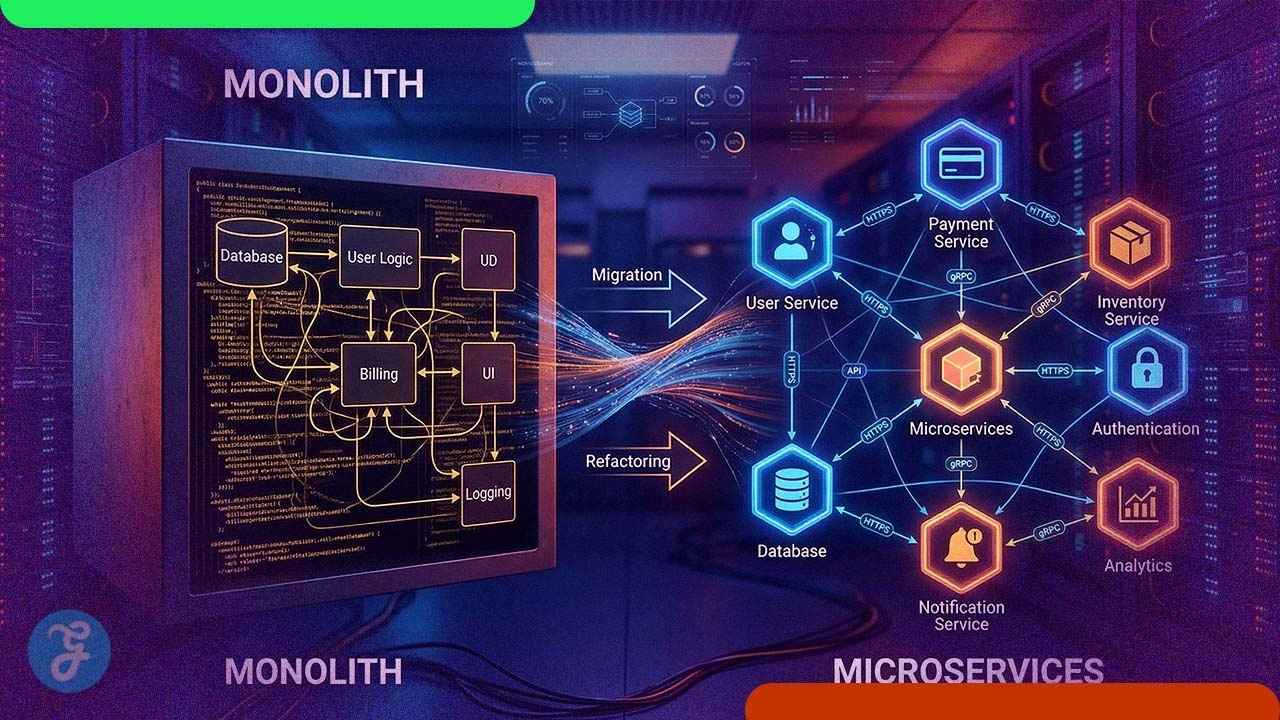
The 2026 market is dominated by SaaS Security Posture Management (SSPM) and advanced Cloud Access Security Brokers (CASB). These tools are essential for managing the complexity of modern cloud estates. The following table provides a high level look at the leading solutions.
| Tool Name | Tool Category | Primary Focus | Security Rating |
| Netskope One | CASB / SSE | Data Loss Prevention | 5/5 |
| Obsidian Security | SSPM | Identity & Supply Chain | 4.8/5 |
| Zscaler SaaS | CASB / ZTNA | Zero Trust Access | 4.9/5 |
| Adaptive Shield | SSPM | Configuration Drift | 4.7/5 |
| Wiz Platform | CNAPP / SSPM | Graph-based Exposure | 5/5 |
| AppOmni | SSPM | Enterprise Connections | 4.6/5 |
Wrap-Up
Finding the best SaaS security tools in 2026 is an ongoing journey as your application stack evolves. By implementing a combination of SSPM and CASB features, you can significantly reduce your attack surface. Always prioritize tools that offer deep integration with your existing security ecosystem.
The goal of SaaS protection is to enable business agility while maintaining strict data control. Start by auditing your most critical apps and choosing a platform that provides the visibility you currently lack. Continuous monitoring and automated remediation will be your strongest allies in the year ahead.