Cyberattacks are getting smarter. Your old security measures might not be enough to stop them. Hackers target websites every day, stealing data or causing crashes.
Good news: New security protocols for future hosting are here to fight back. One key change is the rise of AI-powered tools that spot threats faster than humans. These systems learn from attacks and adapt in real time.
This post will show you 10 upgrades coming to hosting security, like zero trust rules and better encryption. You’ll learn how to stay ahead of risks without slowing down your site.
Keep reading to see what’s next.
Key Takeaways
- AI-powered tools detect threats faster than humans, learning and adapting to stop breaches before they happen. These systems work with encryption and multi-factor authentication for stronger security.
- Zero Trust Architecture checks every login attempt, device, and API call, using dynamic rules like user behavior to block unauthorized access. Tools like cryptographic signing keep data safe from tampering.
- Biometric verification (fingerprints, face scans) adds extra protection beyond passwords. It works with AI to spot fake attempts and fits Zero Trust models for tighter access control.
- Future hosting uses quantum-resistant encryption and blockchain to guard against hackers. Edge computing protocols add real-time threat scans while keeping data close to users for speed.
- Automated cloud backups run 24/7 with strong encryption and virus checks. Recovery is fast, meeting strict rules like GDPR and ISO 27001 to avoid fines and breaches.
Zero Trust Architecture Implementation
Zero Trust Architecture flips old security rules on their head. Instead of trusting users inside a network, it checks every login attempt, device, and API call before granting access.
Think of it like a bouncer who double-checks your ID every time you step into a club, even if they know your face.
This model relies on dynamic context—like user behavior and real-time threats—to block unauthorized access. Companies should only use verified servers to avoid supply chain attacks.
Tools like cryptographic signing and package verification help keep these systems safe from tampering. Multi-factor authentication (MFA) and strict access controls make sure only the right people get in, reducing risks like phishing scams or brute force attacks.
AI-Powered Security Automation
AI-powered security automation is changing how hosting providers fight cyber threats. Criminals now use AI to bypass defenses, leaving almost no traces. Automated tools powered by machine learning spot these attacks fast, stopping breaches before they happen.
These systems analyze user activity, detect malicious code, and block threats in real time. They work with security information and event management (SIEM) tools to monitor cloud infrastructure.
AI also helps with spam filtering, DDoS protection, and data loss prevention. The best part? They reduce human error while speeding up response times.
MCP makes AI security tools work better across different platforms. It standardizes how apps interact with machine learning models, cutting development time. This means faster updates and stronger protection for your data.
No more waiting for patches or manual fixes. The system learns, adapts, and acts on its own.
Multi-Factor Authentication (MFA) Enhancements
Multi-factor authentication (MFA) is getting stronger. It now goes beyond simple text codes, using tools like passkeys and Windows Hello for smoother security. Adding biometrics, such as fingerprints or facial recognition, makes hacking much harder.
Regularly checking access rights keeps sensitive data safer. MFA beats passwords alone every time by adding extra layers of protection. Behavioral biometrics can even track how you type to confirm it’s really you logging in.
With tighter cybersecurity laws and cloud storage at risk, these upgrades are a must for anyone serious about stopping data breaches.
Biometric Verification Integration
Biometric verification is changing how we control access in hosting security. It uses fingerprints, face scans, or even voice recognition to confirm identities. This works with multi-factor authentication (MFA) for stronger protection.
AI and machine learning help spot fake attempts, making it harder for attackers to break in.
Zero Trust models rely on biometrics to check every user and device. Storing this data safely is key, following strict privacy rules. Hosting providers now use advanced biometrics to stop unauthorized access.
It’s faster than typing passwords and harder to fool. Security gets stronger without slowing users down.
Enhanced Data Encryption Techniques
Future hosting will lock down your data like a vault with smarter encryption. Current methods might not stand up to quantum computers, so new quantum-resistant algorithms are in the works.
These will protect encrypted data from being cracked by next-gen tech.
Blockchain is shaking things up too, spreading storage across multiple nodes instead of one risky target. Expect stronger transport layer security (TLS) protocols and better decryption keys for airtight cloud security.
Even IoT devices will get tougher shields, making breaches far harder to pull off. Data privacy stays front and center while keeping performance smooth.
Decentralized Hosting Security Measures
Decentralized hosting distributes data across various locations rather than depending on a single central server as traditional setups do. This method reduces risks associated with single points of failure, making cyber attacks more challenging.
Blockchain technology plays a significant role here. It ensures information security by fragmenting it into parts stored on different nodes. Hybrid clouds also align well with this model, safeguarding sensitive data privately while utilizing public clouds for scalability.
With decentralized systems, hackers cannot target one specific point to cause widespread damage. Content delivery networks assist by improving speed and accessibility without sacrificing security.
Virtual private networks add an extra layer of protection for remote workers accessing these systems. Decentralization results in better uptime and reduced occurrences of breaches.
Security reviews gain efficiency through enhanced tracking of user activity across the network.
Passwords alone are no longer sufficient, but decentralization addresses that. Passwordless authentication methods such as tokens or biometric verification integrate seamlessly into these frameworks.
Multi-factor authentication further strengthens logins. Since each node retains only a portion of the data, losing one won’t compromise everything. Windows 11 and other operating systems are adapting to support this technology as well.
Information security progresses when no single entity holds complete control. The SolarWinds hack demonstrated the risks of centralized systems. Decentralized hosting mitigates such vulnerabilities by distributing risks.
LAN Manager protocols and IPv6 optimizations also perform more effectively in this setup. Data management becomes more streamlined, and backups are automatically distributed across locations.
Cybersecurity experts favor this model for its strength in preventing large-scale attacks.
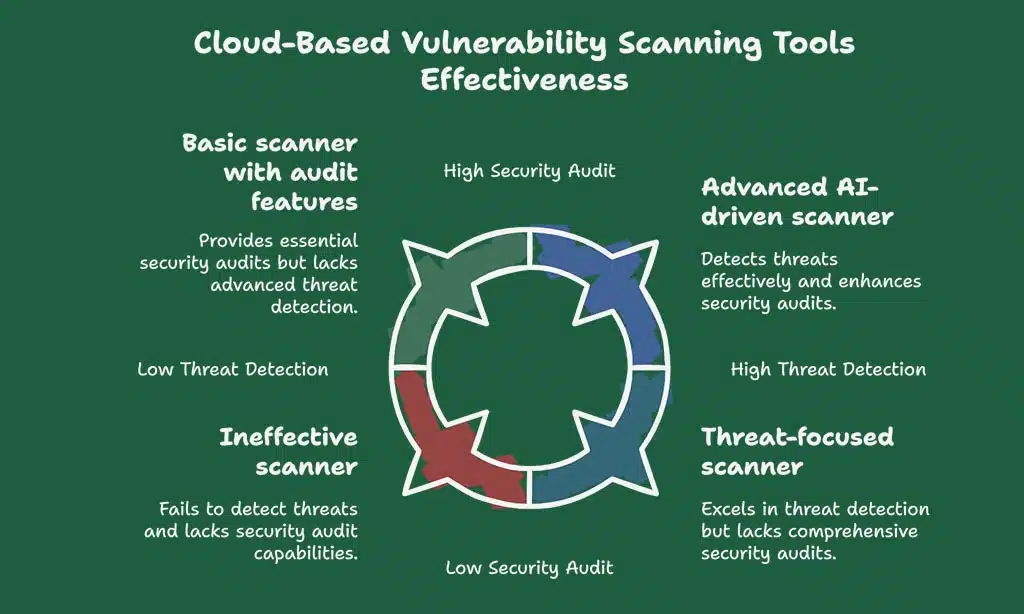
Cloud-Based Vulnerability Scanning Tools
Cloud-based vulnerability scanning tools keep your data safe by checking for weak spots. These tools scan web apps, cloud storage, and even IoT devices in real time, spotting risks fast.
They use AI and machine learning to detect threats before they cause damage.
Regular scans help tighten security audits and fix issues quickly. Some tools also check if backups are encrypted or flag unauthorized access. With cloud services growing, these scanners are essential for strong data security.
They work with zero trust principles to block attacks early.
Real-Time Security Monitoring and Alerts
Hackers move fast, but real-time security monitoring keeps up. It tracks user activity, detects threats the second they happen, and sends instant alerts to stop breaches before damage spreads.
Without built-in runtime tracking, investigating incidents is like finding a needle in a haystack—slow and frustrating.
Systems now use AI to watch over cloud services, IoT devices, and login attempts 24/7. Suspicious actions trigger alarms for cybersecurity specialists to review immediately. This stops small issues from becoming big disasters while keeping data privacy intact.
Constant visibility matters more than ever with remote work on the rise.
Privacy-First Hosting Features
Privacy-first hosting puts your data safety ahead of everything else. It means strict rules like GDPR and ISO 27001 are baked into the service, so your information stays locked down.
Think automatic encryption for stored files, no sneaky data tracking, and tools that let you control who sees what. Cloud storage gets safer with features like user activity monitoring, making sure only the right eyes access sensitive details.
Hosting providers now use advanced methods to keep prying hands off your stuff. They block unwanted snoops with web application firewalls and private clouds. Multi-factor authentication adds an extra lock on your account, while single sign-on makes access smooth but secure.
Even cookies get smarter, storing less personal info to reduce risks. With these steps, your data stays yours—no surprises, no leaks.
Automated Backup and Recovery Protocols
Backups keep your data secure. Recovery plans retrieve it quickly when issues arise.
- Cloud backups operate on a set schedule. No need to manually save files.
- Data is stored away from your primary systems. This safeguards it from local disasters like fires or floods.
- Every backup is secured with strong encryption. Only the correct key can access it later.
- Systems automatically check backups for errors. Corrupted files are repaired or replaced before you need them.
- Advanced tools scan backups for viruses as well. Secure files mean safer restore points.
- Cloud services allow you to choose how often backups occur. Set hourly, daily, or weekly saves based on your needs.
- Recovery starts with a simple click. Retrieve lost files effortlessly while enjoying your morning coffee.
- Backups operate continuously, even while you sleep. Servers work tirelessly around the clock.
- Test restores take place in isolated copies first. This ensures no risk to your active data.
- Multi-factor authentication protects backup settings. Additional login steps keep hackers at bay.
- Backup logs track every save attempt. Spot potential issues before they escalate.
- Storage expands as your data grows. You pay only for the space you use.
- Disaster recovery plans incorporate these backups. When challenges arise, the system takes swift action.
Compliance with Stricter Data Protection Regulations
Hosting providers must follow strict rules like ISO 27001, PCI DSS, and GDPR to keep data safe. These standards help protect user information from breaches and misuse. Companies that fail to comply risk heavy fines or losing customer trust.
Regular security audits and compliance checks are now a must for any reliable cloud services provider.
Providers also offer disaster recovery solutions and 24/7 support to meet these regulations. Multi-factor authentication (MFA) and advanced encryption techniques play a big role in staying compliant.
With laws getting tougher, hosting services need scalable systems that adapt quickly. Data privacy is no longer optional—it’s the foundation of modern hosting security.
Takeaways
Future hosting is getting safer, smarter, and faster. With AI guards, unbreakable encryption, and face scans replacing passwords, your data stays locked tight. Hackers won’t know what hit them.
Stay ready—these changes are coming soon. The web just got a whole lot tougher to crack.
FAQs on Future Hosting Security Protocols
1. What are the top security trends in future hosting?
Future hosting will use multi-factor authentication (MFA), zero trust principles, and passwordless logins. AI and machine learning will help detect threats faster.
2. How does AI improve cloud security?
AI analyzes data privacy risks, spots unusual activity, and helps secure cloud storage. It works with machine learning to block attacks before they happen.
3. Why is changing passwords no longer enough?
Hackers easily crack weak passwords. Future hosting relies on MFA, trusted platform modules, and security processors for stronger protection.
4. What is zero trust in hosting security?
Zero trust means no device or user is trusted by default. Every access request gets checked, whether from teleworking staff or IoT devices.
5. Will passwordless authentication replace traditional logins?
Yes. Passwordless methods, like Microsoft accounts with biometrics or security keys, reduce risks. No more forgotten passwords, just smoother, safer access.