Cloud services were built to move fast and scale across borders. Rules and risks do not work that way. Laws, regulators, customers, and courts still care where data sits, who can access it, and which legal system applies when something goes wrong. That is why cloud sovereignty has become a serious business topic, not a niche compliance debate.
In simple terms, sovereignty means control. It means you can keep sensitive data inside a defined boundary, manage access with confidence, and prove it during audits. It also means you understand the tradeoffs. In some cases, “local” adds cost or limits features. In other cases, it prevents fines, delays, and lost deals.
This guide breaks down cloud sovereignty in a practical way. You will learn what it is, what it is not, why it is rising now, and how to build a setup that keeps data local over time.
Cloud Sovereignty: A Practical Definition
Cloud sovereignty means an organization can control where its data is stored and processed, who can access it, and which legal rules apply. It usually includes three layers:
-
Legal control, meaning the governing laws and court jurisdiction
-
Operational control, meaning who runs and supports the environment day to day
-
Technical control, meaning the tools that enforce boundaries and protect data
Many providers and analysts describe sovereign cloud in similar terms, often tying it to data, operational, and digital sovereignty.
What cloud sovereignty is not:
-
It is not the same as “we picked a cloud region”
-
It is not a promise that no foreign government will ever request access
-
It is not a single product you can buy once and forget
You should treat sovereignty as a design goal. You build it through architecture, controls, contracts, and operating discipline.
| Key Idea | What It Means In Practice | Common Mistake |
|---|---|---|
| Legal layer | Contracts, jurisdiction, transfer rules | Assuming “local data center” solves legal exposure |
| Operational layer | Local operations, support access, incident response | Ignoring who can access systems during support |
| Technical layer | Residency controls, encryption, keys, monitoring | Forgetting logs, backups, and telemetry can move |
Cloud Sovereignty Vs Data Sovereignty Vs Data Residency Vs Data Localization
These terms overlap, but they are not interchangeable.
Data sovereignty focuses on legal authority. If your company must follow GDPR, banking rules, or public sector directives, the legal layer matters most. GDPR also restricts transfers of personal data outside the EEA unless specific conditions are met.
Data residency focuses on location. It answers, “Where is the data stored?” That is necessary, but it is not enough.
Data localization is stricter. It can require certain data types to stay in-country and sometimes requires local processing too. Many jurisdictions use localization rules for finance, telecom, health, and government data.
A helpful way to remember it:
-
Residency is about place
-
Sovereignty is about control and proof
-
Localization is about mandatory local rules
| Term | Core Meaning | Typical Proof |
|---|---|---|
| Data residency | Data stored in a specific place | Region settings, storage location evidence |
| Data sovereignty | Data governed by local laws and enforceable controls | Contracts, access logs, key control, audit reports |
| Data localization | Laws require data to remain local | Legal mapping, regulator-ready documentation |
| Cloud sovereignty | Combined legal, operational, technical control | Boundary design + operating model + evidence |
Why Cloud Sovereignty Is Rising Now
Cloud spending keeps growing. Forecasts from major analysts show public cloud usage expanding rapidly, which increases the volume of sensitive data moving into shared platforms.
At the same time, scrutiny on cross-border transfers has intensified. In Europe, GDPR sets restrictions on transferring personal data outside the EEA. The Schrems II ruling in July 2020 invalidated the EU-US Privacy Shield and raised the bar for transfer risk assessments and safeguards.
Although the EU later adopted a new adequacy decision for the EU-US Data Privacy Framework in July 2023, the topic remains contested and closely watched.
Another driver is lawful access laws. In the US, the CLOUD Act clarifies that providers under US jurisdiction can be compelled to produce data in their “possession, custody, or control,” even if stored abroad. This does not mean automatic access to everything. It does mean legal exposure is more complex than simple geography.
Finally, geopolitics and supply-chain risk push governments and regulated industries to ask for stronger guarantees. That is one reason large providers now offer more explicit “data boundary” and “sovereign cloud” options.
| Driver | Why It Matters | Example Signal |
|---|---|---|
| Regulatory enforcement | Higher cost of non-compliance | GDPR transfer restrictions and enforcement actions |
| Cross-border risk | Transfer rules can change quickly | Schrems II impact on EU-US transfers |
| Lawful access exposure | Jurisdiction can extend beyond location | CLOUD Act scope discussion |
| Market response | Providers build sovereign offerings | Sovereign cloud announcements and data boundaries |
The Three Layers Of Sovereignty You Must Design For
Legal Sovereignty
Legal sovereignty focuses on jurisdiction, contract terms, and transfer mechanisms. For many organizations, the goal is not “zero risk.” The goal is known risk with controls that regulators accept.
Key items to address:
-
Which entity is your contracting party
-
Where disputes are handled
-
What transparency you get on government access requests
-
How sub-processors are handled and disclosed
Operational Sovereignty
Operational sovereignty is about people and process. Who can access systems during support. Where those people are located. How incident response works when something breaks at 3 a.m.
This is where many “residency only” plans fail. Data can stay in-country while privileged operators work from outside.
Technical Sovereignty
Technical sovereignty is where you enforce boundaries:
-
Residency controls for storage and processing
-
Strong identity and access control
-
Encryption with meaningful key ownership
-
Local logging and monitoring
-
Backup and disaster recovery rules that do not copy data elsewhere
| Layer | What You Control | What To Document |
|---|---|---|
| Legal | Jurisdiction, contracts, transfer tools | DPAs, SCC posture, audit rights |
| Operational | Support access, admin process | Access approvals, incident playbooks |
| Technical | Location, encryption, keys, monitoring | Architecture diagrams, key policies, logs |
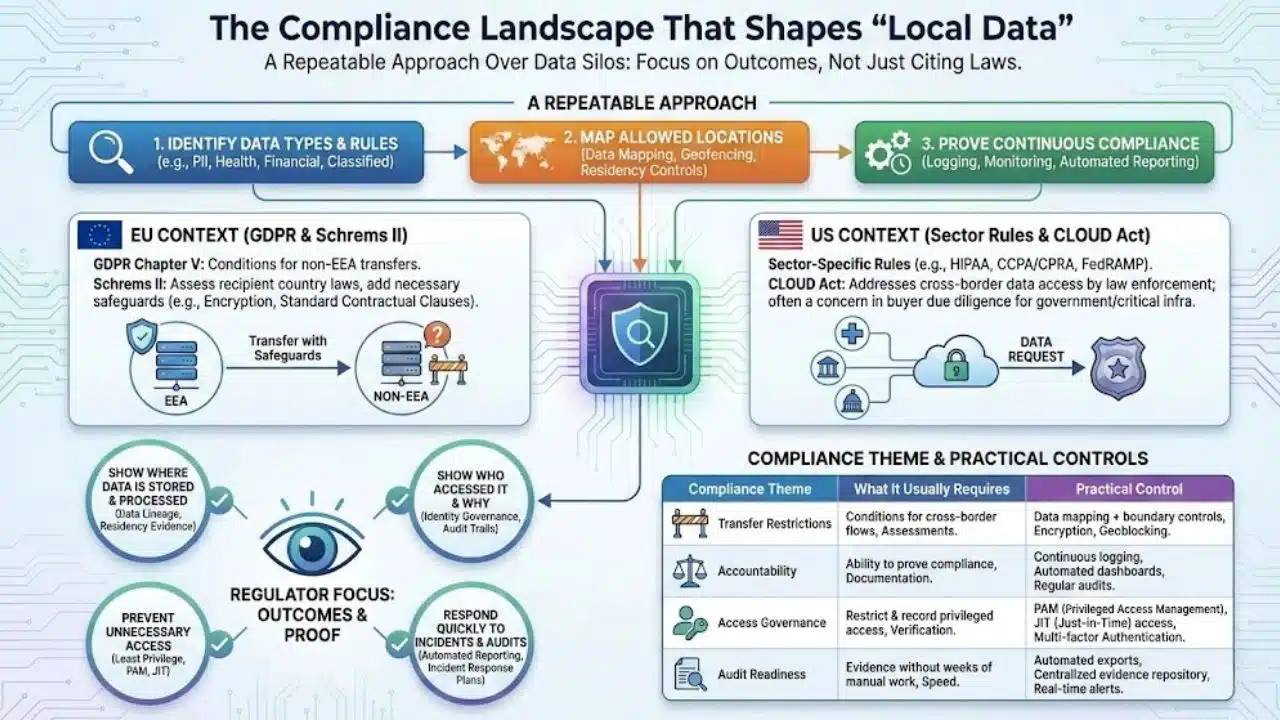
The Compliance Landscape That Shapes “Local Data”
You do not need to cite every law in every country to build a strong program. You do need a repeatable approach:
-
Identify which data types fall under strict rules
-
Map which locations are allowed for each data type
-
Decide how you will prove compliance continuously
In the EU context, GDPR’s Chapter V sets conditions for transferring personal data outside the EEA. Schrems II made it clear that organizations must assess whether the recipient country’s laws undermine protections and add safeguards when needed.
In the US context, sector rules vary, and government access concerns often show up in procurement requirements. The CLOUD Act is often discussed in buyer due diligence, especially for government and critical infrastructure.
Across regions, regulators tend to focus on outcomes:
-
Can you show where data is stored and processed
-
Can you show who accessed it and why
-
Can you prevent unnecessary access, including privileged access
-
Can you respond quickly to incidents and audits
| Compliance Theme | What It Usually Requires | Practical Control |
|---|---|---|
| Transfer restrictions | Conditions for cross-border flows | Data mapping + boundary controls |
| Accountability | Ability to prove compliance | Continuous logging and reporting |
| Access governance | Restrict and record privileged access | PAM, JIT access, approvals |
| Audit readiness | Evidence without weeks of manual work | Automated dashboards and exports |
How Data Quietly Leaves “Local” Clouds
Most teams focus on primary data storage. In practice, data leaks through side channels.
Common pathways:
-
Backups and snapshots that replicate to other regions
-
Logs, metrics, traces, and crash dumps routed to global systems
-
Support bundles uploaded for troubleshooting
-
Third-party tools for analytics, chat, email, and payments
-
Edge caching and CDN behavior
-
AI features that send prompts or content to external services
Also, cloud platforms split systems into:
-
Data plane, where your data is stored and processed
-
Control plane, where management actions happen
A provider may keep customer content local while parts of the control plane remain global. That can still be acceptable, but you must understand it and document it.
| Data Flow | Why It Matters | What To Lock Down |
|---|---|---|
| Backups | Replication breaks residency | Disable cross-region replication by policy |
| Logs and telemetry | Often overlooked and sensitive | Local SIEM, redaction, local endpoints |
| Support access | Humans can become the weak link | Scoped access, approvals, recording |
| Control plane | Management metadata may travel | Ask for boundary details by service |
Technical Strategies To Keep Data Local
This is the part most teams can act on immediately. You can do a lot without buying a special sovereign cloud product.
Classify Data And Split Workloads
Start with a simple model:
-
Public: marketing pages, published docs
-
Internal: standard business data
-
Confidential: customer info, employee records
-
Regulated: health, banking, government records
-
Highly sensitive: identity systems, secrets, security logs
Then split workloads:
-
Keep regulated and highly sensitive workloads inside the strict boundary
-
Allow less sensitive workloads more flexibility for cost and performance
Enforce Residency For Storage And Databases
Use region allow-lists. Block creation of storage outside the allowed region. Treat backups as data too.
Keep Processing Local, Not Just Storage
Data can sit locally but get processed elsewhere through managed services. Confirm where compute runs for:
-
Search indexing
-
ETL jobs
-
Data lakes and warehouses
-
AI inference and training features
Control Encryption Keys
Key control is central to sovereignty discussions. Many providers offer customer-managed keys and options that keep keys under customer control or external control. Provider details differ, so validate service by service.
Use Confidential Computing For Sensitive Workloads
Confidential computing protects data “in use” via hardware-based trusted execution environments. This reduces exposure while data is processed. It does not replace all other controls, but it can strengthen the technical layer.
Make Observability Local
Treat logs as sensitive. They can include IDs, tokens, and request details. Keep them inside the boundary when possible.
Practical checklist:
-
Local log storage and retention
-
Redaction for PII and secrets
-
Separate access roles for logs
-
Local alerting and incident workflows
| Strategy | What It Protects | Quick Win |
|---|---|---|
| Data classification | Scope and cost | Tag datasets and apps by sensitivity |
| Region guardrails | Residency drift | Infrastructure policy that blocks wrong regions |
| Key ownership | Access and lawful request risk | Customer-managed keys where possible |
| Confidential computing | Data in use | Use for highest-risk processing |
| Local observability | Hidden leakage | Keep logs and telemetry local |
Architecture Patterns For Sovereign Setups
Single-Jurisdiction Public Cloud Region
This works when you can enforce strict region controls and manage keys well. It is often the fastest path.
Multi-Zone High Availability Inside One Country
This improves resilience without crossing borders. Make sure failover and DR tests do not trigger cross-border replication.
Provider Sovereign Offerings
Large providers now offer more explicit sovereign approaches, often with claims about independent EU operations, local governance, and limited dependencies. AWS, for example, has described plans and governance structures for its European Sovereign Cloud, including EU-based operations and separation from non-EU dependencies.
Other providers position “data boundary” and sovereign controls as a way to keep core customer data within chosen regions. Microsoft describes an EU Data Boundary for certain enterprise services, with defined scope and documented exceptions. Google describes sovereign cloud controls and boundary features, including residency and access controls.
Hybrid Sovereign
Some organizations keep the strictest data on local infrastructure or local providers, then integrate with public cloud for less sensitive services.
| Pattern | Best For | Main Tradeoff |
|---|---|---|
| Single-region public cloud | Speed with residency | Must manage hidden flows carefully |
| Multi-zone in-country | High availability | More complexity, higher cost |
| Sovereign offerings | Regulated procurement needs | Limited regions, evolving features |
| Hybrid | Strict localization | Integration and operating overhead |
Governance That Keeps Sovereignty True Over Time
Sovereignty fails when it becomes a one-time project. Teams change. Vendors add services. New integrations appear. A good program uses guardrails and routine reviews.
What works in practice:
-
Policy as code to enforce allowed regions and services
-
Regular data flow reviews for new features and vendors
-
Standard templates for risk assessments and transfer decisions
-
Clear ownership, not “shared ownership by everyone”
You also need shared responsibility clarity. Cloud security and compliance depend on who does what, and major providers and government agencies publish shared responsibility models.
| Governance Control | Why It Matters | Evidence To Keep |
|---|---|---|
| Policy as code | Prevents mistakes | Policy rules and enforcement logs |
| Data flow reviews | Stops hidden transfers | DPIAs, vendor assessments |
| Shared responsibility clarity | Avoids gaps | RACI chart and control mapping |
| Regular audits | Proves ongoing control | Audit packs, change records |
A Buyer Checklist To Validate “Sovereign Cloud” Claims
Marketing language is easy. Enforceable commitments are harder. When evaluating a provider or a “sovereign” offering, ask questions that map to legal, operational, and technical control.
Key questions to ask:
-
Can you guarantee storage and processing residency for the services we use
-
Where does the control plane run, and where is metadata stored
-
Who can access our data for support, and where are they located
-
How do you log and audit administrative access
-
Can we control encryption keys, and can the provider be technically blocked from using them
-
Which sub-processors handle data, and where are they located
-
What telemetry leaves the boundary, if any
-
How do backups, DR, and failover behave under real outages
-
What audit reports and evidence can you provide, and how fast
-
What is the exit plan, including deletion verification
Sovereignty is also tied to broader digital sovereignty initiatives. In Europe, Gaia-X is one example of an effort aimed at trusted, interoperable data infrastructure and digital sovereignty principles.
| Checklist Area | What To Ask For | Red Flag |
|---|---|---|
| Residency scope | Service-by-service proof | “Most services” language without specifics |
| Admin access | Logs, approvals, location | No clarity on support access |
| Key control | Customer-managed keys options | Provider retains broad key access |
| Sub-processors | Full list and locations | Hidden vendor chain |
| Exit plan | Export and verified deletion | No deletion proof process |
Cost, Performance, And Product Tradeoffs
You can keep data local and still be practical. But you should expect tradeoffs.
Common impacts:
-
Fewer services in smaller regions
-
Higher costs for local-only redundancy
-
Longer lead times for regulated procurement
-
More work for monitoring and evidence gathering
A balanced approach often works best:
-
Keep regulated and high-risk datasets local with strict controls
-
Keep low-risk services global when allowed and beneficial
-
Document why each workload sits where it does
Cloud adoption continues to grow, and large forecasts highlight how central cloud has become to IT spending. That makes these tradeoffs more relevant, not less.
| Tradeoff | What You Gain | What You Give Up |
|---|---|---|
| Local-only boundary | Stronger compliance posture | Less global flexibility |
| Sovereign offerings | Clearer assurances for regulators | Possible feature limits |
| Hybrid approach | Strict control for sensitive data | Higher operational complexity |
Real-World Scenarios That Make This Concrete
Government Digital Services
Citizen identity data often needs strict residency, strict access controls, and local incident response. Public website content can remain global for performance.
Banking And Payments
Banks may keep transaction records and customer identifiers local. They might still run anonymized analytics if rules allow, but they must prove separation and controls.
Healthcare
Patient data stays local, including backups and logs. Research data may use pseudonymization, but the organization still needs governance to avoid re-identification risk.
SaaS Companies Selling Into Regulated Buyers
A common pattern is a “regional tenant” model where each customer’s data stays inside a chosen boundary. Deals often depend on clear answers about support access, keys, and audit reports.
| Scenario | What Must Stay Local | Common Pitfall |
|---|---|---|
| Government | Identity, records, audit logs | Support access from outside boundary |
| Banking | Transactions, KYC data | Replication to global analytics |
| Healthcare | Patient data, backups, logs | Logs leaking PII |
| SaaS | Tenant data + metadata | Third-party tools breaking residency |
The Future Of Cloud Sovereignty
Expect more boundary and sovereign options, especially in Europe. Providers are already investing in sovereign approaches and describing governance structures that aim to meet evolving sovereignty demands.
Expect more focus on:
-
Local operations and transparency
-
Audit automation and faster evidence
-
Controls for AI workloads and sensitive processing
-
Confidential computing as a stronger baseline for high-risk use cases
The bigger change is cultural. Buyers increasingly treat data location and operational control as core requirements, not optional preferences.
| Trend | What It Means | What To Prepare |
|---|---|---|
| Sovereign offerings growth | More provider options | Better vendor due diligence |
| Audit automation | Faster regulator response | Build evidence pipelines |
| AI sovereignty | Local processing expectations | Map AI data flows early |
Final Thoughts
Cloud sovereignty works when you treat it as a system, not a slogan. Start with data classification. Lock down regions for sensitive workloads. Keep backups and logs inside the boundary. Control encryption keys where you can. Document operational access and support processes. Then build an evidence pipeline that makes audits predictable.
You do not need to make every workload local. You do need a clear, defensible model that matches your risk and regulatory needs. When you do that well, cloud sovereignty becomes a business advantage. It helps you win trust, reduce surprise legal exposure, and move faster with less fear.