A cyberattack is a malicious endeavor to obtain unauthorized access to a computer, computing system, or computer network. Cyberattacks seek to disable, disrupt, demolish, or take control of computer systems, as well as modify, obstruct, delete, manipulate, or steal the data stored within these systems.
What is Cyberattack?
A cyberattack is a malicious endeavor to obtain unauthorized access to a computer, computing system, or computer network. Cyberattacks seek to disable, disrupt, demolish, or take control of computer systems, as well as modify, obstruct, delete, manipulate, or steal the data stored within these systems.
Cyberattacks can be launched from any location by individuals or organizations employing one or more diverse attack strategies. Cyberattacks frequently occur in stages, beginning with hackers surveying or scouring for vulnerabilities or access points, followed by the initial compromise, and then the complete attack, which may consist of stealing valuable data, disabling computer systems, or both.
There are many types of cyber-attacks, including but not limited to:
- Malware attacks
- Denial-of-service (DoS) and distributed denial-of-service (DDoS) attacks
- Phishing attacks
- Ransomware attacks
- Man-in-the-middle (MitM) attacks
- Password attacks
- SQL injection attacks
- Cross-site scripting (XSS) attacks
- Zero-day exploits
- Advanced persistent threats (APTs)
Cyberattacks can have major consequences, including financial losses, reputational harm, legal liabilities, and regulatory penalties. Cyberattacks can result in the loss of sensitive data, such as personal information, intellectual property, and trade secrets, which can have long-term repercussions for both individuals and businesses. It is essential to use a combination of skilled security professionals, processes, and technology to prevent cyber-attacks. Reducing risk involves three broad categories of defensive action: preventing attempted attacks from actually accessing the organization’s IT systems, detecting attacks that have penetrated the defenses, and responding to successful attacks that have penetrated the defenses.
What Does Cyberattack Do?
A cyberattack is a deliberate attempt to gain unauthorized access to a computer, computing system, or computer network with the goal of causing damage, disrupting operations, stealing sensitive data, or controlling the targeted system. Cyberattacks can have a variety of goals, and they can have serious consequences for individuals and organizations.
Objectives of cyberattacks are outlined below:
- Data Breaches: One of the main objectives of a cyberattack is to gain access to sensitive or confidential information, such as personal data, financial records, or intellectual property. Cybercriminals can sell this information on the dark web or use it for identity theft, fraud, or other malicious purposes.
- System Disruptions: Cyberattacks can aim to disrupt the normal functioning of computer systems or networks. This can be achieved through methods like denial-of-service (DoS) attacks or ransomware attacks, where systems are overwhelmed or locked down, rendering them temporarily or permanently unavailable.
- Financial Gain: Some cyberattacks are motivated by financial gain. For example, attackers may attempt to steal funds from bank accounts, conduct fraudulent transactions, or extort money through ransomware attacks. These attacks can result in significant financial losses for individuals and organizations.
- Espionage and Surveillance: Nation-states or advanced persistent threats (APTs) may conduct cyber attacks to gain access to sensitive information for espionage purposes. Such attacks can target government agencies, military organizations, or private companies involved in critical infrastructure.
Consequences of Cyber Attacks are as follows:
- Data Loss and Exposure: A successful cyberattack can result in the loss, theft, or exposure of sensitive data. This can lead to identity theft, privacy violations, financial losses, reputational damage, and legal consequences.
- Financial Losses: Organizations may incur financial losses due to the theft of funds, fraudulent transactions, operational disruptions, or the costs associated with remediation and recovery. Lost productivity, reputational damage, and legal liabilities can further impact the financial standing of affected entities.
- Operational Disruptions: Cyber attacks can disrupt the normal operations of organizations, causing downtime, delays, or service interruptions. This can have a significant impact on productivity, customer trust, and business continuity.
- Damage to Reputation: When organizations suffer a cyberattack, their reputation can be severely damaged. Customers may lose trust in the organization’s ability to protect their data, resulting in a loss of business and a long-term negative impact on the brand’s image.
- Legal and Compliance Consequences: Depending on the nature of the attack and the data involved, organizations may face legal and regulatory consequences.
How Does Cyber Attack Work?
To exploit vulnerabilities and gain unauthorized access to systems or sensitive data, cyber-attacks employ a variety of techniques and methodologies. A typical cyber attack methodology is described in detail below:
- Reconnaissance: Attackers gather information about the target system or organization. This can involve scanning for open ports, identifying potential weaknesses, and profiling potential targets.
- Exploitation: Once vulnerabilities are identified, attackers exploit them using various techniques. This may include exploiting software vulnerabilities, leveraging social engineering techniques, or utilizing phishing emails to trick users into opening malicious attachments or visiting compromised websites.
- Initial Access: After successfully exploiting a vulnerability, attackers gain initial access to the target system. This could involve gaining unauthorized user privileges, creating backdoors, or installing malware on the system.
- Lateral Movement: Once inside the system, attackers try to move laterally and gain access to other systems or accounts within the network. They may exploit weak password security, misuse legitimate credentials, or use advanced techniques like pass-the-hash attacks to escalate their privileges and move laterally undetected.
- Persistence: Attackers aim to maintain access to the compromised system for as long as possible. They may install rootkits, backdoors, or other malicious software to maintain persistence, ensuring that they can return to the system even if initial access is discovered and mitigated.
- Privilege Escalation: If the attacker does not already have sufficient privileges, they may escalate their privileges to gain control over critical systems or data. This can involve exploiting vulnerabilities in system configurations, hijacking privileged accounts, or leveraging weaknesses in access control mechanisms.
- Data Exfiltration: Once the attacker has control over the compromised system and has escalated privileges, they may attempt to exfiltrate sensitive data. This can involve copying or stealing data, encrypting it for ransom purposes, or using covert channels to exfiltrate data undetected.
- Covering Tracks: To avoid detection and hide their activities, attackers often attempt to cover their tracks by deleting logs, obfuscating their presence, or misdirecting investigators. They may also plant false evidence or alter timestamps to mislead forensic analysis.
What is a cyberattack, and what does it mean in the digital world?
A cyber-attack is an attempt to gain unauthorized access to a computer system or network. Cyber-attacks can be carried out for a variety of reasons, including data theft, business disruption, or damage.
Because of our increased reliance on technology, cyber-attacks have become more sophisticated and diverse, constantly evolving to circumvent security measures. New attack vectors are constantly being developed, and existing attacks are becoming more sophisticated. It is difficult for businesses and individuals to stay ahead of the curve as a result of this.
Cyber-attacks can have far-reaching consequences, ranging from financial losses, reputational damage, and legal ramifications to jeopardizing personal privacy and national security. Understanding and mitigating cyber threats through robust cybersecurity measures has become critical to safeguarding the integrity, confidentiality, and availability of critical information and systems as the digital realm expands.
What are the essential cybersecurity measures individuals and organizations should implement?
The following is a list of essential cybersecurity measures that all organizations and individuals should implement in order to protect themselves from cyberattacks:
- Implement cybersecurity best practices: Individuals and companies should follow recommended cybersecurity practices such as using strong passwords, upgrading software, thinking twice before clicking on suspicious links, and enabling multi-factor authentication.
- Train employees on cybersecurity best practices: The most critical cybersecurity measure that every firm should implement is cybersecurity best practices training. Employees that are properly trained will comprehend the importance of cybersecurity.
- Regularly assess cybersecurity risks: Regular cybersecurity risk assessment assists in evaluating threats, determining if existing security measures are enough, and making mid-course changes to safeguard the firm from cyber-attacks.
- Develop and implement a cybersecurity policy: A cybersecurity policy acts as a written framework for all cybersecurity measures implemented in your organization. Consider developing a hierarchical cybersecurity strategy that includes a centralized policy as well as supplemental regulations tailored to each department inside your firm.
- Simplify your technology infrastructure: Having a big number of technologies deployed and maintained is not necessarily the optimal strategy for cybersecurity. Simplifying your IT infrastructure can assist in reducing the attack surface and making it easier to administer.
- Inventory your data, equipment, and processes: To identify possible vulnerabilities and risks, organizations should inventory their data, equipment, and procedures.
- Perform regular risk assessments: Regular risk assessments assist companies in identifying possible vulnerabilities and dangers and enable them to take proactive actions to reduce them.
- Develop a cybersecurity governance and risk management program: A cybersecurity governance and risk management program suited for the organization’s size should be designed. The owners and directors must see cybersecurity risk as a substantial business risk.
- Protect your network: Network security is critical to ensuring the network’s integrity and usefulness. You can use next-generation firewall to protect your network from malicious traffic. Zenarmor NGFW is a next-generation firewall (NGFW) that provides comprehensive protection for your network. It offers a wide range of features.
Experience advanced cybersecurity with Zenarmor, your ultimate Next-Generation Firewall (NGFW). With real-time threat intelligence, automatic botnet detection, and phishing server filtering, Zenarmor guards your network against evolving threats.
Unleash deep visibility and control through detailed reporting, application insights, and user-based filtering. Cloud central management ensures scalability and ease of control, while adaptive access control and high availability configurations strengthen your defenses.
Choose Zenarmor for proactive security, comprehensive visibility, and adaptable control in one powerful NGFW package.
You can freely use Zenarmor to protect your network at the enterprise level.
Frequent software updates are required to guard against known vulnerabilities and attacks.
Individuals and organizations can better defend themselves against cyberattacks and reduce potential risks and vulnerabilities if they put these cybersecurity measures into action and implement them.
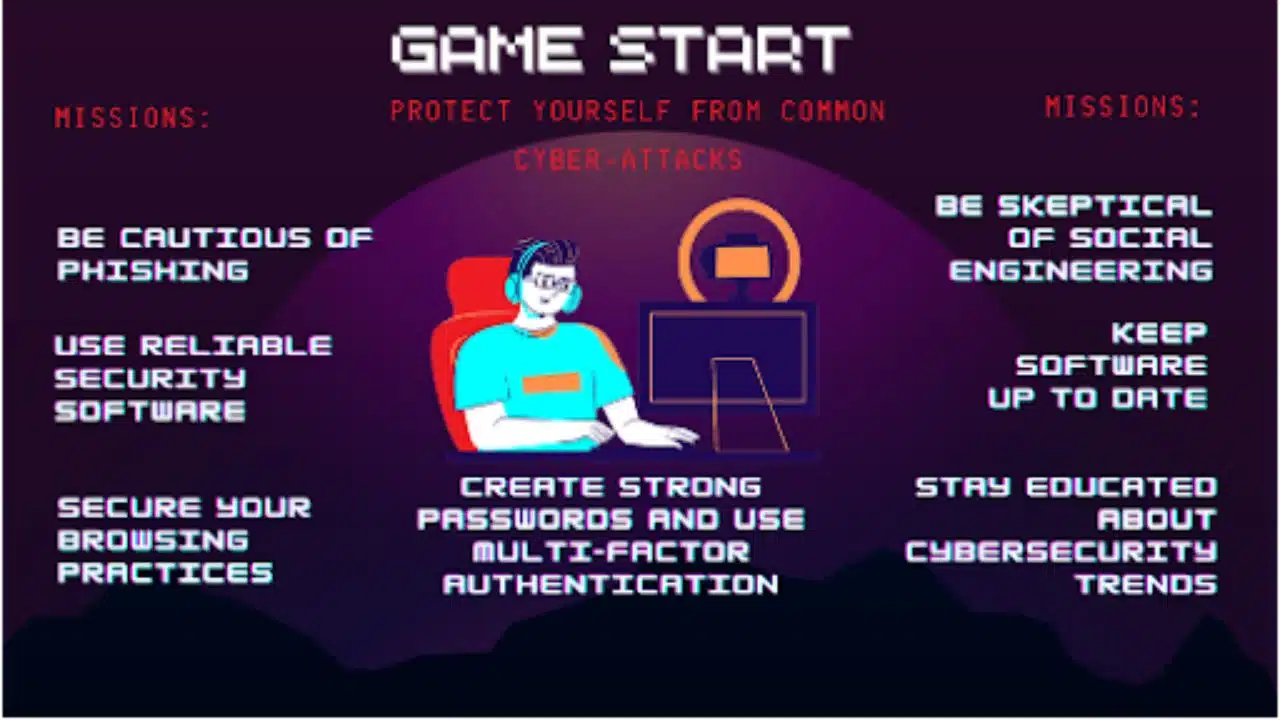
How can users protect themselves from common cyber-attacks?
Attacks in cyberspace are happening more frequently, which is why users need to take preventative measures to safeguard themselves. Users can protect themselves from the most common types of cyberattacks by following these helpful and actionable recommendations:
- Be aware of phishing scams: Phishing scams are one of the most common methods of attack you’re likely to come across. Be cautious of emails or messages that ask for personal information or contain suspicious links. Avoid clicking on links or downloading attachments from unknown sources.
- Use reputable security software: Consider purchasing antivirus software to help monitor your email box and protect against malware. Keep your security software up to date to ensure it is effective against the latest threats.
- Secure browsing habits: Use secure browsing habits, such as checking for the padlock icon in the address bar, using HTTPS, and avoiding public Wi-Fi networks.
- Use strong passwords: Use strong and unique passwords for each account and enable multi-factor authentication where possible. Avoid using easily guessable passwords such as “password123” or “123456”.
- Keep software up to date: Regularly updating software is essential to protect against known vulnerabilities and exploits. Enable automatic updates where possible.
- Be cautious of social engineering tactics: Be wary of social engineering tactics, such as phone calls or messages from unknown sources asking for personal information or login credentials.
- Educate yourself: Stay informed about the latest cyber-attack trends and tactics. Attend cybersecurity training sessions and read up on best practices for cybersecurity.
Users can protect themselves from common cyber-attacks by being aware of phishing scams, using reputable security software, adopting secure browsing habits, using strong passwords, keeping software up to date, being cautious of social engineering tactics, and educating themselves about cybersecurity best practices.