Web3 is revolutionizing the internet, bringing decentralized applications, blockchain technology, and smart contracts to the forefront of digital innovation. While it promises enhanced security, transparency, and user empowerment, Web3 is not without risks.
In fact, the biggest security challenges in Web3 are among the biggest obstacles preventing mass adoption.
From smart contract vulnerabilities to private key mismanagement, Web3 security threats expose users, developers, and investors to potential financial loss and data breaches.
Addressing these risks requires a proactive approach, combining cutting-edge security practices, user education, and regulatory compliance.
In this article, we explore the biggest security challenges in Web3 and provide effective solutions to mitigate them, ensuring a safer decentralized future.
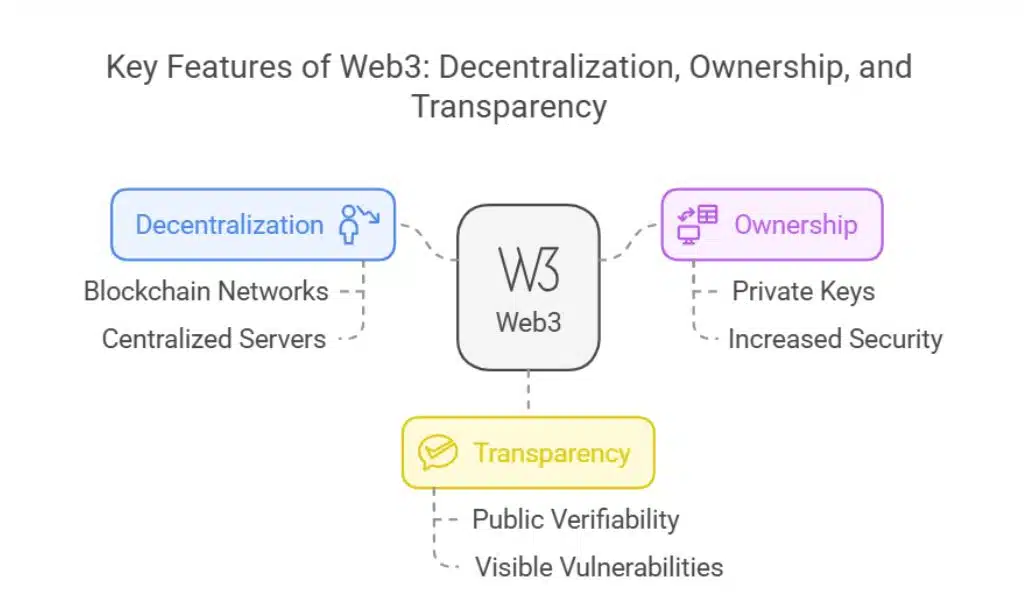
What Makes Web3 Different from Traditional Web Security?
Web3 differs significantly from traditional web systems in the following ways:
- Decentralization: Unlike Web2, which relies on centralized servers, Web3 applications run on blockchain networks, reducing single points of failure.
- Ownership: Users control their own data and assets through private keys, increasing security but also responsibility.
- Transparency: Transactions and smart contracts are publicly verifiable, but vulnerabilities are also visible to malicious actors.
While these features improve security in some areas, they also introduce new risks that traditional cybersecurity models do not fully address.
The 5 Biggest Security Challenges in Web3 and Their Solutions
Web3, while innovative and decentralized, introduces several critical security challenges that users, developers, and enterprises must navigate carefully. The biggest security challenges in Web3 can lead to financial losses, data breaches, and operational failures if not properly mitigated.
Addressing these security threats is essential to fostering trust and adoption in the decentralized ecosystem.
Below, we outline the most pressing security concerns and effective strategies to resolve them.
1. Smart Contract Vulnerabilities
Smart contracts are self-executing agreements coded into blockchain networks. Once deployed, they cannot be altered, making security flaws permanent. Bugs and loopholes in smart contracts can be exploited, leading to substantial financial losses.
Hackers continuously look for weaknesses in smart contracts, and even minor coding errors can result in millions of dollars being drained from decentralized applications (dApps) and DeFi platforms.
Examples of Smart Contract Exploits
- The DAO Hack (2016): An attacker exploited a recursive withdrawal bug, draining $60 million in Ether.
- Poly Network Hack (2021): A vulnerability allowed a hacker to steal over $600 million in assets.
- Nomad Bridge Attack (2022): A bug in the smart contract logic led to a $190 million exploit.
How to Solve It
| Solution | Description |
| Implement rigorous audits | Engage third-party security firms for comprehensive smart contract audits before deployment. |
| Use formal verification | Mathematical proofs can validate the contract’s logic and prevent errors. |
| Adopt upgradable smart contracts | Use proxy contracts that allow bug fixes without affecting user funds. |
| Run bug bounty programs | Encourage ethical hackers to identify and report vulnerabilities before malicious actors exploit them. |
2. Private Key Management Risks
Web3 eliminates centralized credential storage, making private keys the sole access point to assets. Losing or exposing private keys leads to irreversible asset loss.
Without proper key management, users risk losing their digital assets permanently, whether through hacks, accidental deletion, or phishing attacks.
Many users struggle with secure key storage, making this one of the most significant challenges in Web3 security.
Common Pitfalls
- Phishing attacks: Fake wallet apps or malicious links trick users into sharing private keys.
- Weak seed phrases: Short or easy-to-guess recovery phrases increase hacking risks.
- Poor storage: Keeping private keys in cloud storage or on compromised devices leads to breaches.
How to Solve It
| Solution | Description |
| Use multi-signature wallets | Require multiple approvals for transactions, reducing single points of failure. |
| Adopt hardware wallets | Secure assets offline in devices like Ledger or Trezor. |
| Implement social recovery | Use trusted guardians to help restore access without exposing private keys. |
| Educate users | Promote best practices for private key storage and phishing awareness. |
3. Sybil Attacks and Identity Fraud
Web3 lacks a standardized identity system, enabling attackers to create multiple fake accounts and manipulate decentralized networks.
Sybil attacks occur when a malicious actor floods a network with fake identities to gain disproportionate influence, often compromising governance, consensus, or token distributions.
Real-World Examples
- Fake validator nodes: Attackers use multiple identities to control voting mechanisms.
- Bot attacks in DeFi projects: Fake accounts manipulate token distributions and governance decisions.
- NFT fraud: Multiple fake wallets are used to artificially inflate NFT prices.
How to Solve It
| Solution | Description |
| Use Decentralized Identity (DID) solutions | Blockchain-based identity verification can authenticate users without central authorities. |
| Leverage Proof-of-Personhood (PoP) | Biometric or unique identity verifications prevent fake accounts. |
| Implement reputation-based models | Systems like soulbound tokens can track a user’s trustworthiness over time. |
4. Exploits in Cross-Chain Bridges
Cross-chain bridges enable token transfers between different blockchain networks but are highly vulnerable to exploits. These bridges often rely on a single smart contract or a centralized validator, making them an attractive target for hackers.
If compromised, a single attack can result in multi-chain asset loss.
Major Incidents
- Wormhole Hack (2022): A hacker exploited a vulnerability, stealing $325 million.
- Ronin Bridge Hack (2022): Attackers drained over $600 million from Axie Infinity’s bridge.
- Harmony Horizon Hack (2022): Hackers exploited weak multi-signature security, stealing $100 million.
How to Solve It
| Solution | Description |
| Adopt multi-layer security | Implement multi-signature mechanisms and time-locked transactions. |
| Use audited bridge protocols | Choose trusted, third-party-audited bridging solutions. |
| Implement liquidity insurance | Encourage bridge operators to provide financial protection against potential hacks. |
5. Regulatory and Compliance Challenges
The regulatory landscape for Web3 is evolving, leading to uncertainty and potential legal risks for users and developers.
As governments worldwide attempt to regulate decentralized applications, compliance remains a critical concern. Without proper guidance, businesses and users could face legal consequences.
How to Solve It
| Solution | Description |
| Implement decentralized compliance solutions | Smart contracts can automate KYC/AML processes without exposing user data. |
| Stay updated on regulations | Web3 developers must monitor global regulatory trends to ensure compliance. |
| Engage with policymakers | Collaboration with governments can help create balanced regulations that support innovation. |
Takeaways
By understanding and addressing the biggest security challenges in Web3, users, developers, and investors can mitigate risks and enhance blockchain adoption.
Implementing security best practices such as regular audits, secure key management, and decentralized identity solutions can help build a more resilient Web3 ecosystem.
Additionally, staying up to date with regulatory changes and technological advancements ensures that businesses and individuals can adapt to emerging threats effectively.
Security in Web3 is a collective effort, requiring ongoing education, collaboration, and innovation to foster a safer decentralized environment.
Stay informed, adopt best practices, and leverage cutting-edge technologies to protect yourself in this evolving digital landscape.