Have you ever faced the challenge of managing an IoT device from afar, knowing that any misstep could compromise its security? Whether updating configurations or troubleshooting, remote access can feel like walking a tightrope without a safety net. Imagine if there was a way to navigate this wire with confidence.
Secure Shell (SSH) is your virtual safety harness in the world of IoT management. It’s not just about connecting remotely; it’s about creating a secure corridor for your data and commands to travel through, guarded against prying eyes and malicious intents.
In this article, we’ll explore SSH Control IoT Devices and how SSH provides peace of mind when controlling IoT devices across networks. You’ll learn how to establish trustworthy connections using SSH and why it’s pivotal for keeping your IoT infrastructure not only functional but also secure.
Let’s embark on this digital journey together, because mastering SSH means taking control without compromising security. Are you ready to secure your IoT universe? Keep reading.
Content Highlights
- SSH lets you connect to IoT devices safely over the internet. It encrypts data so no one else can see it.
- SSH is important for controlling IoT devices from anywhere. It keeps the connection secure.
- To use SSH, you need the IP address of the IoT device. You also need the username and password or a special SSH key.
- SSH lets you send commands to IoT devices to check on them or change settings remotely.
- To keep SSH secure, use strong passwords and update devices regularly. Also, monitor logs and restrict user access.
Understanding SSH and IoT
[Video Credit: @PenguinDigital]
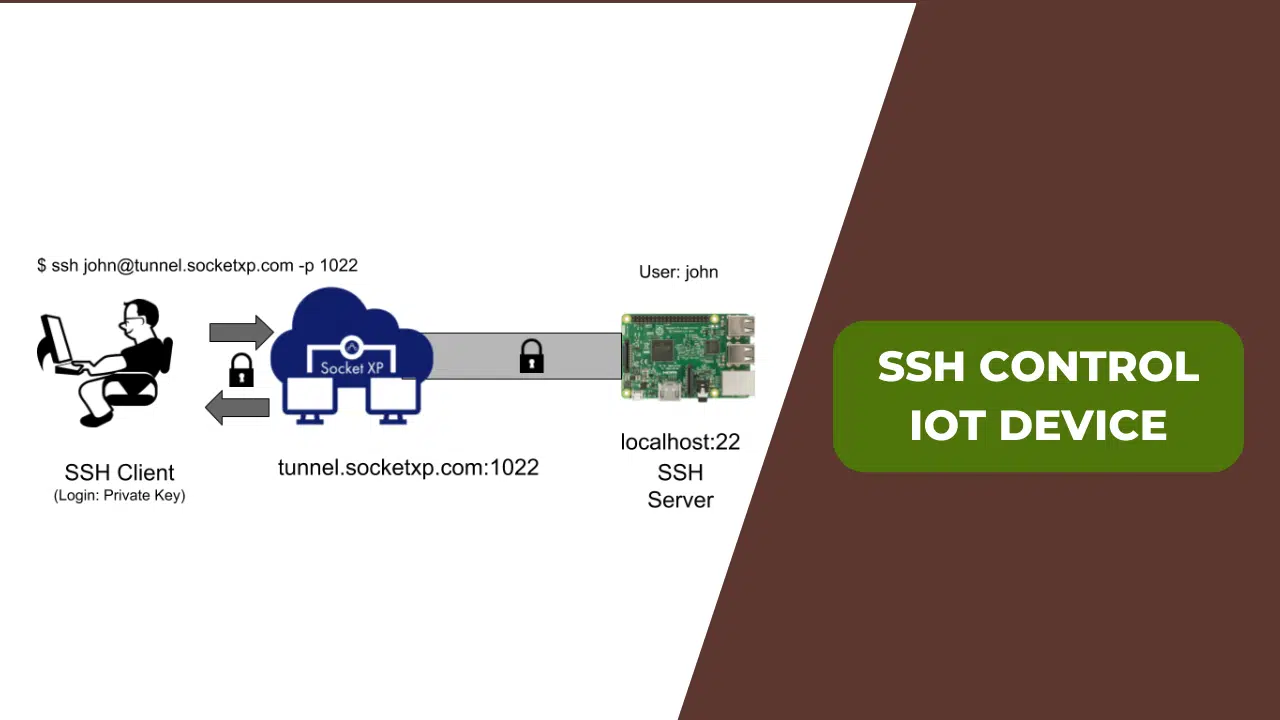
Before we discuss SSH Control IoT devices, first we’ll talk about SSH and IoT. SSH, or Secure Shell, is a protocol that provides a secure way to access and control devices and Control IoT Devices remotely over a network. In the context of IoT, SSH plays a crucial role in allowing users to securely connect to and manage their IoT devices from anywhere in the world.
Understanding how SSH works with IoT devices is essential for ensuring efficient and secure device management.
Definition of SSH
Secure Shell, or SSH, is like a secret path for computers to talk over the internet. It lets one computer connect to another in a way that’s safe from outsiders. When you use SSH, it’s as if you have a special key that only fits your lock nobody else can peek into what you’re doing.
This is important when dealing with Internet of Things (IoT) devices like cameras and smart thermostats because it keeps the information they send and receives private.
Think of it this way, if IoT devices were houses, SSH would be their alarm systems. Just as an alarm protects a home from intruders, SSH keeps IoT gadgets safe from snoops and hackers trying to get in where they shouldn’t be.
With SSH, everything sent between these gadgets is scrabbled up, so no one else can read it unless they have the secret code or ‘key’. This means personal details stay just that personal.
It wraps up data in strong encryption before sending it out on the big internet journey. That’s why people who care about keeping things away from prying eyes use SSH for their IoT stuff just like you wouldn’t leave your front door open when you go out, using SSH makes sure your digital doors are locked tight too!
Importance of SSH in the IoT
SSH stands for Secure Shell. It’s like a special door that only lets in people with the right key. This matters a lot for IoT, which means the Internet of Things. IoT is all about things like cameras, fridges, and lights that can talk to the internet.
IoT devices are smart, but they need to be safe too. SSH helps keep them safe when people want to check on them from far away. Imagine you have a smart light at home and you’re on vacation. With SSH, you can turn it off without worrying about bad guys getting into your network.
SSH makes sure no one can sneak a peek at what you’re doing with your IoT stuff. It scrambles up messages so only the right device can understand them. That way, everything stays private and secret.
Businesses like using SSH for their IoT gadgets because it saves time and money. They don’t have to go to each device by hand, they just log in from anywhere safely using keys made just for them.
Using SSH also helps fix problems faster since technicians do not need to travel onsite every time something needs checking or updating like adding new features or fixing bugs in the system software (firmware updates).
Plus, if something goes wrong with an IoT device, SSH lets someone trusted get root access quickly so they can sort it out before anything big happens. Additionally, you can also read AI Chatbots and IoT.
The Role of SSH Control IoT Device
SSH plays a crucial role in controlling IoT devices by providing secure access to these devices. It allows users to establish a secure connection and remotely manage their IoT devices, enabling seamless control and monitoring from anywhere with an internet connection.
Accessing IoT Devices with SSH
Accessing IoT devices with SSH means you can manage them from anywhere. This uses a secure path, so your data stays safe.
- First, make sure the IoT device is on and connected to the internet.
- On your computer, open an SSH client. This program lets you talk to an IoT device.
- You need the IoT device’s IP address. It’s like its home address on the internet.
- Type in the username for the IoT device. It tells the device who you are.
- Now, enter your password or use an SSH key. This key is a special code that only you have.
- If everything matches, you’ll connect to the IoT device. You see a screen where you can type commands.
- Start sending commands to tell the IoT device what to do.
- You can check if things are working fine or change settings.
- When done, type ‘exit’ to safely disconnect from your IoT device.
- Always keep your passwords and keys secret. And change them sometimes for more safety.
Establishing an SSH Connection with an IoT Device
Setting up an SSH connection to an IoT device lets you control it from far away. This is a safe way to reach your device and send commands.
- First, make sure your IoT device is on and connected to the internet.
- Your computer needs an SSH client program like Putty for Windows or the terminal in macOS and Linux.
- Find out the IoT device’s IP address. You may need to check your router or use a scanning tool.
- Open your SSH client and type in the IP address of the IoT device.
- Choose the right port number, usually 22, unless changed for safety.
- Click ‘connect’ or enter [username]@[IP address]’ in the terminal.
- When asked, type in the password for your IoT device’s user account.
- If this is your first time connecting, you might see a security message asking if you trust this connection. Say ‘yes’ to keep going.
- After logging in, you can type commands to tell your IoT device what to do.
- Always keep passwords hard to guess and store them safely.
- Use SSH keys instead of passwords for better safety if you can.
- Keep updating your devices with new security patches.
Importance of IoT Remote Access
IoT remote access allows for the monitoring and control of IoT devices from anywhere, providing flexibility and convenience. It enables real-time management, troubleshooting, and updates without the need for physical presence, leading to increased efficiency and cost savings.
Benefits of Remote Access to IoT Devices
Remote access to IoT devices offers numerous advantages, ensuring efficient management and enhanced security.
- Scalability: Remote access allows for the seamless expansion of IoT networks, enabling the management of diverse applications such as utility usage, automation, and supply chain inventories.
- Security Monitoring: Administrators can effectively monitor and address unauthorized activities in real time, preventing potential damage and disruptions in operational technology.
- Firmware Updates: Scheduled remote firmware updates help in mitigating operational issues stemming from outdated software and applications, ensuring smooth functionality.
- Data Confidentiality: The use of the SSH protocol ensures data confidentiality and security for IoT networks, safeguarding sensitive information from unauthorized access.
- Multi-Layered Security: Remote access provides layers of added security such as user-generated credentials, multi-factor authentication, and zero-trust keyless solutions, enhancing overall device security.
- Proactive Management: Effective management, disposal, and regeneration of SSH keys are crucial in maintaining secure remote access for IoT devices while proactively addressing potential vulnerabilities.
Keeping IoT Remote Access Secure with SSH
When it comes to ensuring the security of remote access to IoT devices, Secure Shell (SSH) plays a pivotal role. By leveraging SSH, organizations can establish secure and encrypted connections to their IoT devices, mitigating the risk of unauthorized access and data breaches.
With SSH protocols, IoT device management benefits from strong encryption techniques and multi-factor authentication, providing layers of added security essential for protecting sensitive information and maintaining operational safety.
To enhance SSH security for IoT devices, best practices such as disabling password authentication, implementing robust SSH keys, and conducting regular audits of SSH configurations are crucial.
Avoiding Risky IoT Remote Access Practices
To ensure the security of IoT devices, it is essential to avoid risky remote access practices. This includes using strong authentication methods, regularly updating software and firmware, and implementing network segmentation to isolate IoT devices from other systems.
Best Practices for SSH-Driven IoT Remote Access
To ensure the security of IoT devices through SSH, consider these best practices:
- Use Strong Passwords: Create complex and unique passwords for SSH access to prevent unauthorized entry into your IoT devices.
- Implement two-factor authentication (2FA): Enable 2FA to add an extra layer of security, requiring a second form of verification in addition to a password.
- Regularly Update SSH Keys: Periodically rotate or regenerate SSH keys to reduce the risk of unauthorized access and maintain secure connections.
- Monitor SSH Logs: Keep track of SSH logs to detect any suspicious activities or potential security breaches in real time.
- Disable Root Login: Restrict root login access through SSH to minimize the risk of unauthorized privilege escalation.
- Enable Firewall Protection: Use firewalls to control incoming and outgoing network traffic, adding a layer of defense against unauthorized access.
- Limit User Access: Only grant SSH access to authorized users and regularly review user privileges to prevent unauthorized entry.
- Utilize Secure File Transfer Methods: When transferring files over SSH, employ secure protocols such as SFTP (SSH File Transfer Protocol) for encrypted data exchange.
- Regular Security Audits: Perform routine security audits and vulnerability assessments of IoT devices accessible through SSH to identify and address potential risks proactively.
- Educate Users on Best Practices: Provide training and guidelines for users accessing IoT devices via SSH, emphasizing the importance of following secure practices.
Enhancing SSH Security for IoT Devices
To enhance the security of IoT devices, it is crucial to regularly update and patch operating systems, implement multi-factor authentication (MFA), and use cryptographic keys for secure communication.
Curious to know more about how these strategies can be effectively implemented? Keep reading to find out!
Preparing to SSH into an IoT Device
- Ensure that the IoT device is running and connected to a network.
- Verify the IP address or hostname of the IoT device before establishing the SSH connection.
- Check if the SSH service is enabled on the IoT device and configure it if necessary.
- Generate SSH keys for secure authentication between the client and the IoT device.
- Set up port forwarding on the router to allow SSH traffic to reach the IoT device’s local network address.
Troubleshooting SSH Connection Issues
If you’re experiencing issues with your SSH connection to an IoT device, here are some expert tips to troubleshoot and resolve the problem:
- Verify the Correct IP Address: Check that you are using the correct IP address of the IoT device you are attempting to connect to. An incorrect IP address can lead to a connection failure.
- Confirm SSH Service Status: Ensure that the SSH service is running on the IoT device. You can do this by accessing the device through other means or checking its status directly, if possible.
- Check port settings: Verify that your SSH client is using the correct port to connect to the IoT device. The default port for SSH connections is 22, but it could be different based on your specific setup.
- Review firewall settings: Make sure that any firewall or network security settings are not blocking SSH connections. Adjust firewall rules if necessary to allow SSH traffic.
- Validate User Credentials: Double-check that you are using the correct username and password (or private key) for authenticating the SSH connection.
- Diagnose Network Connectivity: Troubleshoot network connectivity issues between your local machine and the IoT device, ensuring no connectivity problems are causing the connection failure.
- Investigate Error Messages: Pay attention to any error messages presented during connection attempts and research their meanings online or in relevant documentation.
- Update Software Versions: Ensure both your local SSH client software and the IoT device’s SSH server software are up-to-date with the latest bug fixes and patches.
- Restart Devices: Sometimes a simple restart of both your local machine and the IoT device can clear up temporary connection issues due to software glitches or memory leaks.
- Seek Community Support: If all else fails, consider seeking help from online forums or communities where experts and other users might have encountered similar problems and found solutions.
Takeaway
That’s everything we have on SSH Control IoT devices. In conclusion, understanding SSH and its role in IoT device control is vital for maintaining security and efficiency. By implementing best practices for SSH-driven remote access to IoT devices, businesses can ensure data confidentiality and mitigate cybersecurity risks.
The importance of careful management and proper configuration for keeping client-server connections private cannot be overstated. Additionally, regular firmware updates are crucial for mitigating operational issues caused by outdated software.
Finally, encouraging proactive measures like effective SSH key management will further enhance the security of IoT remote access.
Frequently Asked Questions (FAQs)
Now, let’s find out some frequently asked questions about SSH Control IoT devices.